hacker methodology handbook pdf
|
The Hackers Handbook: The Strategy Behind Breaking into and
exploit code and the methodology and programming facilities they draw upon in building a hacking exploit. Written for the nonprogrammer the chapter details |
|
The Web Application Hackers Handbook: Discovering and
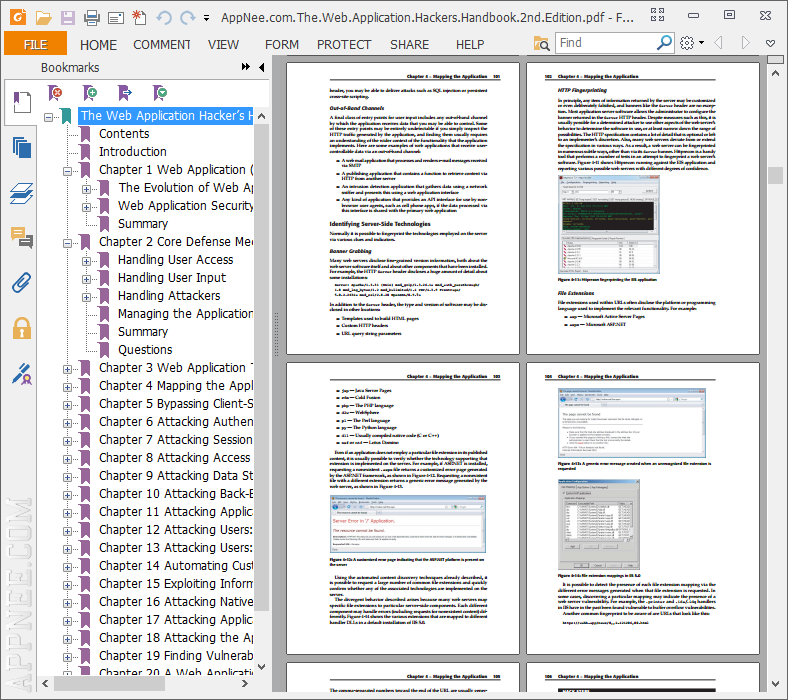
21-Feb-2007 Chapter 20 A Web Application Hacker's Methodology. 665. General Guidelines. 667. 1. Map the Application's Content. |
|
The Web Application Hackers Handbook: Finding and Exploiting
%20Marcus%20Pinto%20-%20The%20web%20application%20hacker's%20handbook_%20finding%20and%20exploiting%20security%20flaws-Wiley%20(2011).pdf |
|
The Car Hackers Handbook
03-Apr-2012 Title: The car hacker's handbook: a guide for the penetration ... methodology known as the common vulnerability scoring system (CVSS). CVSS. |
|
Gray Hat Hacking The Ethical Hackers Handbook
06-Dec-2007 Ethical Hacker's Handbook and Security Information Event ... Testing Methodology Manual (OSSTMM) testing and assessment methodologies. |
|
CEH: Certified Ethical Hacker Study Guide
Understand the CEH scanning methodology Searchable Book in PDF The CD contains the entire book in PDF (Adobe ... A. Download and install the LMSHUT. |
|
The Browser Hackers Handbook
deploy its own PDF rendering engine in Chrome to replace the Adobe Reader software. Figure 1-1: Browser Hacker's Handbook methodology. |
|
The Web Application Hackers Handbook
21-Feb-2007 Chapter 20 A Web Application Hacker's Methodology. 665. General Guidelines. 667. 1. Map the Application's Content. |
|
CAR INFOTAINMENT HACKING METHODOLOGY AND ATTACK
Kinda similar to Jason Haddix's “The Bug Hunters Methodology” pull%20tool%20instructions.pdf ... The Car Hacker's Handbook by Craig Smith: ... |
|
IOS Hackers Handbook
for download. Apps must be signed by a trusted party such as Apple |
|
(PDF FILE) Hacker Methodology Handbook PDF - Yumpu
2 jan 2021 · Turn your PDF publications into a flip-book with our unique Google optimized e-Paper software START NOW Hacker Methodology Handbook (> FILE*) |
|
The Hackers Handbookpdf - Zenk - Security
The hacker's handbook : the strategy behind breaking into and defending Networks / audit methodology for Novell NetWare 4 1 and was an instructor at the |
|
Hugo Cornwall - The Hackers Handbook pdf - X-Files
In the introduction to this book I described hacking as a sport; and like most sports it is both relatively pointless and filled with rules written or |
|
Hacker Methodology Handbook: Bobeck Thomas - Amazoncom
Avis 46 |
|
The Web Application Hackers Handbook
The Web Application Hacker's Handbook: Discovering and Exploiting Security Manual Request Tools Chapter 20 A Web Application Hacker's Methodology |
|
The Web Application Hackers Handbook - Internet Archive
Chapter 21 A Web Application Hacker's Methodology 791 General Guidelines 793 1 Map the Application's Content 795 1 1 Explore Visible Content |
|
Gray Hat Hacking The Ethical Hackers Handbook - cswiscedu
6 déc 2007 · From software exploitation to SCADA attacks this book covers it all Gray Hat Hacking is without doubt the definitive guide to the art of |
|
The web application hackers handbook: discovering and exploiting
This book is a practical guide to discovering and exploiting security flaws in web applications The authors explain eac · Similar Topics · Computers · Security |
|
The Web Application Hackers Handbook: Finding and Exploiting
5000 $US |
|
Amazoncom: Hacker Methodology Handbook: Version 13 eBook
Avis 46 |
|
The Hackers Handbook - Zenk - Security
The hacker's handbook : the strategy behind breaking into and defending Networks / Susan Young exploit code and the methodology and programming facilities they draw This information was uncovered via a manual audit of the system |
|
The Hackers Handbook - Caribbean Environment Programme - UNEP
23 jan 2021 · Thank you very much for downloading The Hacker's Handbook: Everything You book collection an online access to it is set as public so you can download it instantly proven methodology that combines the virtues of |
|
The Hackers Handbook - UNEP
[DOC] The Hacker's Handbook: The Strategy Behind Breaking Into And Defending Networks You will learn a proven methodology for approaching mobile application Hacking Connected Cars-Alissa Knight 2020-03-17 A field manual on |
|
Hackers Handbook - X-Files
you some grasp of methodology, help you develop the appropriate attitudes and skills Finally, to those who would argue that a hacker's handbook must be valid phone number, passwords and extracts from the operations manual of one of |
|
Hacker Methodology
6 jan 2014 · This includes dumpster diving, social engineering and the use of utilities such as web-search hacking, traceroutes, pings, network lookups, etc |
|
The Web Application Hackers Handbook
21 fév 2007 · Chapter 20 A Web Application Hacker's Methodology 665 General if a company's web site links to AnnualReport2004 pdf and Annual |
|
The Hackers Underground Handbook
reader develop a hacker defense attitude in order to prevent the attacks discussed 14 1 Download the Ubuntu Live CD iso file from www ubuntu com What the GET method does is submit the information you type in through the URL so |
|
The Web Application Hackers Handbook
6 juil 2011 · Hacker's Handbook Second Chapter 21 A Web Application Hacker's Methodology We recommend that you download and experiment with |
|
Hacking Methodology
In the past a lot of ethical hacking involved manual processes Now, tools can automate various tasks These tools allow you to focus on performing the tests |
|
Web application hackers handbook v2 pdf - Squarespace
The Web Application Hacker's Handbook: Finding And Exploiting Security Flaws describes a tried and tested methodology that encompasses both the power of |

