digital signature algorithm
|
Digital Signature Standard (DSS)
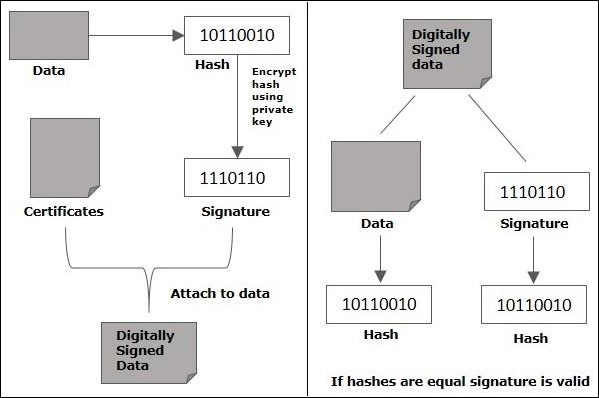
Feb 3 2023 · This standard specifies a suite of algorithms that can be used to generate a digital signature Digital signatures are used to detect unauthorized modifications to data and to authenticate the identity of the signatory |
Which algorithm is used for digital signature?
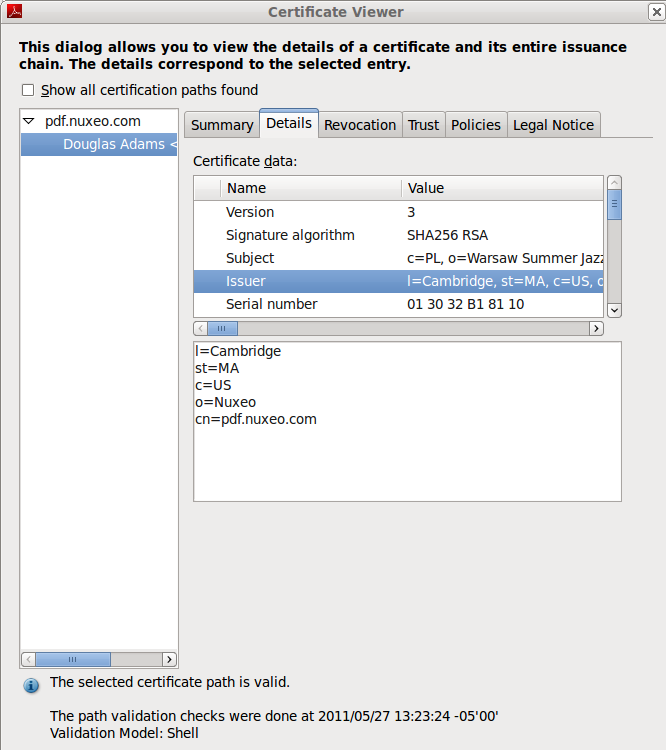
