elicitation insider threat
|
US Department of Justice Federal Bureau of Investigation
Understanding the techniques and the threat may help you detect and deflect elicitation attempts disguise deniable and effective The conversation can be in person over the phone or in |
|
ELICITATION
Elicitation is a structured method of communication used to extract predetermined information from people without making them aware that they are a collection target Elicitation comes in many forms Communications can be verbal or written |
What is insider threat?
In this lesson, you will learn about the definition of insiders, insider threat, and its categories. Narration: It’s very rare that an individual wakes up with the intention of betraying their company, harming their colleagues, or compromising national security. Research has consistently shown that malicious acts by insiders are seldom impulsive.
Why do we need a new counterintelligence & security threat?
These threats present new counterintelligence and security challenges in protecting classified and proprietary information from unauthorized access or improper use by a trusted insider. Thanks to rapid advances in technology, the world is more interconnected than ever before.
What is an elicitation attempt?
It is usually non-threatening, easy to E a specific purpose: collect information that is not readily available and do so without The strategic use of conversation to extract information from people without giving them the feeling they are being interrogated. Elicitation attempts can be simple, and sometimes are obvious.
What role do you play in Insider Threat Mitigation?
Narration: Each of us plays a vital role in insider threat mitigation. We have a duty to protect our company’s information, our colleagues, and our facilities. It is our collective responsibility to protect the classified or proprietary information with which we've been entrusted. Each of us plays a vital role in insider threat mitigation.

Understanding The Insider Threat Video

Finding and Detecting Insider Threats and Advanced Persistent Threats

How to Detect Insider Threats
|
Insider Threat Awareness (INT101) Student Guide
Recognize insider threat counterintelligence |
|
Insider Threat Awareness - Lesson
4 déc. 2020 Recognize insider threat counterintelligence |
|
INSIDER THREAT AWARENESS
22 déc. 2017 “Insider threat” is the term used for the potential harm that may ... Foreign intelligence officers are trained in elicitation tactics. |
|
Student Guide - Insider Threat Awareness
insiders -- people with access to information who unknowingly reveal more than information electronically or they may use elicitation as a technique to ... |
|
Foreign Collection Methods: Indicators and Countermeasures
Insider Threat . Thwarting the Enemy: Providing Counterintelligence and Threat Awareness to the Defense ... Brief employees on elicitation methods. |
|
STUDENT GUIDE COUNTERINTELLIGENCE AWARENESS AND
threat: • Request training on the insider threat. • Attend briefings on elicitation methods. • Be alert to actions of other employees. |
|
Untitled
CI & INSIDER THREAT You do not have to intend harm to create a threat. ... social media sites using elicitation |
|
FBI
an introduction to elicitation and elicitation techniques. Understanding the techniques and the threat may help you detect and deflect elicitation attempts. |
|
Insider Threat Awareness Training Resources
(Elicitation). ? Identify Reportable Behaviors / Indicators Of Malicious Insiders threats. ? Understand Counterintelligence And Security Reporting |
|
The Insider Threat and Its Indicators
procedures or clever elicitation collection techniques. Keep in mind that not all insider threats exhibit all of these behaviors and not all instances ... |
|
Insider Threat Awareness (INT101) Student Guide - CDSE
The National Insider Threat Task Force (NITTF) defines an “insider threat” as: The threat that an insider will use his or her authorized access, wittingly or unwittingly, to do harm to the security of the United States |
|
Best Practices for Mitigating and Investigating Insider Threats
Identify and discover all content inside your network that represents risk Effective insider threat management requires an organization to locate and classify its |
|
The Insider Threat and Its Indicators - NATIONAL INSIDER THREAT
For the purposes of the NISPOM, insider threat refers to the threat of an insider using his or her authorized access, wittingly or unwittingly, to do harm to the |
|
Insider Threat Awareness Training Resources - NATIONAL INSIDER
(Elicitation) ▫ Identify Reportable Behaviors / Indicators Of Malicious Insiders threats ▫ Understand Counterintelligence And Security Reporting Requirements |
|
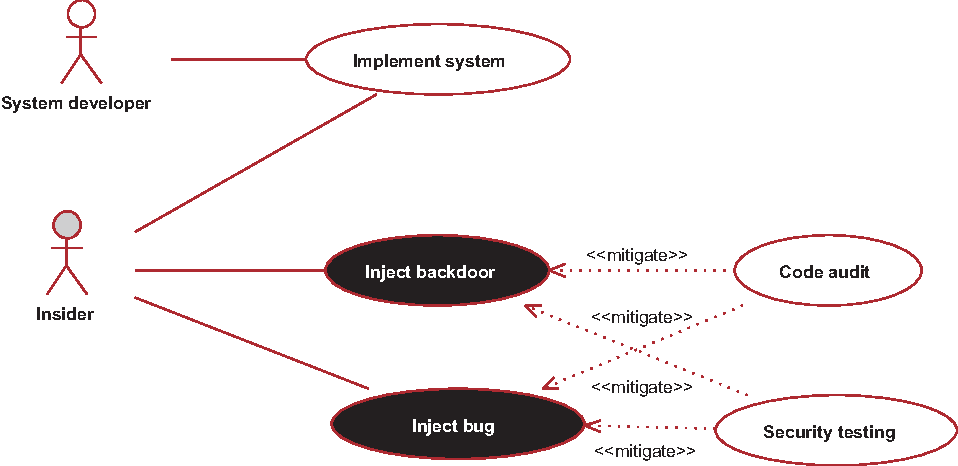
Defense against Insider Threat: a Framework for Gathering Goal
Third, by a list of defense strategies which helps on the elicitation of requirements The output of the method consists of goal-based require- ments for the defense |
|
Counterintelligence Slides
CI INSIDER THREAT AWARENESS ME You do not have to intend harm to create a threat social media sites, using elicitation, and eavesdropping 1 800 |
|
IMS Insider Threat Awareness Briefing Facilitation Guide
Insider Threat Awareness Materials: Insider Threat Posters: https://www cdse edu/resources/posters-insider-threat html Signs of recruitment or elicitation |
|
COUNTERINTELLIGENCE - Lockheed Martin
methods and tactics, concepts related to the Insider Threat, and employee countermeasures Elicitation (collection during seemingly innocent conversation)* |








