graph theory applications in network security
|
Graph Theory Applications in Network Security 1 INTRODUCTION 2
Graph theory has become a very critical component in many applications in the computing field including networking and security. Unfortunately it is also |
|
Scenario Graphs Applied to Network Security
Through a detailed concrete example we show how we can model a computer network and generate and analyze attack graphs automatically. The attack graph we |
|
Applied graph theory to security: A qualitative placement of security
23 ????. 2020 ?. Abstract. The rise of edge computing enables local network management. Services are no longer clustered inside the cloud but rather spread ... |
|
Connections between graph theory and cryptography
We consider such topics as: • sparse graphs social networks and mobile security systems;. • hash functions |
|
Synthesis of Patterned Media by self-assembly of magnetic
applications of the graph theory in the field of network security and the second is focused on the possibility of using the Euler graph as a Method Object |
|
Applied graph theory to security: A qualitative placement of security
25 ??? 2021 ?. Abstract. The rise of edge computing enables local network management. Services are no longer clustered inside the cloud but rather spread ... |
|
Applied graph theory to security: A qualitative placement of security
25 ??? 2021 ?. Section 3 provides an abstract methodology for qualitative positioning of edge computing security services on IoT networks. Section 4 outlines ... |
|
A NOVEL APPROACH OF MOBILE SECURITY ROBOTICS MOVED
31 ???. 2018 ?. Webb and et al have reviewed the significant key application of graph theory applications in wire and wireless networks security [12]. Algorithm. |
|
Retracted: Selection of intermediate routes for secure data
9 ???. 2020 ?. systems using graph theory application and grey wolf ... ture stringent energy resources and network security issues. |
| An approach for network security with graph coloring problem |
|
Graph Theory Applications in Network Security - arXiv
16 nov 2015 · In this paper we explore applications of graph theory in cellular networks with an emphasis on the 'four-color' theorem and network coding and |
|
Graph Theory Applications in Network Security - Academiaedu