DSA and RSA are both cryptographic algorithms used for digital signatures and encryption.14 fév. 2023
What is the signature signing algorithm?
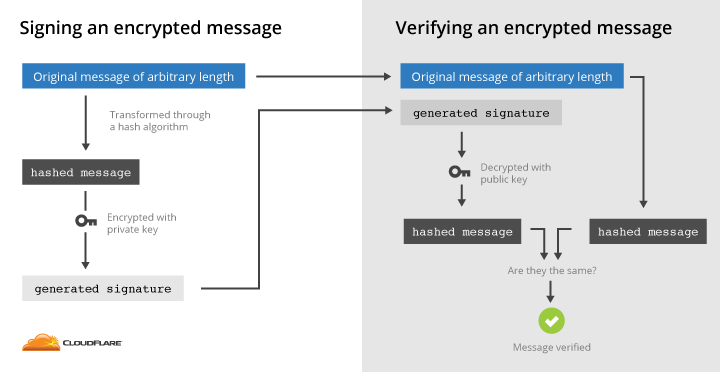
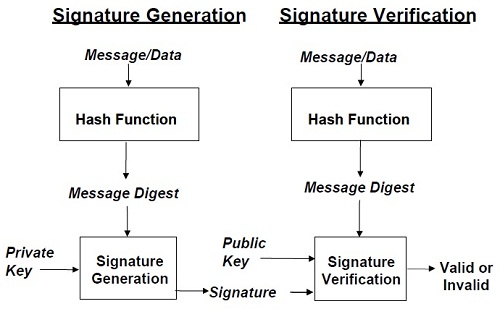
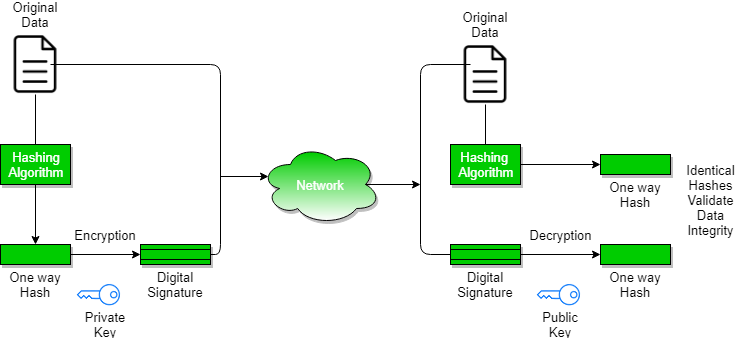
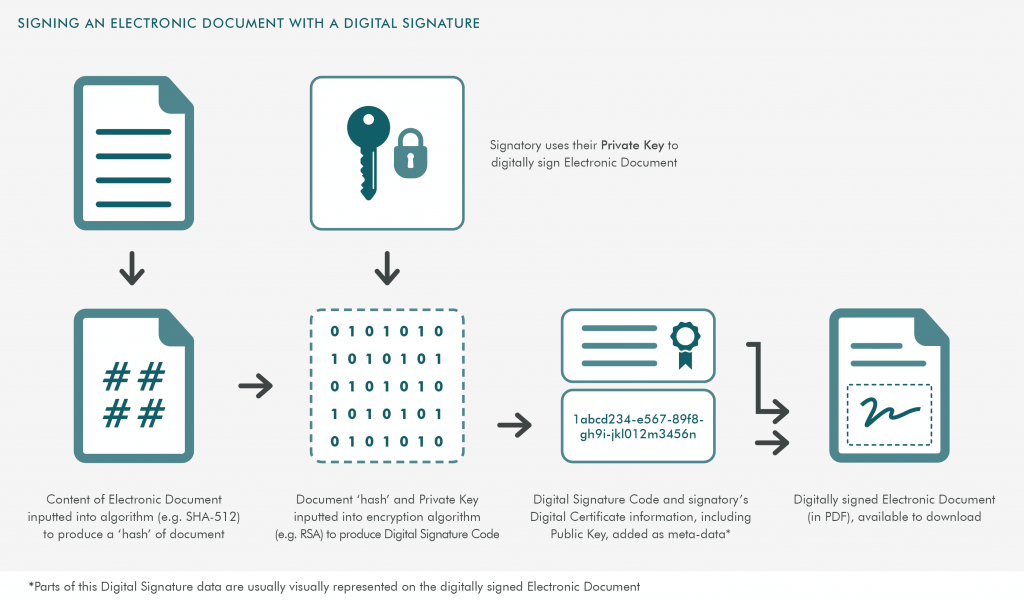
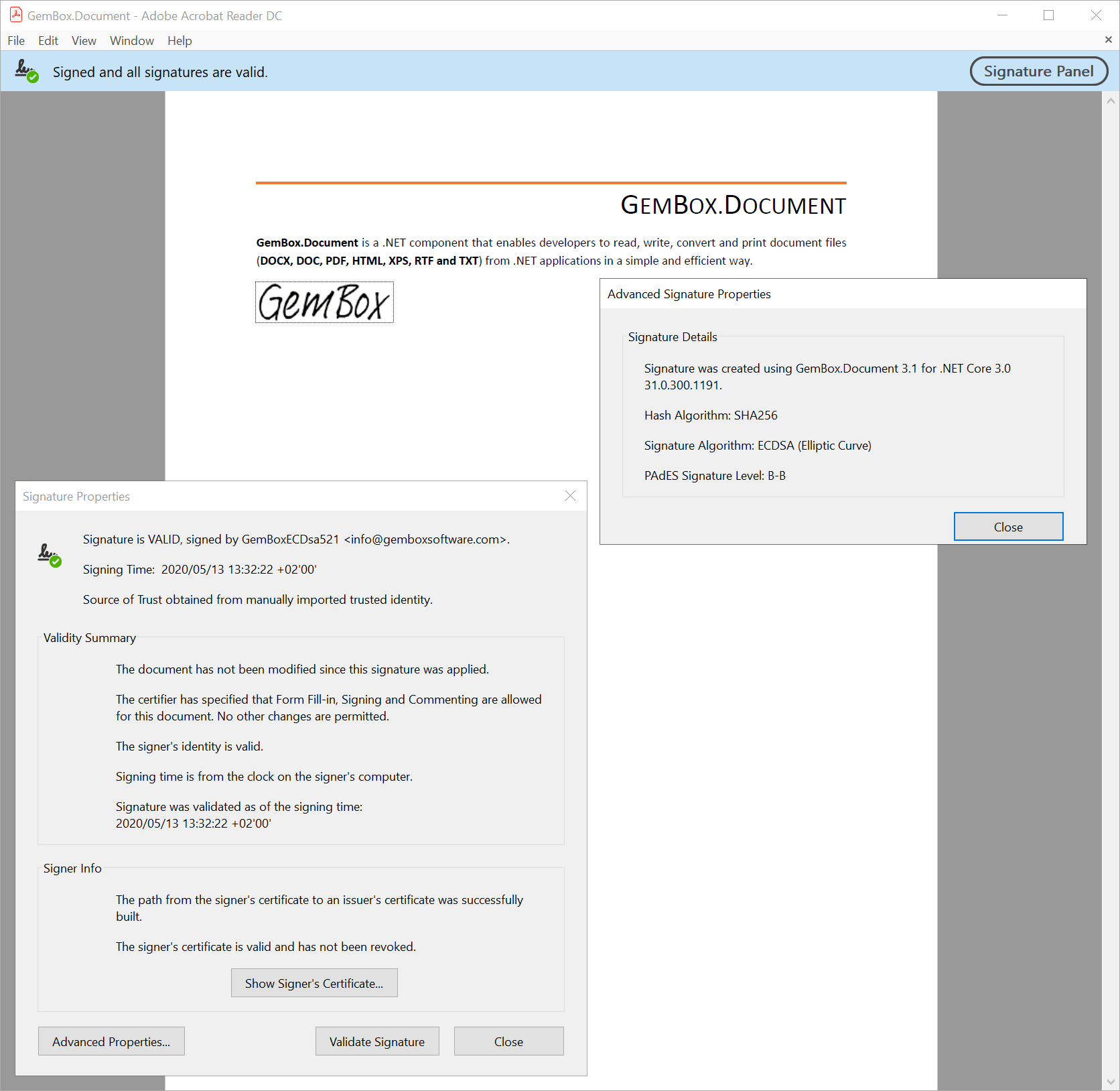
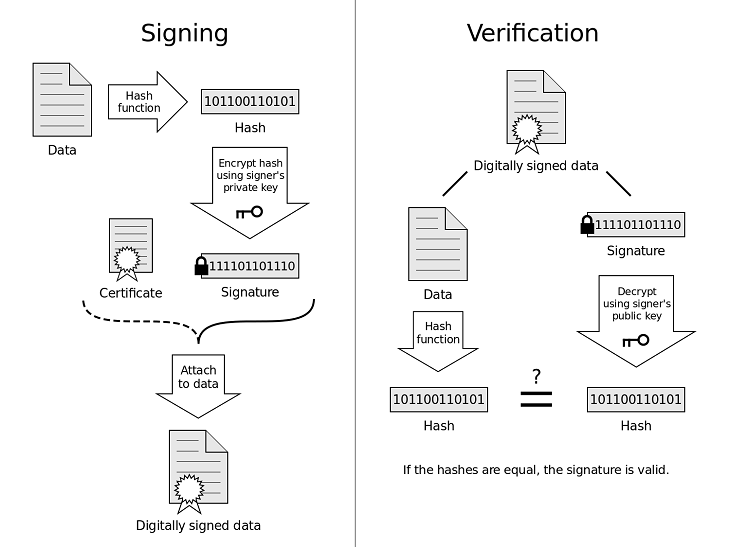
A signing algorithm that, given a message and a private key, produces a signature.
