hacking techniques pdf
|
Hacker Techniques and Tools
Hackers should be judged by their hacking not criteria such as degrees |
|
Legal Frameworks for Hacking by Law Enforcement: Identification
10 Mar 2017 enforcement agencies assert that the use of hacking techniques brings ... Found at https://www.eff.org/files/2016/01/18/37-3_vep_2016.pdf. |
|
Hacking Techniques in Wired Networks
of hacking techniques in wired networks and provides in-depth discussions on the common characteristics of cyber attacks |
|
Untitled
Proven techniques can help guide you along the hacking highway and ensure Use this search for PDF documents that might contain sensitive information. |
|
Google Hacking 101.pdf
Google also allows keyword searches in specific parts of web pages using special syntax words. Additional commands called special syntaxes |
|
Google Hacking for Penetration Testers
INURL:orders. INURL:admin. FILETYPE:php. Putting operators together in intelligent ways can cause a seemingly innocuous query… Page 10. Google Hacking Basics. |
|
Hacking: The Art of Exploitation 2nd Edition
“Erickson's book a compact and no-nonsense guide for novice hackers |
|
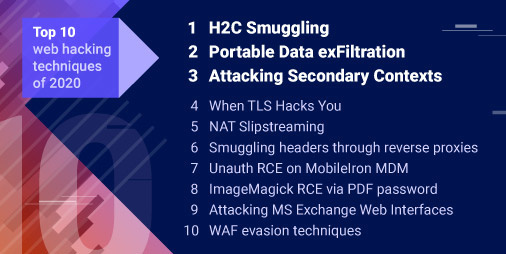
Top Ten Web Attacks
Java Decompilation. Page 21. The Top 10 Web Hacking Techniques. 6. Source Code Disclosure. 7. Input Validation. 8. SQL Query Poisoning. 9. Session Hijacking. 10 |
|
Ethical Hacking Techniques with Penetration Testing
Ethical Hacking Techniques with Penetration Testing. K.Bala Chowdappa S.Subba Lakshmi http://www.eccouncil.org/ ipdf/EthicalHacker.pdf (visited on may. |
|
(PDF) A Review and Comparing of all Hacking Techniques and
PDF This paper presents an investigation and analysis of methods used by hackers to make hacking for any information in any site on the network also |
|
Hacking Attacks Methods Techniques And Their Protection Measures
1 mai 2018 · PDF As public and private associations relocate a greater amount of their basic capacities to the Internet criminals have greater |
|
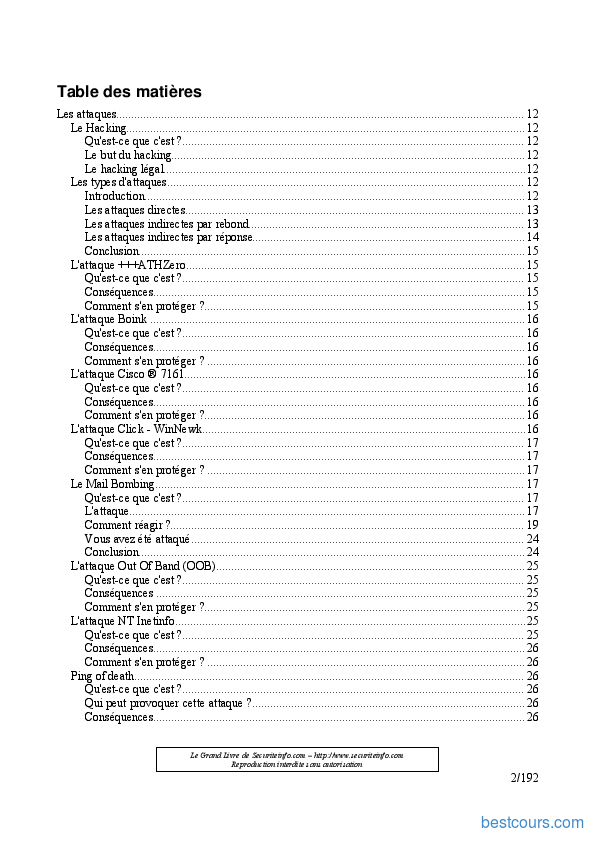
Les Différents Techniques Du Hacking PDF - Scribd
Avis 50 |
|
Hacker Techniques and Tools - Jones & Bartlett Learning
Hacker Techniques and Tools CHAPTER 1 Hacking: The Next Generation 03 CHAPTER 2 TCP/IP Review 21 CHAPTER 3 Cryptographic Concepts 49 CHAPTER 4 |
|
Hacking: The Art of Exploitation 2nd Edition - Zenk - Security
is filled with real code and hacking techniques and explanations of how they work ” The information in this book is distributed on an “As Is” basis |
|
How Hackers Do It: Tricks Tools and Techniques - Zenk - Security
%2520Tools |
|
Common Windows Linux and Web Server Systems Hacking
_Linux_and_Web_Server_Systems_Hacking_Techniques.pdf |
|
Hacking Techniques in Wired Networks - Penn State S2 Group
For example the COPS package [12] can help identify file permission problems easy- to-guess passwords known vulnerable services and improperly configured |
|
Les bases du hackingpdf
techniques mises en place dans le hacking et les tests d'intrusion metagoofil py -d syngress com –t pdf docxlspptx –n 20 -o files –f results html |
|
Les Bases Du Hacking 2e A C Dition Pdf
latest music video techniques de hacking 2e a c dition pdf book web les bases du hacking 2e édition by patrick engebretson web informatiques |
|
Ethical Hacking - Zenk - Security
Evolution of technology focused on ease of use who apply their hacking skills for defensive purposes Usually delivered in hard copy format for |
|
Hacking Techniques in Wired Networks - Penn State S2 Group