We first cover some algorithmic aspects then present network coding and its relation to routing See Full PDF Download PDF See Full PDF |
|
A Study of Graph Theory Applications in IT Security - ResearchGate
2 fév 2021 · This study focused on two parts; the first is to review the most important applications of the graph theory in the field of network security |
|
Graph Theory Applications in Network Security - ResearchGate
5 mar 2023 · Graph theory has become a very critical component in many applications in the computing field including networking and security |
|
Graph Theory Applications in Network Security
13 juil 2017 · In this paper we review some of the key applications of graph theory in network security We first cover some algorithmic aspects then present |
|
Scenario Graphs Applied to Network Security
Through a detailed concrete example we show how we can model a computer network and generate and analyze attack graphs automatically The attack graph we |
|
Graph Theory Applications in Network Security - Semantic Scholar
15 nov 2015 · Some of the key applications of graph theory in network security are reviewed followed by some algorithmic aspects then network coding and |
|
Graph Theory Applications in Network Security - PDF Free Download
Graph Theory Applications in Network Security Jonathan Webb1 Fernando Docemmilli2 and Mikhail Bonin3 Theory Lab - Central Queensland University Wayville |
|
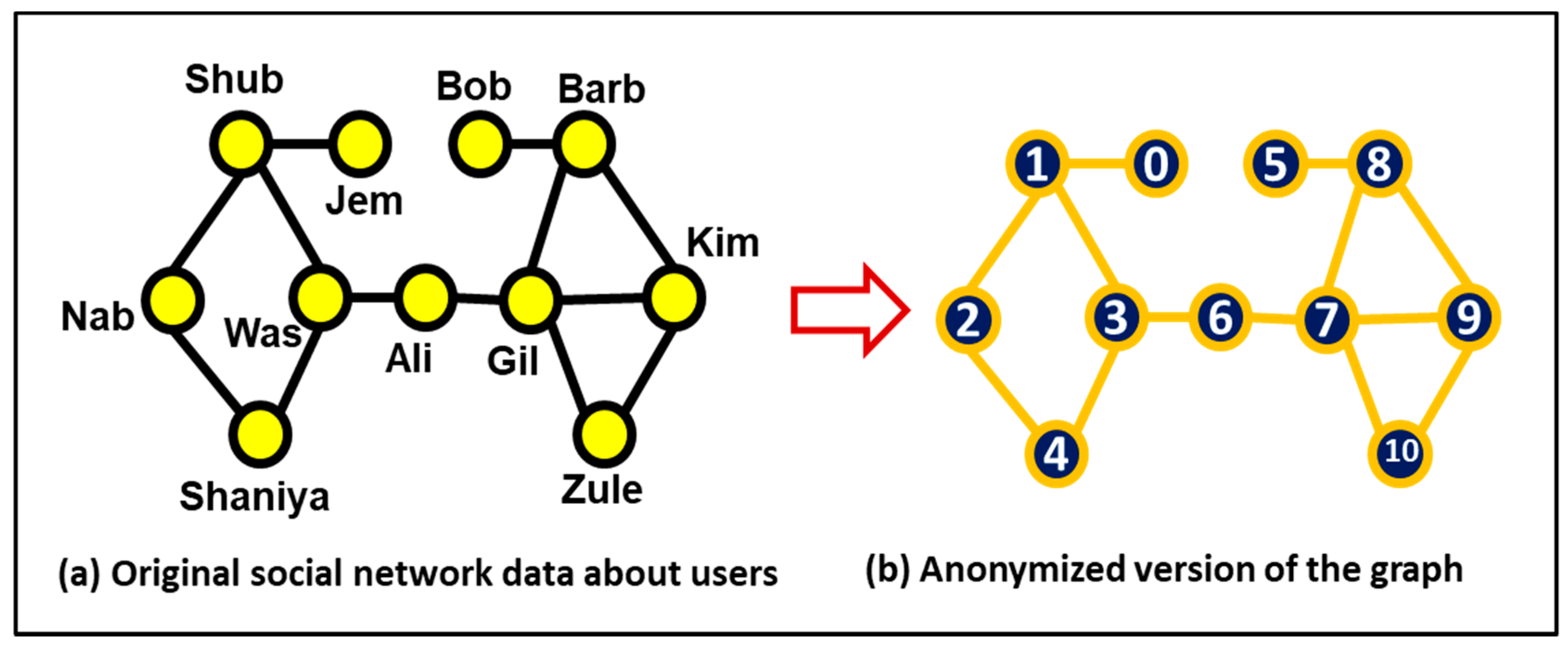
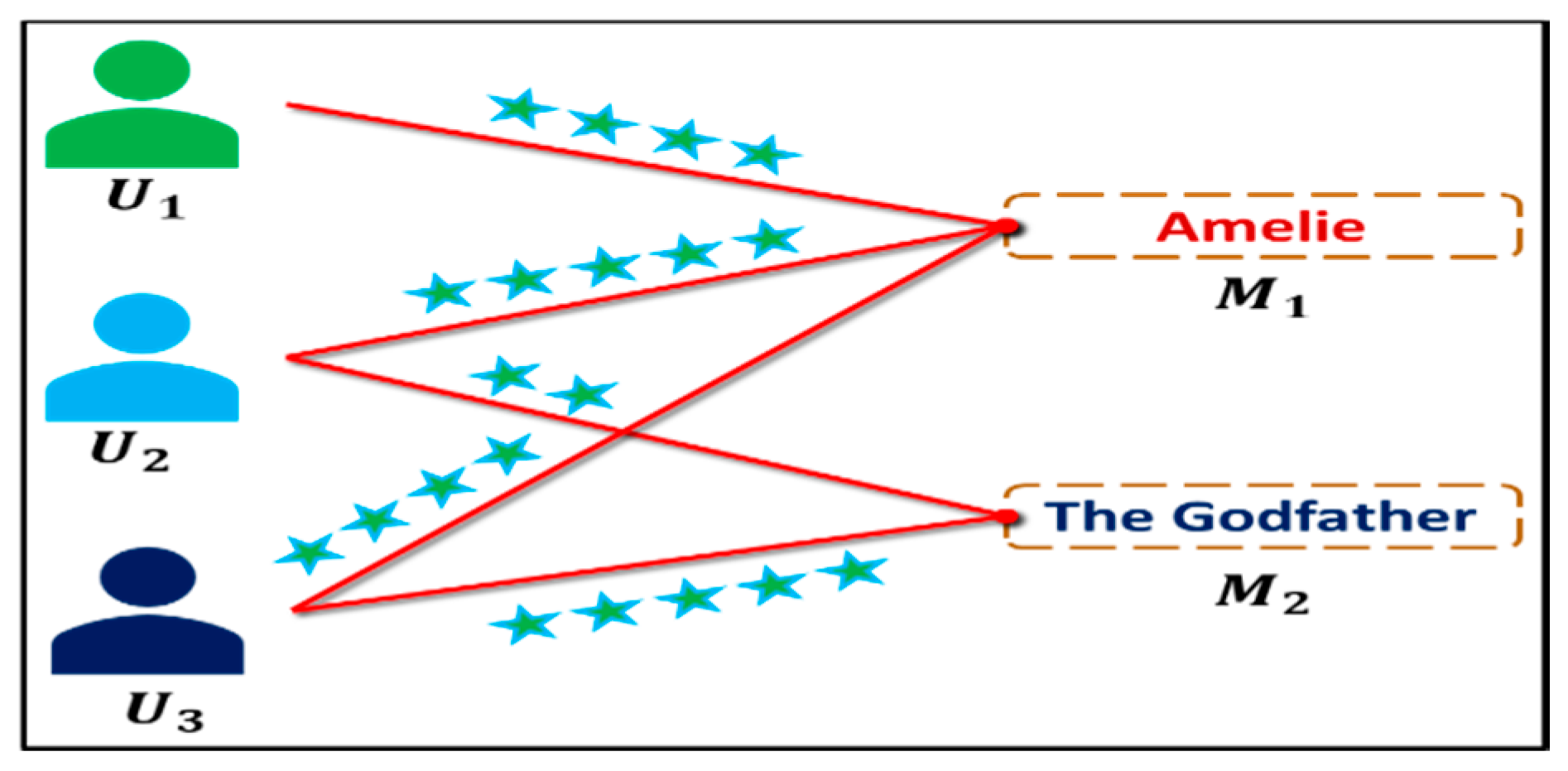
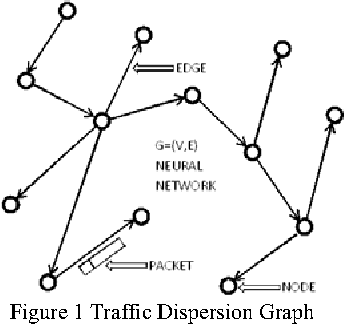
Network Security Analysis Based on Graph Theory Model with
Keywords Network security; Graph theory; Neutral network Download chapter PDF Gan Z B Wu P Lu S F : Application Research of Computers 20(11) |
|
Scenario Graphs Applied to Network Security
We call this set of counterexamples a scenario graph In this chapter we present two different algorithms for producing scenario graphs and explain how scenario |
|
Graph Theory Applications in Network Security - PDF Free Download
Graph Theory Applications in Network Security Jonathan Webb1 In this paper we explore applications of graph theory in cellular networks with an |
|
Network Security Analysis Based on Graph Theory Model with
Abstract In order to improve the safety of network and grasp the safety situation of network correctly the graph theory and neutral network was combined to |