A signature verifying algorithm that, given the message, public key and signature, either accepts or rejects the message's claim to authenticity.Is AES a Digital Signature Algorithm?
The RSA algorithm was used during the process of giving digital signature, while the AES algorithm was used during the process of encoding a message that will be sent to the receiver.
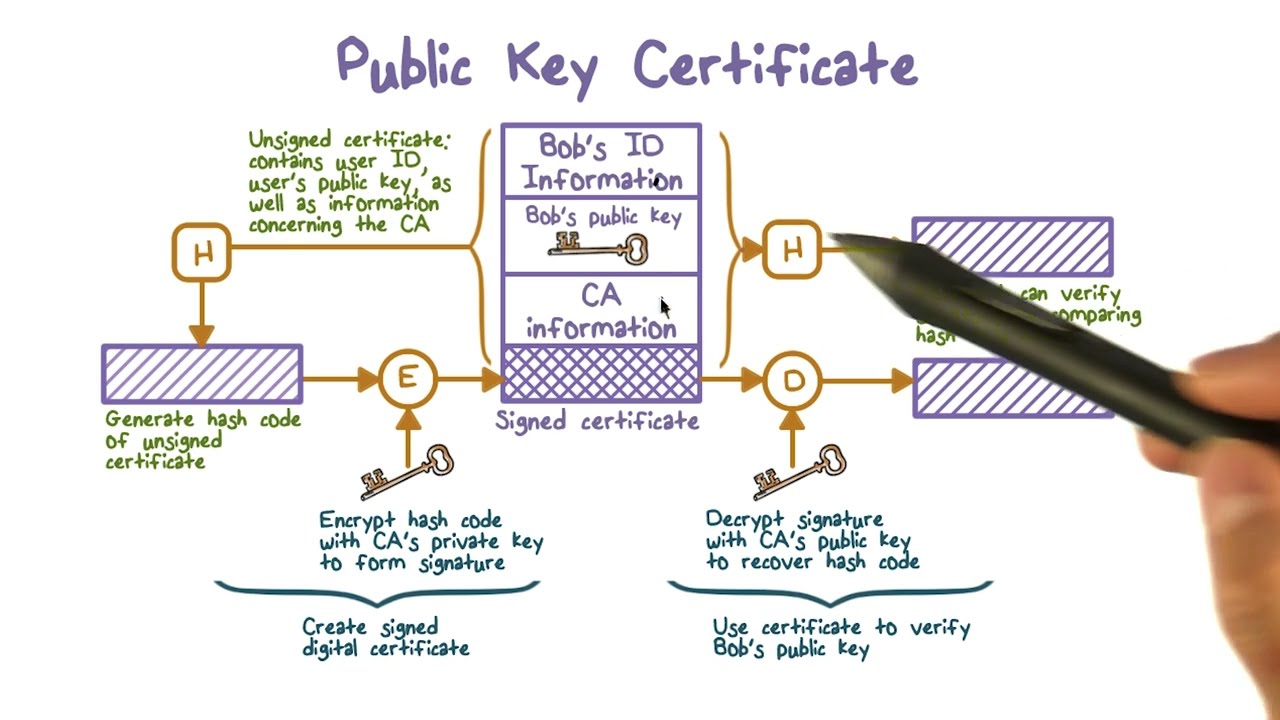
Digital signatures rely on asymmetric cryptography, also known as public key cryptography.
