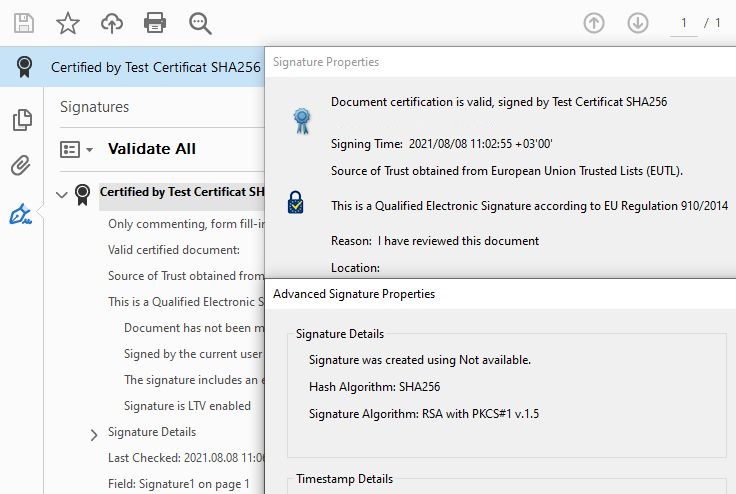
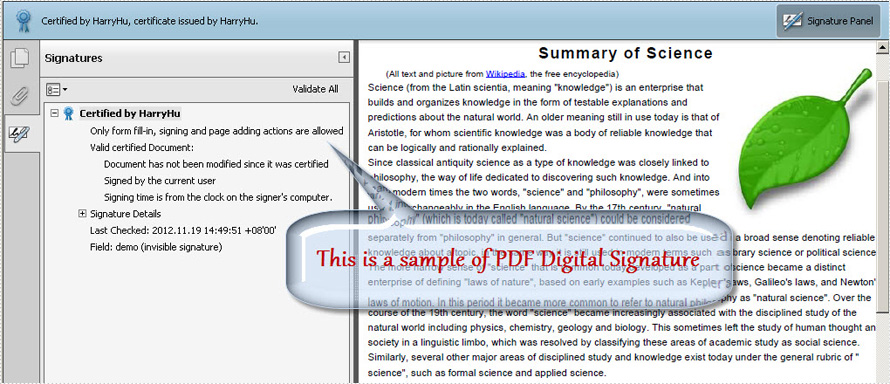
digital signature in cryptography example
How do digital signature schemes work?
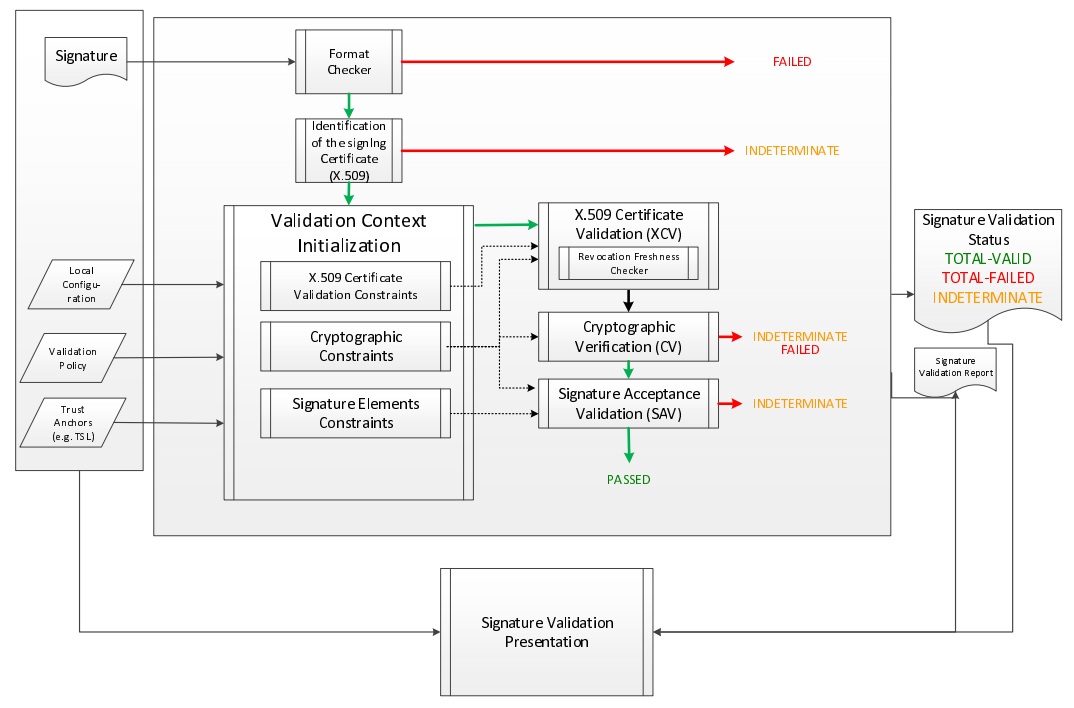
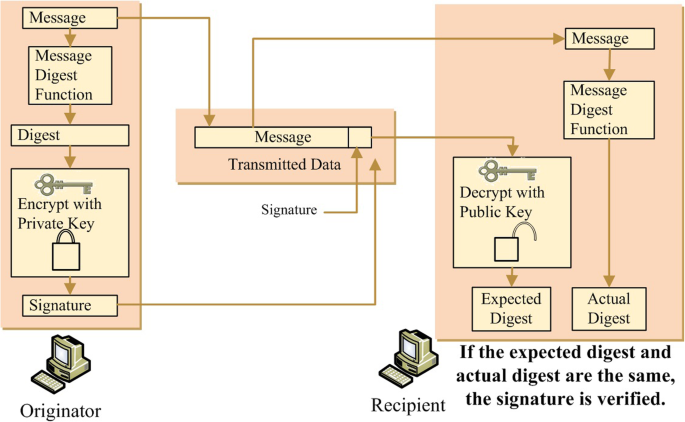
