application security risk assessment checklist
|
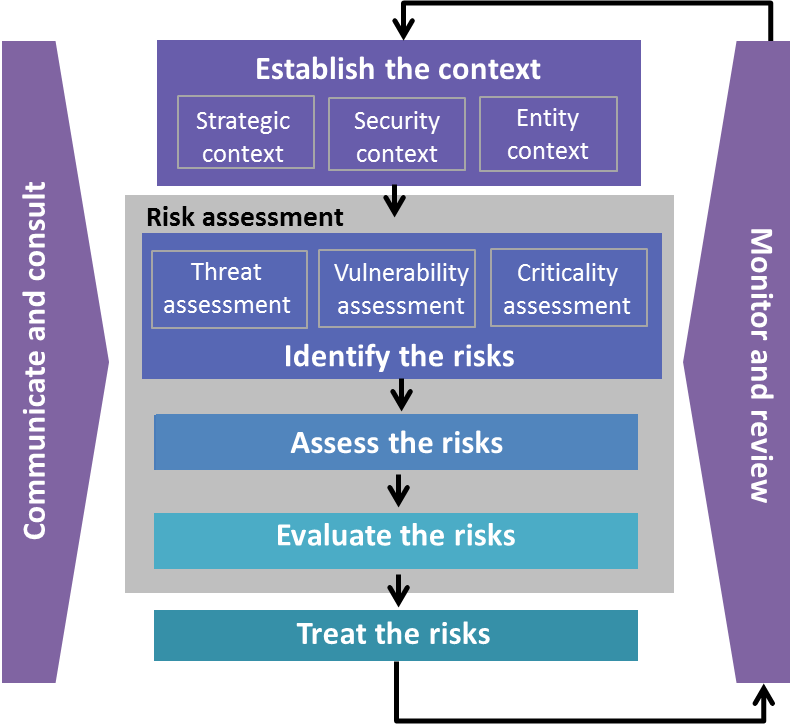
IT Risk Assessment Checklist
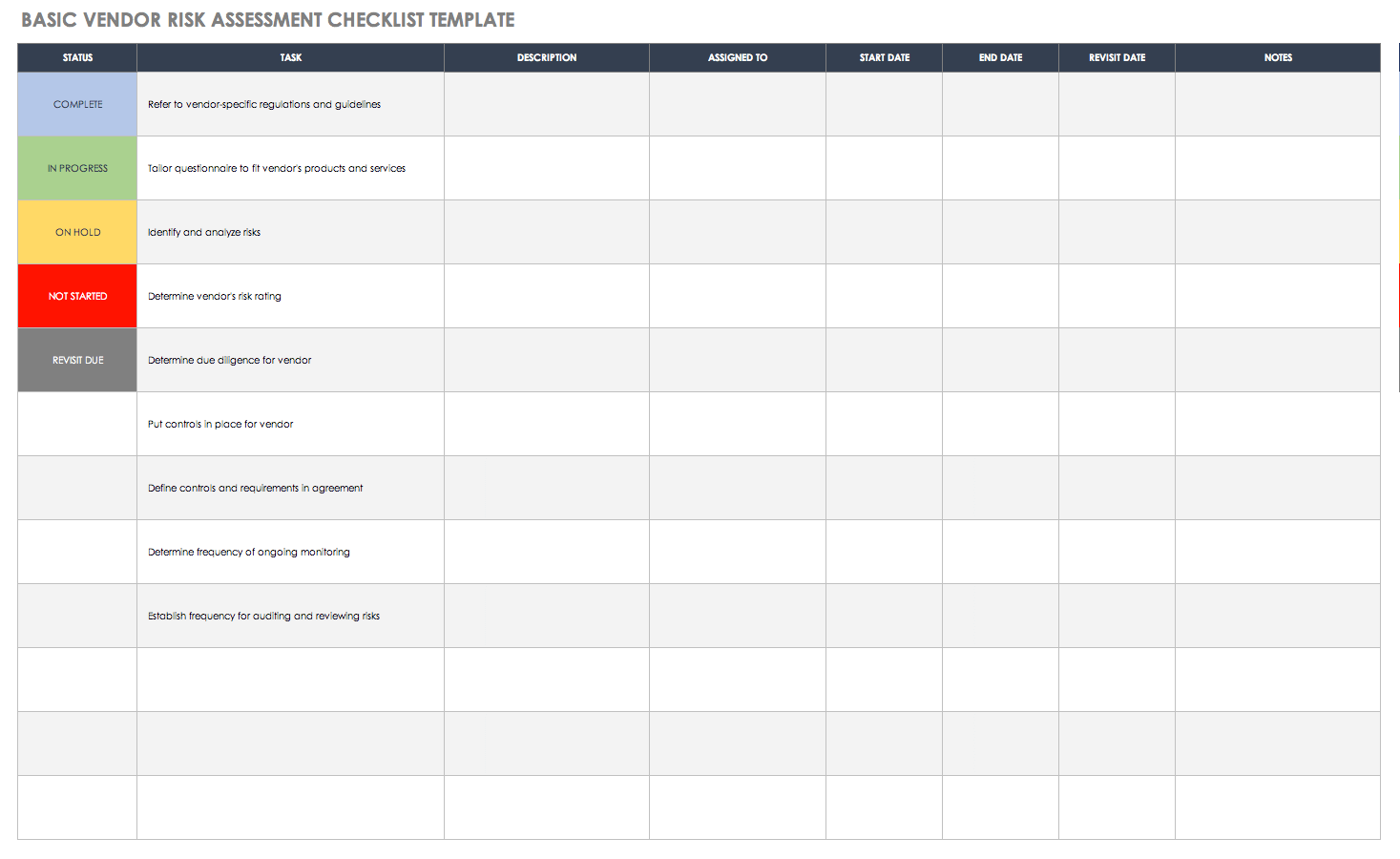
This simple checklist is just one of several tools available to conduct information security risk assessments in your organization Once the step is complete |
|
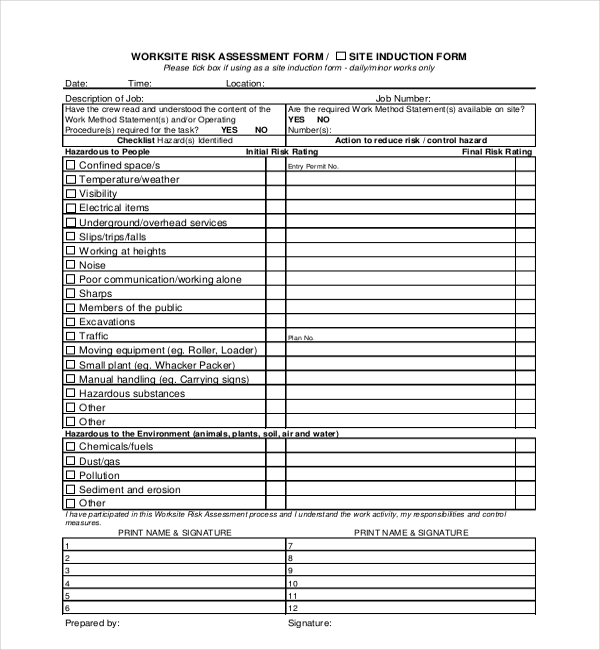
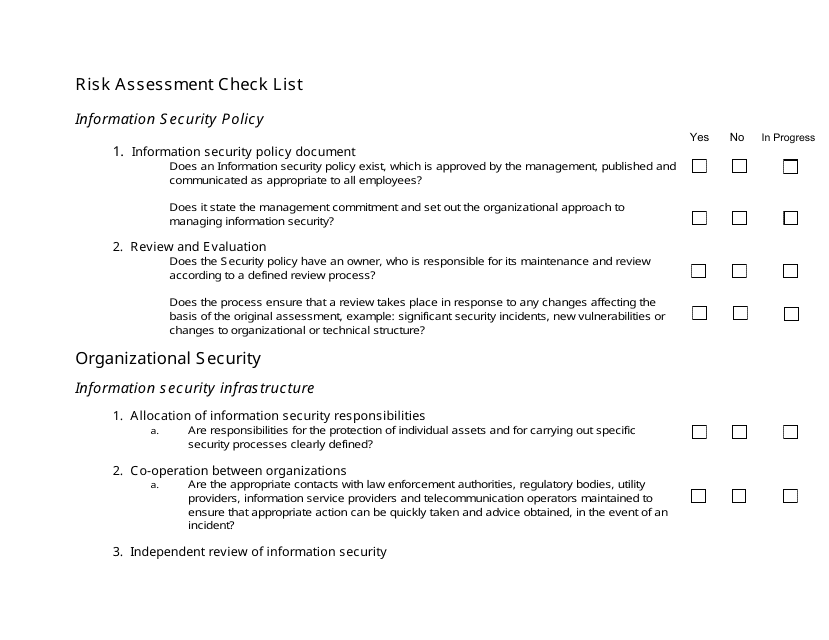
Risk Assessment Check List
Are security risks with third party contractors working onsite identified and appropriate controls implemented? 2 Security requirements in third party |
|
SANS Institute Web Application Security Checklist
This checklist is to be used to audit a web application It is essential that the web application not be evaluated on its own in an e-commerce implementation |
How do you perform an application security risk assessment?