An asymmetric key consists of a public/private key pair.
The private key is used to create a signature, and the corresponding public key is used to verify the signature.

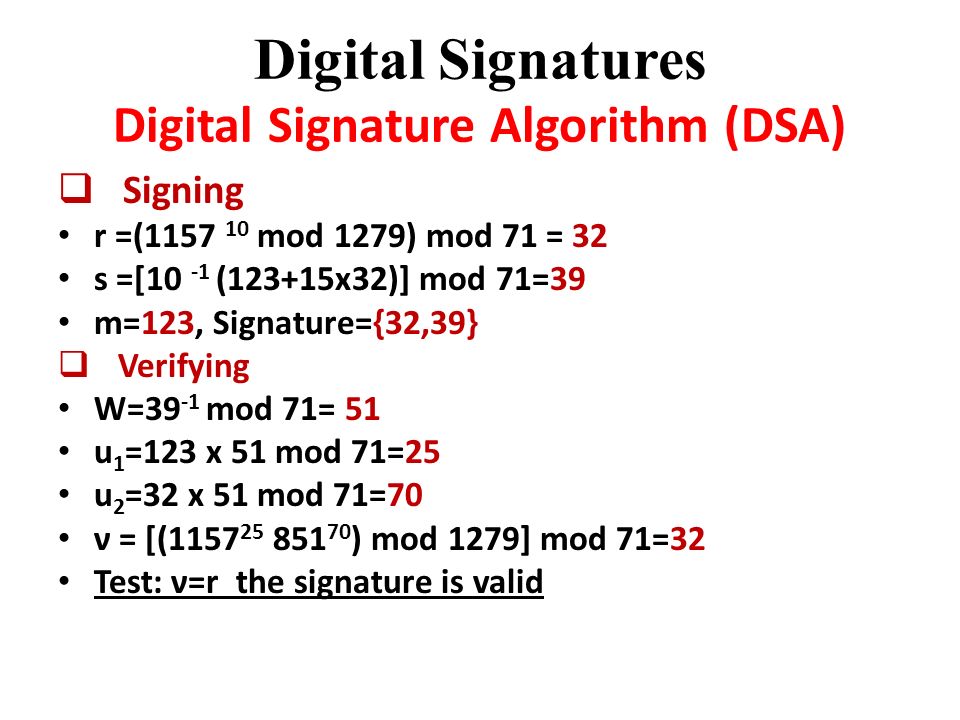
Digital Signature Algorithm (DSA)

DSA Algorithm DSA Algorithm Explained Digital Signature Algorithm Simplilearn

Digital Signature Algorithm (DSA) explained with example
|
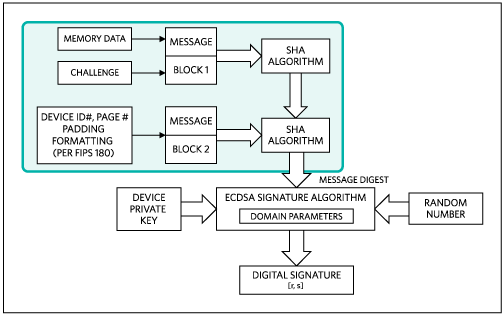
Public key cryptographic algorithm SM2 based on elliptic curves Part 2
This part is applicable to digital signature generation and verification in commercial cryptographic applications. It meets the security requirements of |
|
RFC 9021: Use of the Walnut Digital Signature Algorithm with CBOR
The goal of this publication is to document a way to use the lightweight quantum-resistant. WalnutDSA signature algorithm in COSE in a way that would allow |
|
The Insecurity of the Digital Signature Algorithm with Partially Known
The Digital Signature Algorithm (DSA). Recall the Digital Signature Algorithm (see [26] and [43]) or DSA |
|
WalnutDSATM: A Quantum-Resistant Digital Signature Algorithm
It presents an in-depth discussion of the construction of the digital signature algorithm analyzes the security of the scheme |
|
FIPS 186-3 Digital Signature Standard (DSS)
3 июн. 2009 г. 62-2005 Public Key Cryptography for the Financial Services Industry: The. Elliptic Curve Digital Signature Algorithm (ECDSA). e. ANS X9.80 |
|