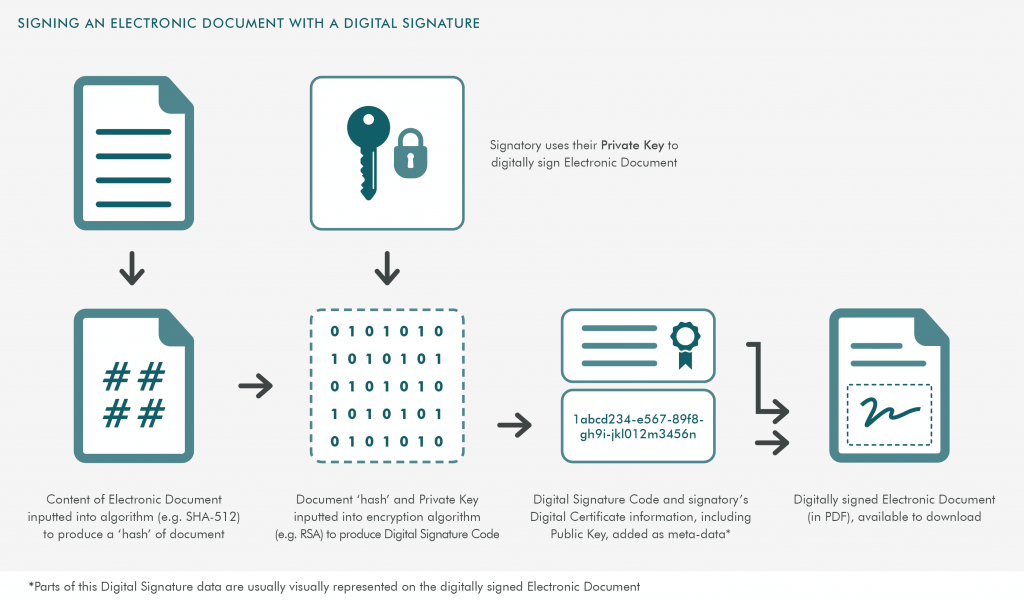
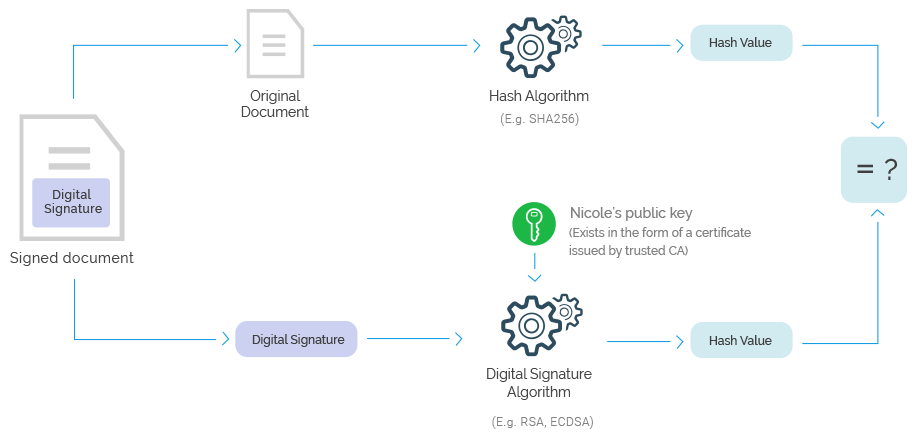
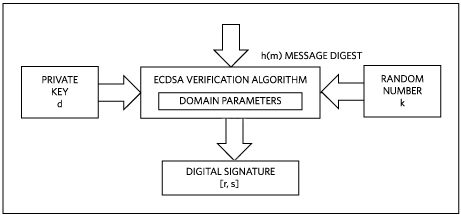
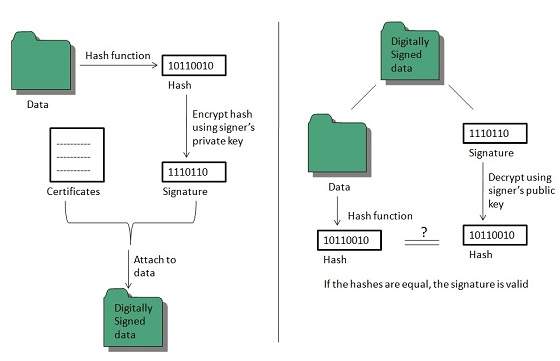
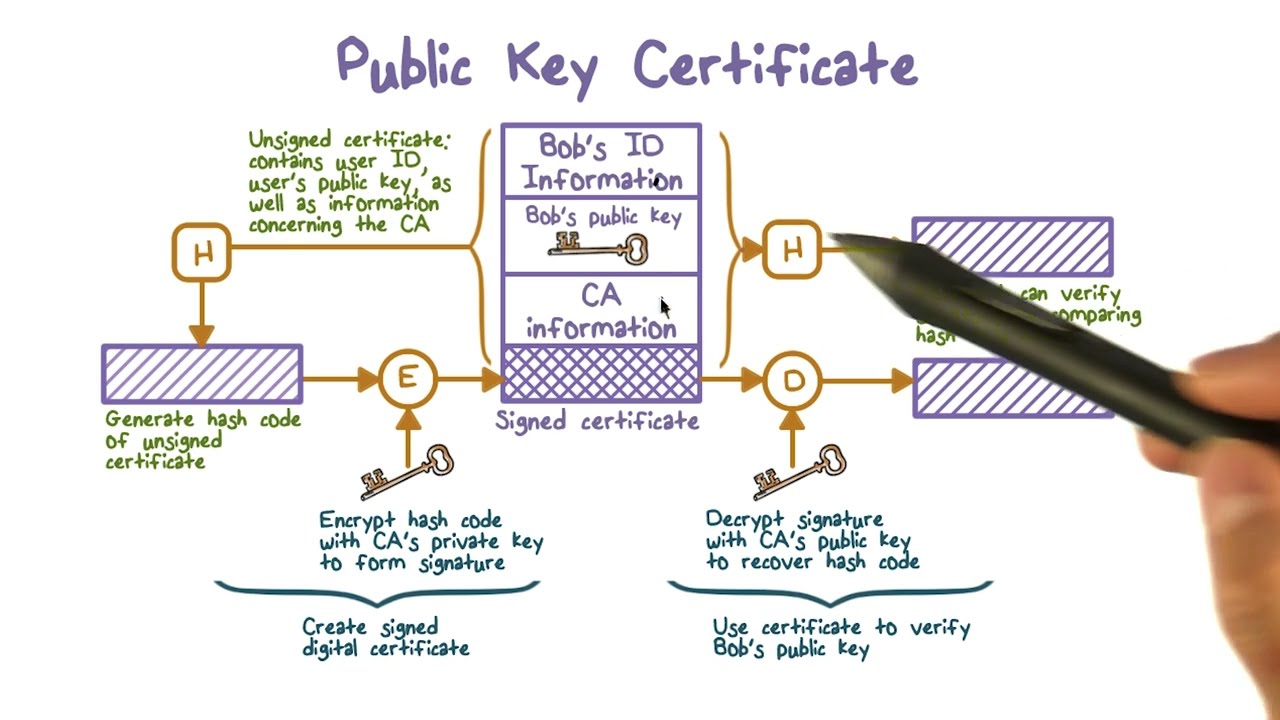
Most signature schemes work like it is shown at the following diagram: At signing, the input message is hashed (either alone, or together with the public key and other input parameters), then some computation (based on elliptic curves, discrete logarithms or other cryptographic primitive) calculates the digital signature.
