header manipulation vulnerabilities
|
Fortify Developer Workbook
15 abr 2014 Since Header Manipulation vulnerabilities like cookie manipulation occur when an application includes malicious data in its. |
|
Header Manipulation Rules Resource Guide
When you use the out-of-dialog setting for an outbound manipulation the Oracle. Communications Session Border Controller only executes this specific SIP header |
|
IPv6 Security Vulnerabilities
An attacker could perform header manipulation on the extension headers to create attacks. Someone could create an IPv6 packet that meets. |
|
Exploring HTTP Header Manipulation In-The-Wild
3 abr 2017 how future protocol decisions on header manipulation may affect ... [7] Squid: Security vulnerabilities. https:. |
|
Finding Security Vulnerabilities in Java Applications with Static
25 sept 2005 2.2.4 HTTP Header Manipulation . ... discovered application vulnerabilities such as SQL injections cross-site scripting |
|
E-Mail Header Injection Vulnerabilities
With the proper injection string E-mail Header Injec- tion vulnerabilities can be exploited by an attacker to inject additional headers |
|
Micro Focus Fortify WebInspect Agent Rulepack Kit Guide
Vulnerability Rules. VulnerabilityrulesimproveMicro FocusFortifyWebInspect WebInspect Agent in acustomHTTP header. ... Header Manipulation: IMAP. |
|
First Do No Harm: Studying the manipulation of security headers in
25 feb 2021 Tampering with these headers may hamper the client-side security of the applications and expose them to vulnerabilities. |
|
Micro Focus Fortify WebInspect Agent Rulepack Kit Guide
12 may 2021 vulnerabilities: ?. ClassLoader Manipulation: Struts. ?. Header Manipulation: IMAP. ?. Header Manipulation: SMTP. |
|
Micro Focus Fortify WebInspect Agent Rulepack Kit Guide
Vulnerability Rules. VulnerabilityrulesimproveMicro FocusFortifyWebInspect WebInspect Agent in acustomHTTP header. ... Header Manipulation: IMAP. |
|
Exploring HTTP Header Manipulation In-The-Wild
7 avr 2017 · In this paper we explore the propensity of different network types and regions to manipulate HTTP headers in terms of both fre- quency (§5) |
|
HTTP Response Splitting
HTTP Response Splitting is a protocol manipulation attack similar to Message Headers – metadata that describes a request or response |
|
How to identify and exploit HTTP Host header vulnerabilities
In this section we'll look more closely at how you can identify whether a website is vulnerable to HTTP Host header attacks We'll then provide examples of |
|
Ajax request header manipulation (DOM-based) - PortSwigger
Ajax request header manipulation arises when a script writes controllable data into a header of an Ajax request that is issued using XmlHttpRequest An attacker |
|
Fortify Developer Workbook
15 avr 2014 · Since Header Manipulation vulnerabilities like cookie manipulation occur when an application includes malicious data in its |
|
Ch 13: Attacking Users: Other Techniques (Part 2)
HTTP header injection allows an attacker to HTTP header injection vulnerability Exploit session fixation vulnerabilities |
|
Studying the manipulation of security headers in browser extensions
25 fév 2021 · Tampering with these headers may hamper the client-side security of the applications and expose them to vulnerabilities |
|
Exploring HTTP Header Manipulation In-The-Wild
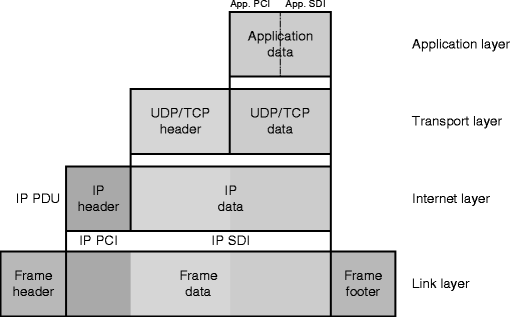
3 avr 2017 · Headers are a critical part of HTTP and it has been shown that they are increasingly subject to middlebox manipulation |
|
Header-Based Attacks SpringerLink
Header-based attacks are a form of computer offensive in which the attacker uses its ability to forge arbitrary header data to exploit a flaw in the |
|
E-mail Header Injection Vulnerabilities Semantic Scholar
20 jan 2017 · Abstract E-mail Header Injection vulnerability is a class of vulnerability that can occur in web applications that use user input to |
|
Ajax request header manipulation (stored DOM-based) - PortSwigger
Ajax request header manipulation arises when a script writes controllable data into a header of an Ajax request that is issued using XmlHttpRequest An attacker |
|
Finding Protocol Manipulation Attacks - UCLA CS
may be vulnerable to manipulation (e g , bandwidth) and protocol actions at honest sender, obediently reflects the ECN bit from the packet header into |
|
E-Mail Header Injections An Analysis of the World Wide - CORE
E-Mail header injection vulnerability is a class of vulnerability that can occur in web applications that use user input to construct e-mail messages E-Mail injection is possible when the mailing script fails to check for the presence of e-mail headers in user input (either form fields or URL parameters) |
|
HPE Security Fortify WebInspect Agent Rulepack Kit Guide
not generateanyevents Vulnerability Rules request to Fortify WebInspect Agent in acustomHTTP header Header Manipulation: SMTP ○ MailCommand |
|
Fortify Runtime Application Protection Rulepack Kit Guide
Header Manipulation 24 Malformed Request: Missing Accept Header 28 RTAP rules produce three types of events: attack, vulnerability, and audit |
|
This could be the user input in header
The Attack • HTTP Response Splitting is a protocol manipulation attack, similar to The HTTP response splitting vulnerability is not the attack, it is simply the |
|
E-Mail Header Injections An Analysis of the World Wide Web by Sai
E-Mail header injection vulnerability is a class of vulnerability that can occur in Mail Header Injection vulnerabilities on the Internet manipulate any header |
|
Fortify Developer Workbook
15 avr 2014 · Vulnerability Examples by Category Category: Header Manipulation: Cookies (9 Issues) 0 1 2 3 4 5 6 7 8 9 Number of Issues |
|
847 Web Application Attack Facts
16 mar 2020 · DNS cache poisoning can occur with header manipulation To carry out a cache poisoning attack, the attacker first finds the vulnerability in the |
|
Countering Web Injection Attacks: A Proof of Concept - School of
designed to manipulate the web application's security and data This section outlines establishing a vulnerable service code to inject the new HTTP header |







![PDF] Detection of vulnerabilities and automatic protection for web PDF] Detection of vulnerabilities and automatic protection for web](https://portswigger.net/web-security/images/http-request-smuggling.svg)


![PDF] Towards Vulnerability Discovery Using Staged Program Analysis PDF] Towards Vulnerability Discovery Using Staged Program Analysis](https://docs.microsoft.com/en-us/azure/web-application-firewall/media/application-gateway-crs-rulegroups-rules/managed-rules-01.png)