Digital Signature Standard (DSS)
3 февр. 2023 г. 62-2005 Public Key Cryptography for the Financial Services Industry: The. Elliptic Curve Digital Signature Algorithm (ECDSA). e. ANS X9.80 |
|
An Electronic Digital Signature Algorithm Based on a Composition of
electronic digital signatures. Key words: algorithm electronic digital signature |
|
The FIPS 186-4 Digital Signature Algorithm Validation System
22 мая 2014 г. ... Digital Signature Algorithm Validation System (DSA2VS) specifies the procedures involved in validating implementations of the Digital Signature. |
|
Electronic Signature Algorithms Standard
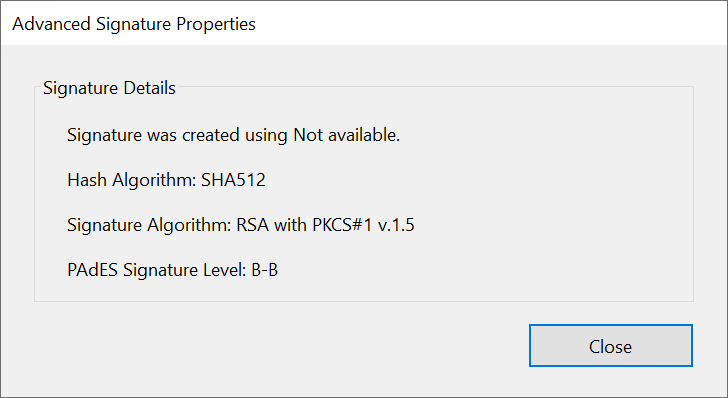
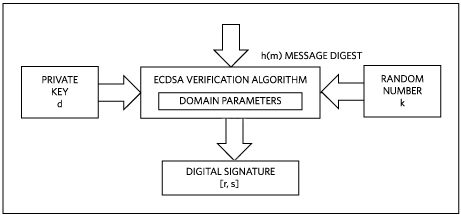
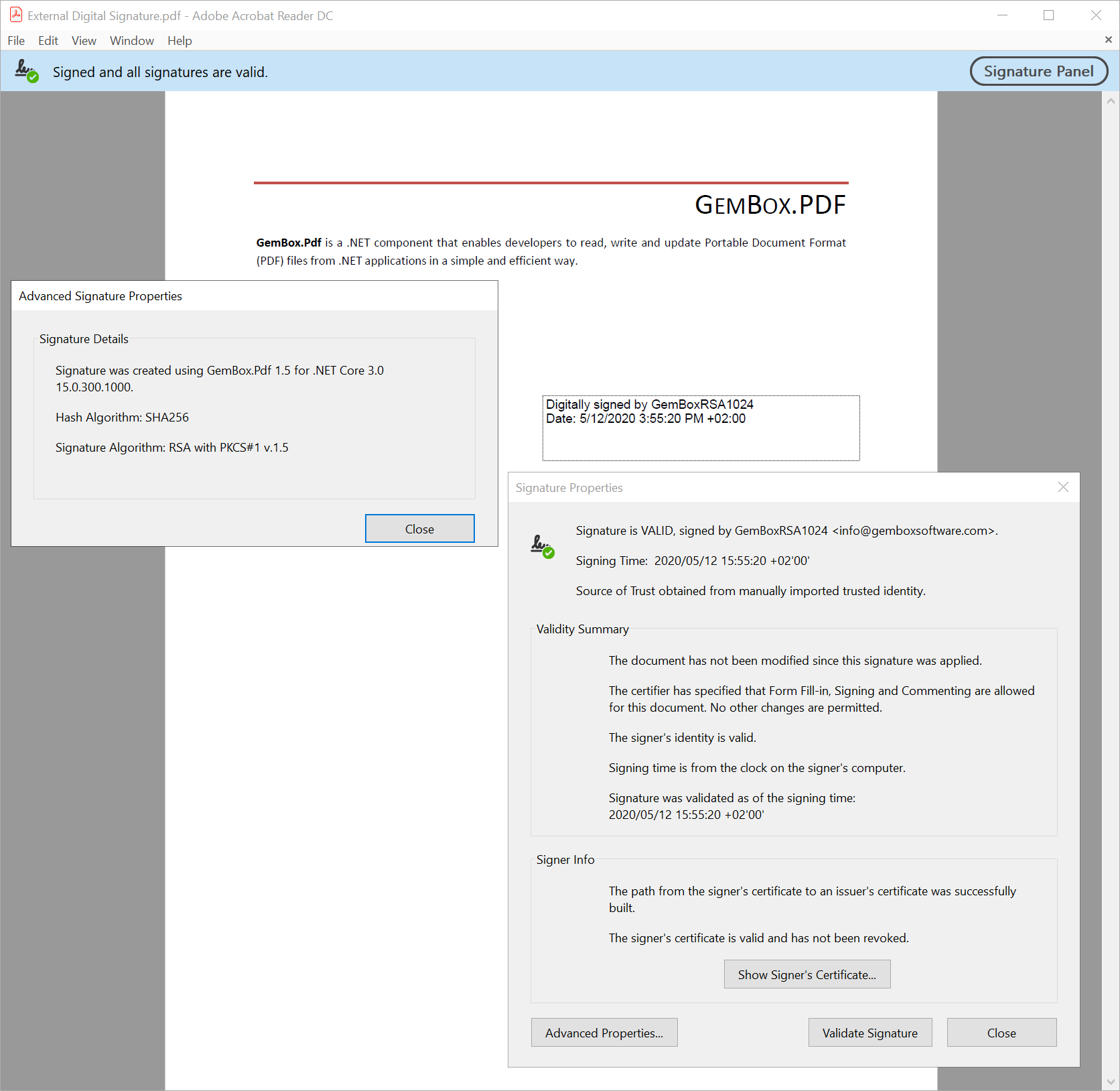
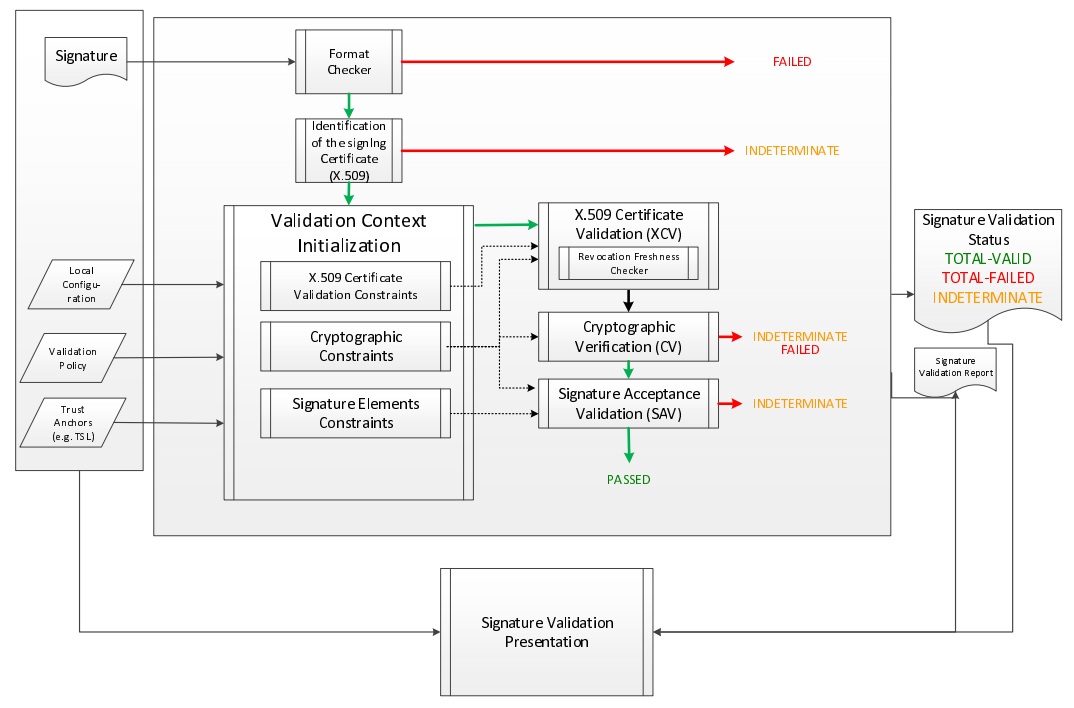
Figure 1: Digital Signature Processes. A digital signature algorithm includes a signature generation process and a signature verification process. A |
|
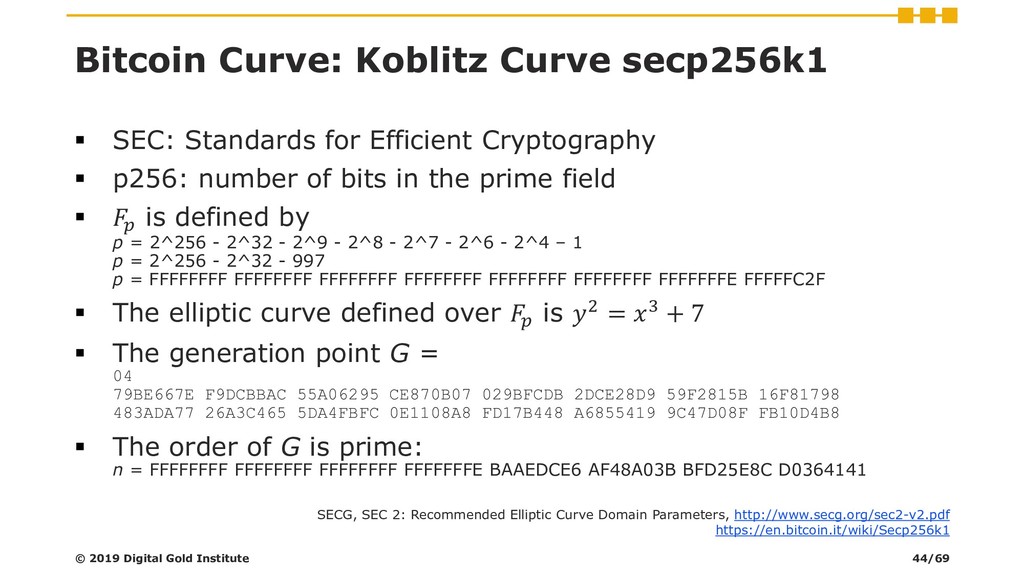
A Secure Multiple Elliptic Curves Digital Signature Algorithm for
Abstract: Most cryptocurrency systems or systems based on blockchain technol- ogy are currently using the elliptic curves digital signature algorithm (ECDSA). |
|
The Elliptic Curve Digital Signature Algorithm (ECDSA)
62 ECDSA and discusses related security |
|
FIPS 186-3 Digital Signature Standard (DSS)
03-Jun-2009 62-2005 Public Key Cryptography for the Financial Services Industry: The. Elliptic Curve Digital Signature Algorithm (ECDSA). e. ANS X9.80 |