You can identify the hazards that are associated with work operations and assess their risk.
You can control work according to its risk, identify risks in job plans, and assess the risks that are associated with incidents and management of change records.
|
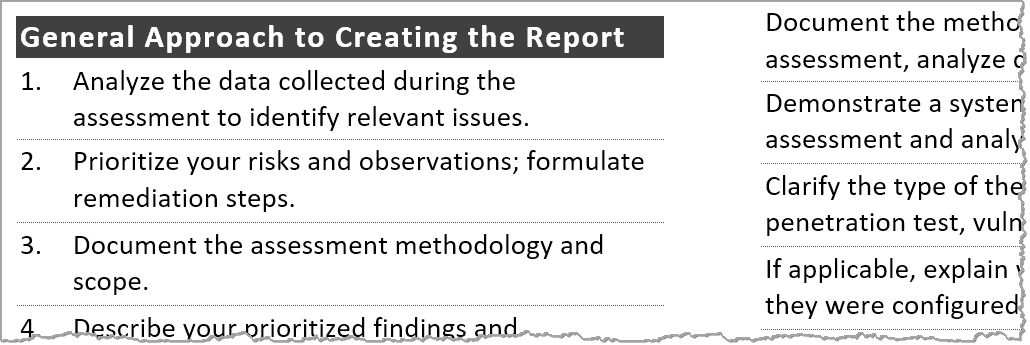
Risk Management Guide for Information Technology Systems
Appendix B—Sample Risk Assessment Report Outline . application and database administrators; computer specialists; security analysts;. |
|
Application Security Questionnaire
Also use the space below to list any other security threats |
|
A Security Checklist for Web Application Design
securing web applications and the databases they connect to from malicious and unintentional abuse. Checklist. Risk Assessment. Authentication. |
|
Owasp-security-checklist-excel.pdf
11 Jun 2020 What is Security Testing Types with. Example Guru99. 1 Application Security Risk Assessment ASRA Workstation or Server App. OWASP Mobile. |
|
OWASP Penetration Testing Check List
OWASP Web Application Penetration Checklist technique to test the security of web applications under certain circumstances. ... Risk Management Guide. |
|
Application Security Verification Standard 4.0 - Final
Assessment and Certification . As a Replacement for Off-the-shelf Secure Coding Checklists . ... As a Driver for Agile Application Security . |
|
Risk Assessment Check List
Is necessary approval obtained from business and application owners? Media handling and Security. 1. Management of removable computer media a. Does a procedure |
|
PCI DSS v3.2.1 Quick Reference Guide
Payment Application Data Security Standard (PA-DSS) 12.2 Implement a risk assessment process that is performed at least annually and upon significant. |
|
SANS Institute Web Application Security Checklist
This checklist is to be used to audit a web application. ensure that appropriate steps have been taken to address the risks posed by. |
|
How to Implement Security Controls for an Information Security
related systems; therefore decisions on the application of security controls have to balance considerations 2.1 Security Controls for Risk Assessment . |
|
Application Security Questionnaire - HIMSS
2 10 Can the application continue normal operation even when security audit application/system used to mitigate the risks associated with malicious code: CCHIT Security Criteria S8 1, S10 S11 (Checklist questions 2 5, 2 9 2 10) 3 |
|
Securing Web Application Technologies (SWAT) CHECKLIST