What algorithms are used in digital signatures?
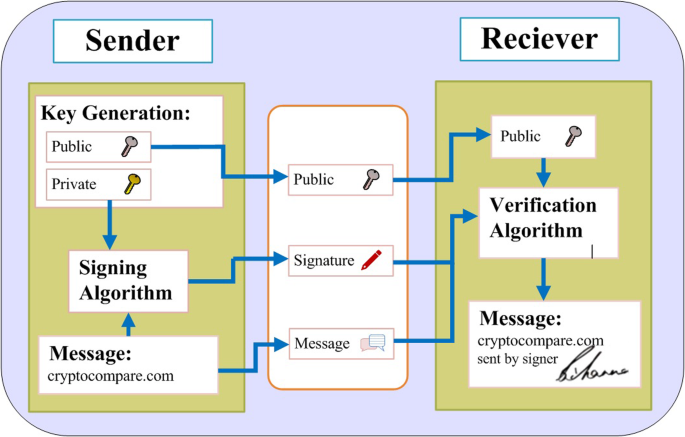
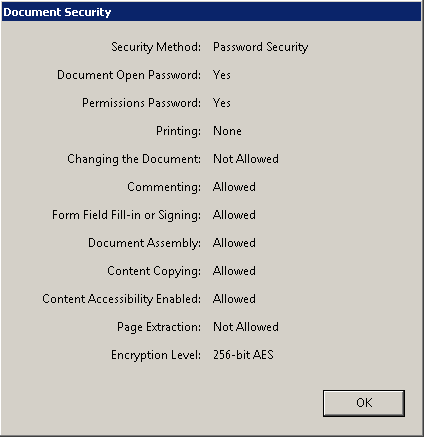
There are three algorithms at work in Digital Signatures. They are as follows: Key Generation Algorithms help ensure authenticity and integrity or it would be very easy to tamper with the data. They also prevent anyone from pretending to be the sender. Signing Algorithms make one-way hashes of the data that has to be signed.
How digital signature uses public key cryptography?
