heap exploitation
|
Investigation of x64 glibc heap exploitation techniques on Linux
We present an analysis and classification of eight different heap exploiting techniques. To demonstrate this we have developed three different vulnerable |
|
Untitled
Example: Linux kernel memory allocator (SLUB). Example: jemalloc userland memory allocator. Abstracting heap exploitation |
|
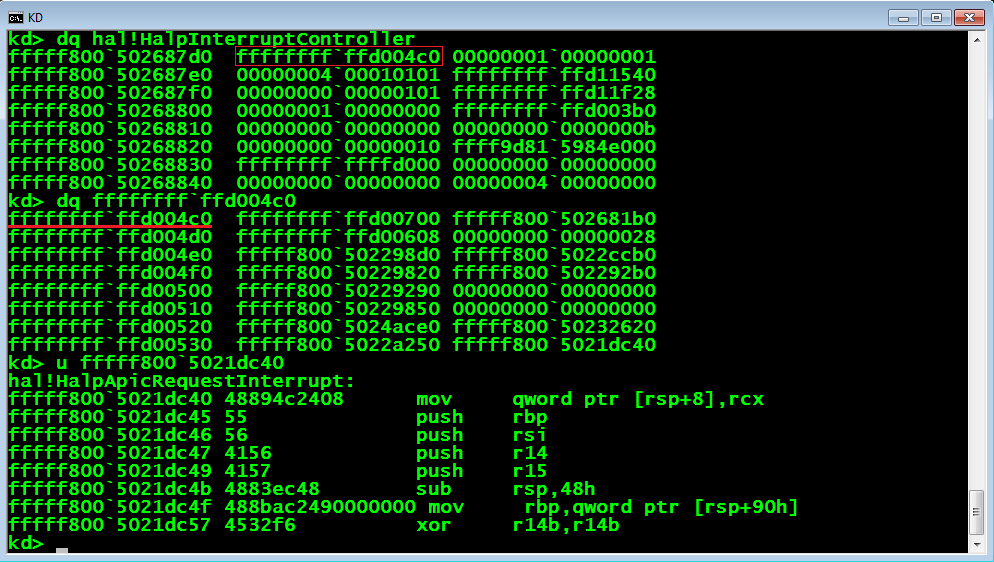
Practical Windows XP/2003 Heap Exploitation
Practical Windows XP/2003 Heap Exploitation. 2. John McDonald (jrmcdona@us.ibm.com). Chris Valasek (cvalasek@us.ibm.com). IBM ISS X-Force Research |