of hacking techniques in wired networks and provides in-depth discussions on the common characteristics of cyber attacks the structure and components of |
|
Les bases du hackingpdf
Il y a quelques années une discussion ouverte sur les techniques de hacking et leur enseignement aurait fait l'objet d'un certain tabou Les |
|
Ethical Hacking Techniques with Penetration Testing
This paper attempts to discuss the overview of hacking and how ethical hacking disturbs the security and studied the different types of hacking with its |
|
Hacker Techniques and Tools - Jones & Bartlett Learning
These early hackers went on to create the foundation for technologies such as (http://nvlpubs nist gov/nistpubs/Legacy/SP/nistspecialpublication800-115 pdf ) |
|
Hacking Techniques
Hacking Techniques by Michael Hamm linuxdays lu 2007 4 Hacking Techniques Script Kiddies Hackers Geek filetype: |
|
Hacking: Computer Hacking, Security Testing,Penetration - Pirate
You grabbed the right book In here you will learn about the modern tools and advanced techniques that ethical and criminal hackers use Not only will you learn |
|
Les bases du hacking (Référence) (French Edition)
techniques mises en place dans le hacking et les tests d'intrusion MetaGooFil est capable de traiter les formats pdf , doc, xls, ppt, odp, ods, docx, xlsx et pptx |
|
How Hackers Do It: Tricks, Tools, and Techniques - Zenk - Security
Using easily obtainable freeware security tools, we demonstrate the techniques hackers employ to attack systems All of the attacks described in this article have |
|
Techniques de hacking (Jon Erickson Ed Pearson) - Zenk - Security
FL : Techniques de hacking (Jon Erickson Ed Pearson) Novembre 2009 (C) Fondation Hellday 2008 Ce document est constitué des notes prises durant la |
|
Techniques de Hacking
Techniques de hacking qui résolvaient simplement des problèmes, les premiers hackers avaient pour obses- sion d'écrire des programmes qui résolvaient des |
|
Computer Hacking: A beginners guide to computer hacking, how to
This book includes great tips and techniques that will help you to begin developing your own computer hacking skills You will discover some basic hacks you |
|
The Basics of Hacking and Penetrationpdf
A few years back, the open discussion or teaching of hacking techniques was considered a bit taboo fortunately, times have changed and people are begin- |
|
Hacking Methodology
Proven techniques can help guide you along the hacking highway and ensure Use this search for PDF documents that might contain sensitive information |
![PDF] Mind Hacking free tutorial for Beginners PDF] Mind Hacking free tutorial for Beginners](https://imgv2-1-f.scribdassets.com/img/document/400981911/149x198/738672e037/1551661640?v\u003d1)


![PDF-DOWNLOAD~] Inflation Hacking: Inflating Investing Techniques PDF-DOWNLOAD~] Inflation Hacking: Inflating Investing Techniques](https://data01.123dok.com/thumb/basics-web-hacking-tools-techniques-attack-web-pdf-oy8jdk5z.Pki4ZiPT5VIqTD1so.jpeg)


![Web Application Advanced by Maor Tal [Leanpub PDF/iPad/Kindle] Web Application Advanced by Maor Tal [Leanpub PDF/iPad/Kindle]](https://miro.medium.com/max/1066/0*2u4gcnJ_UfV6lzXs.jpg)

![E-BOOK_DOWNLOAD] LIBRARY~ Hacking Connected Cars Tactics Techniques E-BOOK_DOWNLOAD] LIBRARY~ Hacking Connected Cars Tactics Techniques](https://zbook.org/img/1911/hacking-20with-20kali-ch7_271119022904.jpg)



![PDF] Sécurité informatique (Hacking) cours et formation gratuit PDF] Sécurité informatique (Hacking) cours et formation gratuit](https://ebookscart.com/wp-content/uploads/2019/12/1-72.png)