![Free [epub]$$ Hacker Methodology Handbook Full PDF Free [epub]$$ Hacker Methodology Handbook Full PDF](https://image.slidesharecdn.com/17108f3cdc2-200324015150/95/hacker-methodology-handbook-book-498-2-638.jpg?cb\u003d1585014735)



![FREE] [DOWNLOAD] [READ] Hacker Methodology Handbook in format E-PUB FREE] [DOWNLOAD] [READ] Hacker Methodology Handbook in format E-PUB](https://image.slidesharecdn.com/1713c64084f-200403013958/95/hacker-methodology-handbook-book-938-2-638.jpg?cb\u003d1585878026)


![Free [epub]$$ Hacker Methodology Handbook Full PDF Free [epub]$$ Hacker Methodology Handbook Full PDF](https://image.isu.pub/200427073306-05463aefd34ab1f933a1badd44d055dd/jpg/page_1.jpg)
![Free [epub]$$ Hacker Methodology Handbook Full PDF Free [epub]$$ Hacker Methodology Handbook Full PDF](http://waycelestial.weebly.com/uploads/1/2/3/7/123722480/560375201.jpeg)




![Web Hacking 101 by Peter Yaworski [Leanpub PDF/iPad/Kindle] Web Hacking 101 by Peter Yaworski [Leanpub PDF/iPad/Kindle]](https://cv02.twirpx.net/2600/2600630.jpg?t\u003d20200505020729)