|
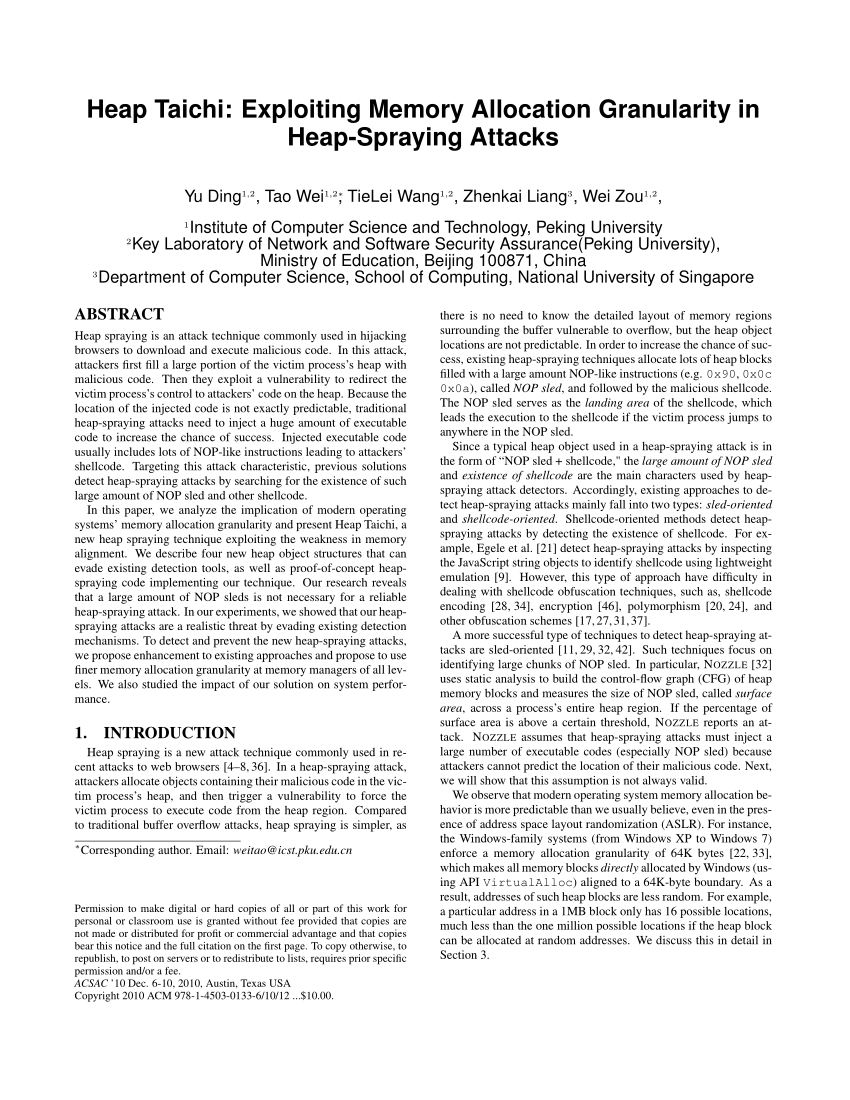
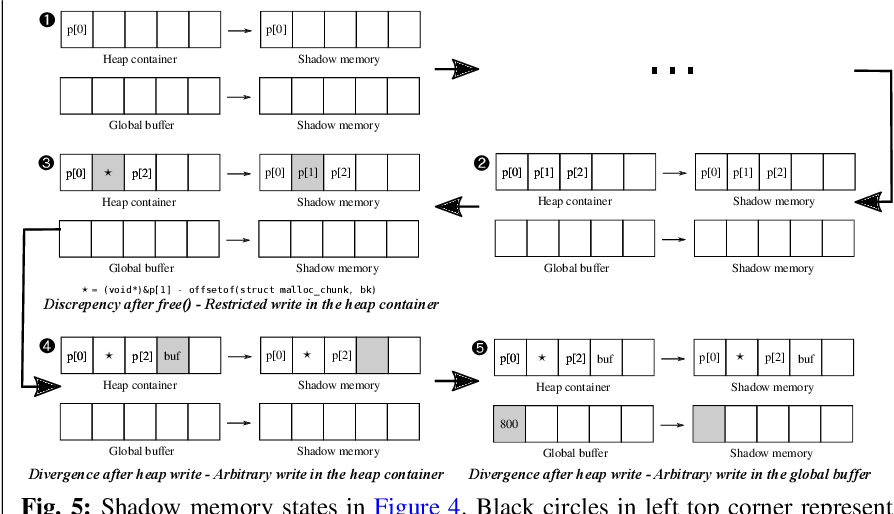
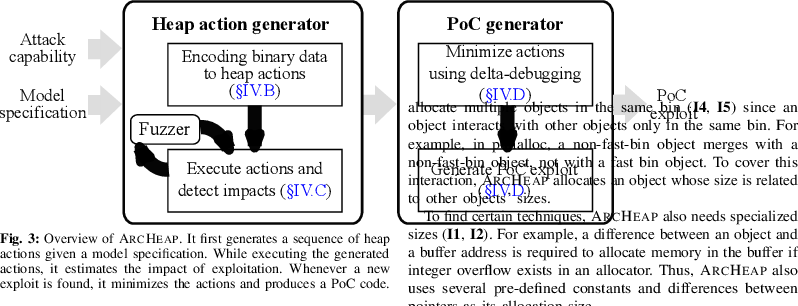
Automatic Techniques to Systematically Discover New Heap
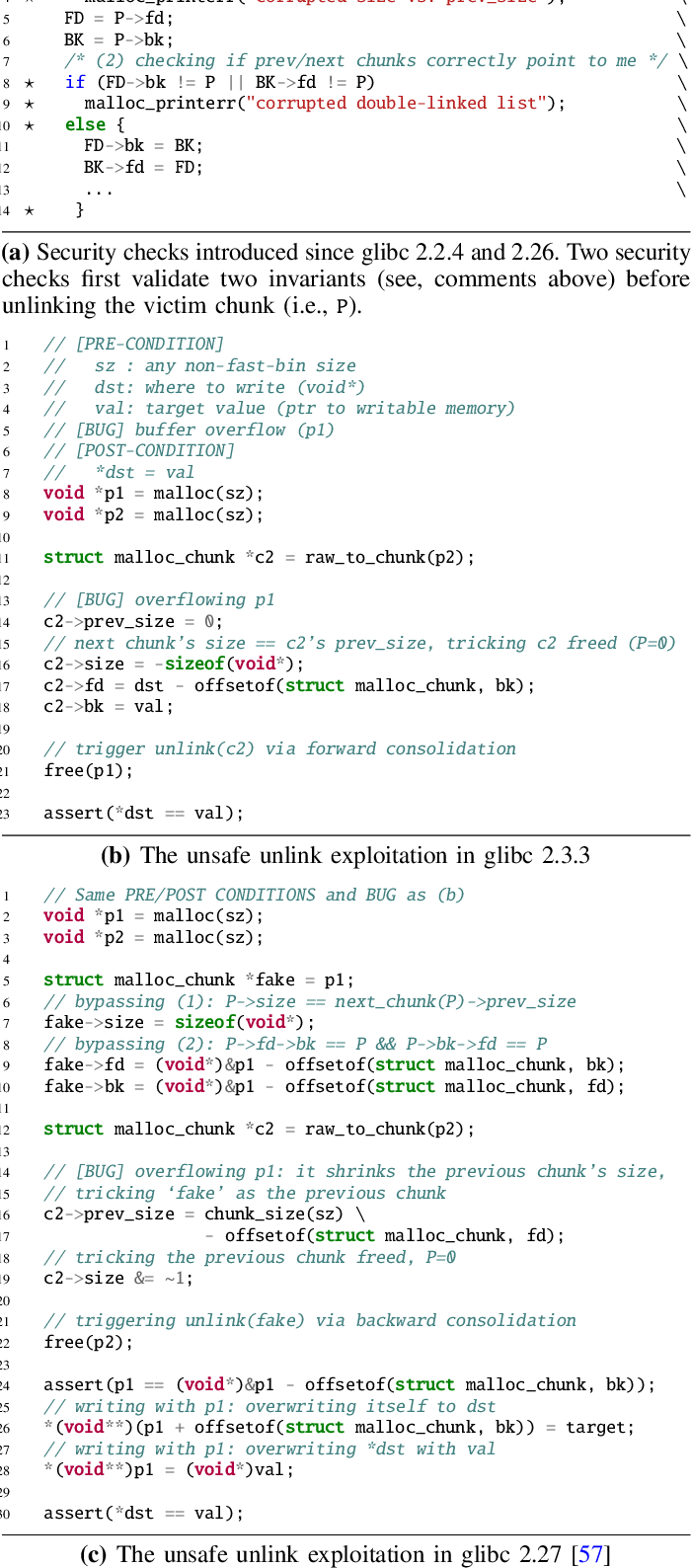
Exploitation techniques to abuse metadata of heap allocators have been widely studied because of their generality (i.e. application independence) and |
|
Automatic Techniques to Systematically Discover New Heap
Aug 12 2020 Abstract. Exploitation techniques to abuse metadata of heap allocators have been widely studied because of their generality (i.e. |
|