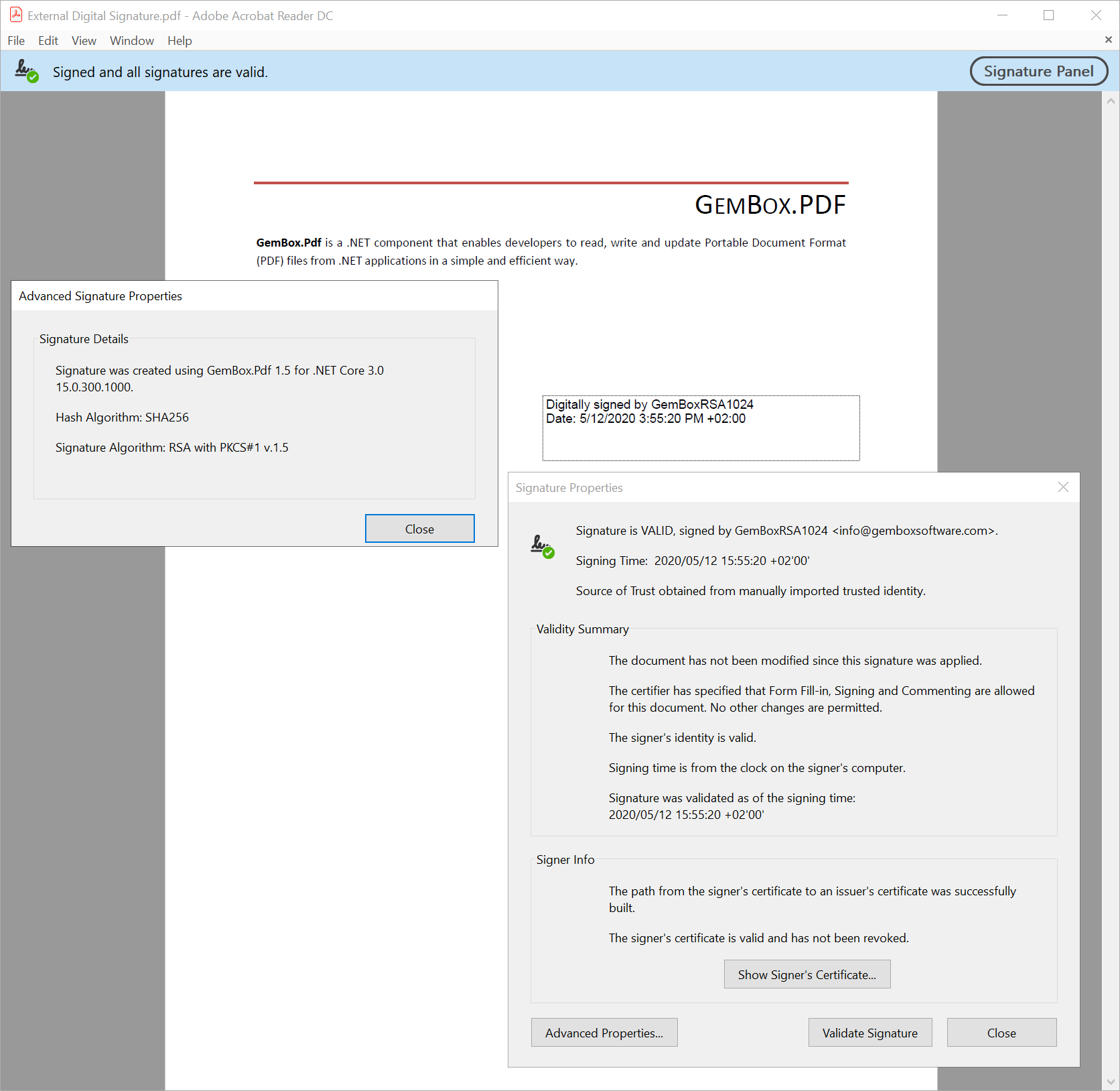
Let’s have a look at how digital signature uses public key cryptography for signing and verification operations. Authentication: When a verifier validates a digital signature using sender’s public key, he is confident that the signature is of the sender with associated secret private key.
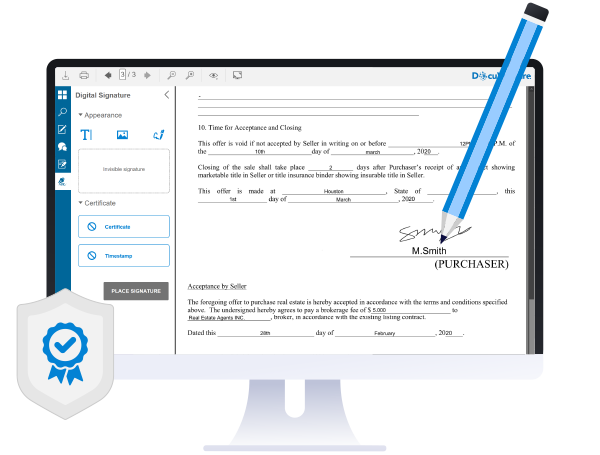
What is an example of a digital signature?