|
The FIPS 186-4 Digital Signature Algorithm Validation System
22-May-2014 Digital Signature. Algorithm. The algorithm specified in FIPS 186-4 Digital Signature Standard. (DSS) for generating and verifying digital ... |
|
Overview of TLS v1.3
25-Jan-2018 X509 certificates signed by a mutually trusted third party. ... Digital Signature (Authentication) algorithms: – RSA (PKCS#1 variants). |
|
NEW DIGITAL SIGNATURE ALGORITHM EHT 1. Introduction Digital
11-Mar-2022 converted into a digital signature algorithm. That is quite different in the lattice (code)-based public-key cryptography. |
|
A New Digital Signature Algorithm for Ensuring the Data Integrity in
%20No.%202/18839.pdf |
|
Implementation of Elliptic Curve Digital Signature Algorithm
Digital Signature Algorithm (DSA) Diffie Hellman (DH) and El. Gamal are based on discrete logarithms. The best known method for solving Discrete Logarithm |
|
Electronic Signature Algorithms Standard
Electronic Signature Algorithms. Standard. Version: 1.0. Author: Qatar Public Key Infrastructure Section. Document Classification: PUBLIC. |
|
Implementation of Elliptic Curve Digital Signature Algorithm
Digital Signature Algorithm (DSA) Diffie Hellman (DH) and El. Gamal are based on discrete logarithms. The best known method for solving Discrete Logarithm |
|
Analysis of Digital Signature based Algorithm for Authentication and