How is graph theory used in network security?
In cybersecurity, a graph-based approach centers on preserving the context of security events by breaking down components of observable data into a graph representation of all cyber artifacts, from all data streams, accounting for all past and present data.- Modern Applications of Graph Theory discusses many cutting-edge applications of graph theory, such as traffic networks, navigable networks and optimal routing for emergency response, and graph-theoretic approaches to molecular epidemiology.
|
Network Security Using Graph Theory - IJIET
Assuming that not many diverse applications use the same port number, port- based TDGs can be used in order to identify the type of application utilizing a given |
|
Graph Theory and Cyber Security - IEEE Xplore
applications of graph theory in computer provides pointers to key theory?", and other one asked me:" Has grap applied to cyber security?" Graphs are discrete |
|
ON ATTACK GRAPH MODEL OF NETWORK SECURITY - Journal
Keywords: Attack graph model; Network security ACM Classification Keywords: C 2 Computer-communication networks; G2 2 Graph Theory; G2 3 Applications |
|
Scenario Graphs Applied to Network Security - Carnegie Mellon
The attack graph we produce for a network model shows all ways in which an intruder can violate a given In our application to security, each path represents an attack, a way in which an intruder can automata theory Model checkers such |
|
APPLICATION OF GRAPH THEORY IN COMMUNICATION
The graph theoretical ideas are used by various computer applications like data mining, image segmentation, clustering Graph theory can be used to represent communication networks A Her research interests include network security, |
|
An Introduction to Graph Theory for Security People Who - Events
The application of graphs in a security context Summary A Little More Advanced Graph Theory You'll often called a directed network or a directed graph, |





![PDF] CS6702 Graph Theory and Applications Lecture Notes Books PDF] CS6702 Graph Theory and Applications Lecture Notes Books](https://i1.rgstatic.net/publication/266970564_Graph_Theory_and_Its_Applications_to_Future_Network_Planning_Software-Defined_Online_Small_Cell_Management/links/544043820cf2fd72f99dd4b3/largepreview.png)