The SWAT Checklist provides an easy-to-reference set of best practices that raise must be of sufficient length to withstand analysis and prediction CWE-6 a risk review with security professionals and threat model the application to identify |
|
INFORMATION SECURITY CHECKLIST Software Application
Risk Information prior to storing or accessing UBC Electronic Information The application must be hardened and pass vulnerability assessments as described |
|
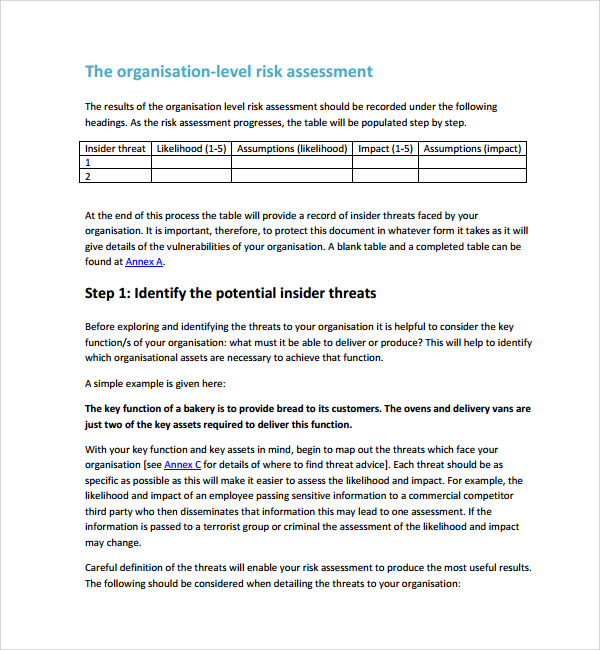
Risk Assessment Checklist - AcqNotes
basis of the original assessment, example: significant security incidents, new Are security risks with third party contractors working onsite identified and appropriate Is necessary approval obtained from business and application owners? |
|
CYBER SECURITY CHECKLIST - Utahgov
This is a simple checklist designed to identify and document the existence and status for a CYBER SECURITY THREAT/VULNERABILITY ASSESSMENT |
|
How to Conduct an Effective IT Security Risk Assessment
Brad focuses his time on Web application security as it applies to global and enterprise IT security risk assessments also enable organ- izations to build up a |
|
Software security checklist for the software life cycle - nobcsucdavis
of a Software Security Assessment Instrument (SSAI) This paper Security Checklist (SSC) for the life cycle It includes the 2) a vulnerability matrix that categorizes vulnerabilities security, to system security and application security as |
|
Web Application Security Assessment Policy - SANS Technology
Emergency Releases – An emergency release will be allowed to forgo security assessments and carry the assumed risk until such time that a proper assessment |
|
It security risk assessment checklist template - Squarespace
IT risk assessments are fundamental to a business' cyber security, preventing apps – applications by untrustworthy sources may gather information without the |



![Facility Security Assessment Checklist [Free Download] Facility Security Assessment Checklist [Free Download]](https://www.pivotpointsecurity.com/wp-content/uploads/2019/04/ISO-27001-Checklist-thumbnail-min.jpg)


![IT Risk Assessment Template: Top 5 [Free Download] IT Risk Assessment Template: Top 5 [Free Download]](https://dmhnzl5mp9mj6.cloudfront.net/security_awsblog/images/OperationsAudtingChecklists_600.gif)




![Vendor Risk Management Audit \u0026 Assessment [Checklist] Vendor Risk Management Audit \u0026 Assessment [Checklist]](https://www.pivotpointsecurity.com/wp-content/uploads/2018/11/ISO-27001-Checklist-XLS-Icon.jpg)