![Elicitation Brochure - [PDF Document] Elicitation Brochure - [PDF Document]](https://i1.rgstatic.net/publication/282550435_Automated_Insider_Threat_Detection_System_Using_User_and_Role-Based_Profile_Assessment/links/5f8e1dd7a6fdccfd7b6e8195/largepreview.png)







![PDF-Download]-Data-Flow-Diagrams---Simply-Put!:-Process-Modeling PDF-Download]-Data-Flow-Diagrams---Simply-Put!:-Process-Modeling](https://reader015.staticloud.net/reader015/html5/20180728/577cca211a28aba711a57163/bg2.png)
![Elicitation Brochure - [PDF Document] Elicitation Brochure - [PDF Document]](https://d3i71xaburhd42.cloudfront.net/b611114e9e6f211c154678cfd758a8f8ebc69551/6-Figure3-1.png)
![PDF] An extended misuse case notation: Including vulnerabilities PDF] An extended misuse case notation: Including vulnerabilities](https://i1.rgstatic.net/publication/227069899_Monitoring_Technologies_for_Mitigating_Insider_Threats/links/0fcfd50747158e72e7000000/largepreview.png)

![PDF] The CERT Guide to Insider Threats: How to Prevent Detect PDF] The CERT Guide to Insider Threats: How to Prevent Detect](https://www.frontiersin.org/files/MyHome%20Article%20Library/439045/439045_Thumb_400.jpg)
![PDF] An extended misuse case notation: Including vulnerabilities PDF] An extended misuse case notation: Including vulnerabilities](https://onlinelibrary.wiley.com/cms/asset/a060ab32-18af-43db-9d57-15e4c4ae3c73/risa13687-fig-0008-m.jpg)


![PDF] An extended misuse case notation: Including vulnerabilities PDF] An extended misuse case notation: Including vulnerabilities](https://media.springernature.com/original/springer-static/image/chp%3A10.1007%2F978-3-030-44711-3_4/MediaObjects/491525_1_En_4_Fig2_HTML.png)


![PDF] The CERT Guide to Insider Threats: How to Prevent Detect PDF] The CERT Guide to Insider Threats: How to Prevent Detect](https://0.academia-photos.com/attachment_thumbnails/41975089/mini_magick20190218-770-d7nk69.png?1550506563)


![PDF] An extended misuse case notation: Including vulnerabilities PDF] An extended misuse case notation: Including vulnerabilities](https://ars.els-cdn.com/content/image/1-s2.0-S016740482030184X-gr2.jpg)





![PDF] The CERT Guide to Insider Threats: How to Prevent Detect PDF] The CERT Guide to Insider Threats: How to Prevent Detect](https://media.springernature.com/lw685/springer-static/image/art%3A10.1007%2Fs00766-010-0115-7/MediaObjects/766_2010_115_Fig9_HTML.gif)