The goal of a Digital signature algorithm is to provide security for message or data. The present paper focuses on a comparative study of some existing |
|
Digital Signature Standard (DSS) - NIST Technical Series Publications
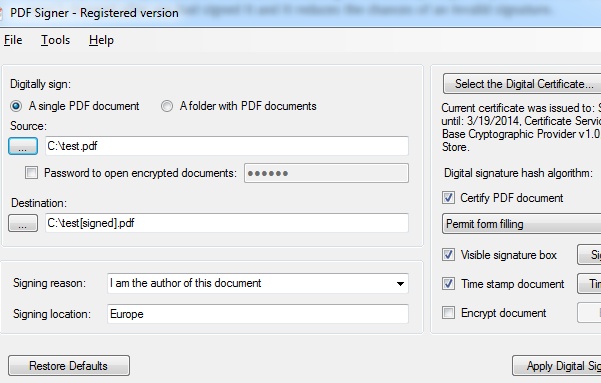
A digital signature algorithm is intended for use in electronic mail, electronic funds transfer, electronic data interchange, software distribution, data storage, and |
|
Digital Signature Algorithm
Digital Signature Algorithm L = 1024 N = 160 Signature: R is 636155AC 9A4633B4 665D179F 9E4117DF 68601F34 S is 6C540B02 D9D4852F |
|
Digital signature algorithm
Public key cryptographic algorithm SM2 based on elliptic curves Part 2: Digital signature algorithm 1 Scope This part of GM/T 0003 specifies the digital |
|
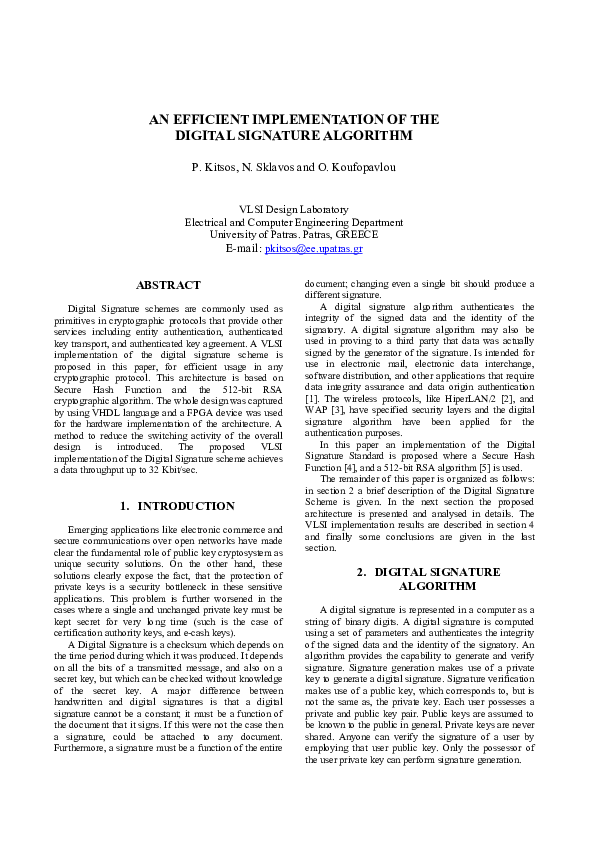
An efficient implementation of the digital signature algorithm
In this paper an implementation of the Digital Signature Standard is proposed where a Secure Hash Function [4], and a 512-bit RSA algorithm [5] is used The |
|
Study of digital signature schemes for gnss signal authentication
For this reason, the strength-per-key- bit is substantially greater in an algorithm that uses elliptic curves Comparision of Elliptic Curve Cryptography One way |
|
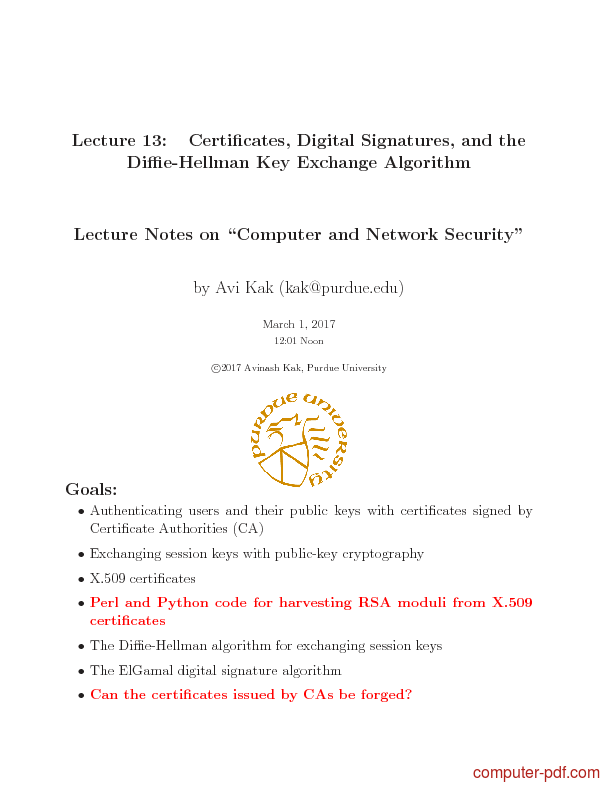
Topic 6: Public Key Encryption and Digital Signatures - Purdue
Concept of digital signature is still originally due to Diffie Most public-key encryption algorithms use either Essentially the same algorithm was discovered |