Digitally signed messages may be anything representable as a bitstring: examples include electronic mail, contracts, or a message sent via some other cryptographic protocol. A digital signature scheme typically consists of three algorithms:

2

#37 Digital Signature In Cryptography CNS

Digital Signature Algorithm (DSA)
|
Chapter 22 - Digital Signatures Based on Discrete Logarithms
They are arguably the most important topic in public key cryptography (for example to provide authentication of automatic software updates; see Section 1.1). |
|
FIPS 186-3 Digital Signature Standard (DSS)
3 juin 2009 Key. A parameter used in conjunction with a cryptographic algorithm that determines its operation. Examples applicable to this Standard include:. |
|
Speeding-Up Verification of Digital Signatures
27 sept. 2020 Digital signatures are a cryptographic mechanism used to verify the authen- ... As a first example of a signature scheme with progressive ... |
|
Topic 6: Public Key Encryption and Digital Signatures
Concept of digital signature is still originally due to Diffie. & Hellman Not a Public Key Encryption system but can allow A and B ... RSA Example 2. |
|
Post-quantum algorithms for digital signing in Public Key
30 juin 2017 Support for post-quantum digital signature algorithms in Public Key ... One example is the public-key algorithm RSA which is based on the. |
|
Digital Signature Standard (DSS)
Key words: computer security cryptography |
|
Elliptic Curve Cryptography in Practice
21 oct. 2013 public-key cryptography protocols for example implementing digital signatures and key agree- ment. More than 25 years after their ... |
|
Cryptography Lecture 8 - Digital signatures hash functions
A digital signature should not only be tied to the signing user but also to the message. • The example of encrypting with the private key does this: only. |
|
Strong and provable secure ElGamal type signatures Chapter 16.3
Cryptography. 8. El Gamal Signature example cont. • verify: y. 1 y2 * ?y1 = ? m mod p. 61 * 86 = 211 mod 13. 7 = 7 ? true. • Digital Signature Algorithm |
|
Practical Attacks on Digital Signatures Using MD5 Message Digest
2 déc. 2004 We use the knowledge of the single MD5 collision published by. Wang et al. [2] to show an example of a pair of binary self-extract packages with ... |
|
Topic 6: Public Key Encryption and Digital Signatures - Purdue
Concept of digital signature is still originally due to Diffie Protocol Not a Public Key Encryption system, but can allow A and B Example: Let p=11, g=2, then |
|
Digital Signatures
Elements of applied cryptography A digital signature is a number dependent on An example of bad redundancy function leading to existential forgery |
|
Digital Signatures
Elements of applied cryptography Digital Signatures A digital signature is a number dependent on some secret Examples: RSA, Rabin, Nyberg-Rueppel |
|
Cryptography Lecture 8 - Digital signatures, hash functions
A digital signature should not only be tied to the signing user, but also to the message • The example of encrypting with the private key does this: only Alice can |
|
Digital Signature Schemes
computationally complex There are many Digital Signature Schemes which meet these coordinate to Bob's public encryption exponent e gives the first coordinate Noting that from the definition of s, we have m = sk + ar mod (p-1), we see |
|
Cryptography and Network Security Chapter 13
Cryptography and Network Security Chapter digital signature algorithm and standard Digital Signatures ElGamal Signature Example • use field GF(19) q |
|
Digital Signatures - Centre For Applied Cryptographic Research
(See Definition 11 3 ) 2 Digital signature schemes with message recovery do not require the original message as input to the verification algorithm In this case, |
|
RSA DIGITAL SIGNATURE SCHEME
encryption), a digital signature s is computed on a message m ferred to as an RSA digital signature scheme as it is a good example of the modern design of |
|
Digital Signature Standard (DSS) - NIST Technical Series Publications
Key words: computer security, cryptography, digital signatures, Federal signature algorithm are available at http://csrc nist gov/groups/ST/toolkit/ examples html |
|
What is a digital signature? - Applied Cryptography Group
A more realistic example software update Software vendor clients secret signing key (sk) sig signing algorithm verify sig, install if valid pk pk untrusted hosting |