|
The Elliptic Curve Digital Signature Algorithm (ECDSA) - Computer
62 ECDSA, and discusses related security, implementation, and interoperability issues Page 2 1 Introduction The Digital Signature Algorithm (DSA) was |
|
Analysis of RSA Digital Signature Key Generation using - CORE
Keywords: Private Public key; Strong prime; Gordon's algorithm; Hash Function ; Message Digest; Factorization problem 1 Introduction A digital signature is a |





![PDF] REDUCED TIME COMPLEXITY VARIANT OF DIGITAL SIGNATURE PDF] REDUCED TIME COMPLEXITY VARIANT OF DIGITAL SIGNATURE](https://media.geeksforgeeks.org/wp-content/uploads/20200514170345/Untitled-Diagram-1-11-1.png)










![PDF] Certificates Digital Signatures and the DiffieHellman Key PDF] Certificates Digital Signatures and the DiffieHellman Key](https://image.slidesharecdn.com/ecc-mysoreuniv-sept2011-111001114525-phpapp02/95/mathematics-towards-elliptic-curve-cryptographyby-dr-rsrinivasan-53-728.jpg?cb\u003d1317469649)



![Digital Signature Algorithm - [PDF Document] Digital Signature Algorithm - [PDF Document]](https://helpx.adobe.com/content/dam/help/en/acrobat/kb/SHA1-algorithm-warning-message/_jcr_content/main-pars/image/SHA1-warning-message.png)



![PDF] Fast Implementation of Digital Signature Algorithms On PDF] Fast Implementation of Digital Signature Algorithms On](https://images.slideplayer.com/16/5038421/slides/slide_20.jpg)