Automatic Techniques to Systematically Discover New Heap
Heap exploitation techniques (HETs) are preferable methods to exploit heap vulnerabilities. • Abuse underlying allocator to achieve more powerful primitives |
|
The Shadow over Android Heap exploitation assistance for
We have done some too on exploiting jemalloc targets. ? Standalone jemalloc Firefox's heap |
|
Binding the Daemon FreeBSD Kernel Stack and Heap Exploitation
Why target FreeBSD? ?. Background. ?. Related work. ?. Exploitation. ?. Kernel stack overflows. ?. Kernel heap (memory allocator) overflows. |
|
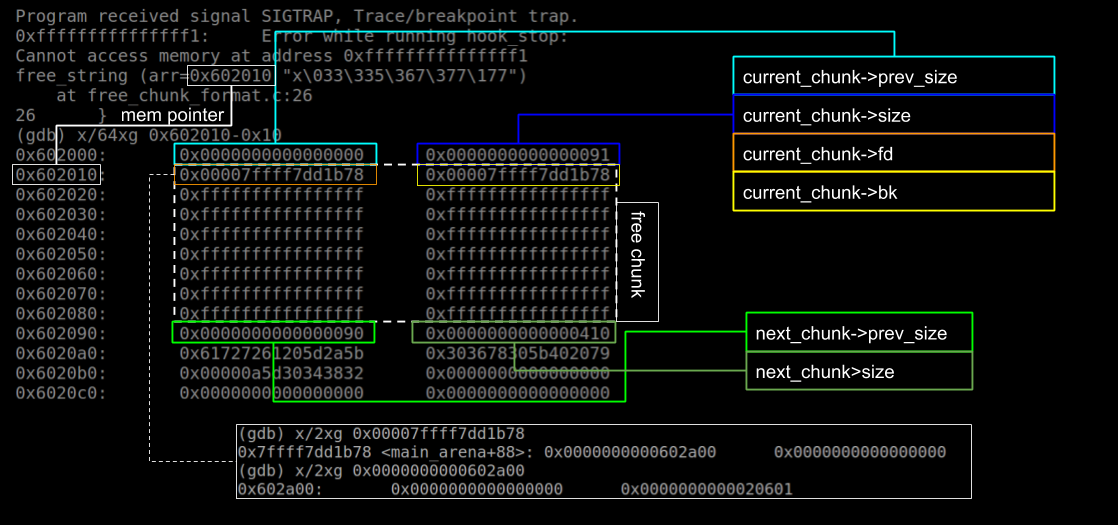
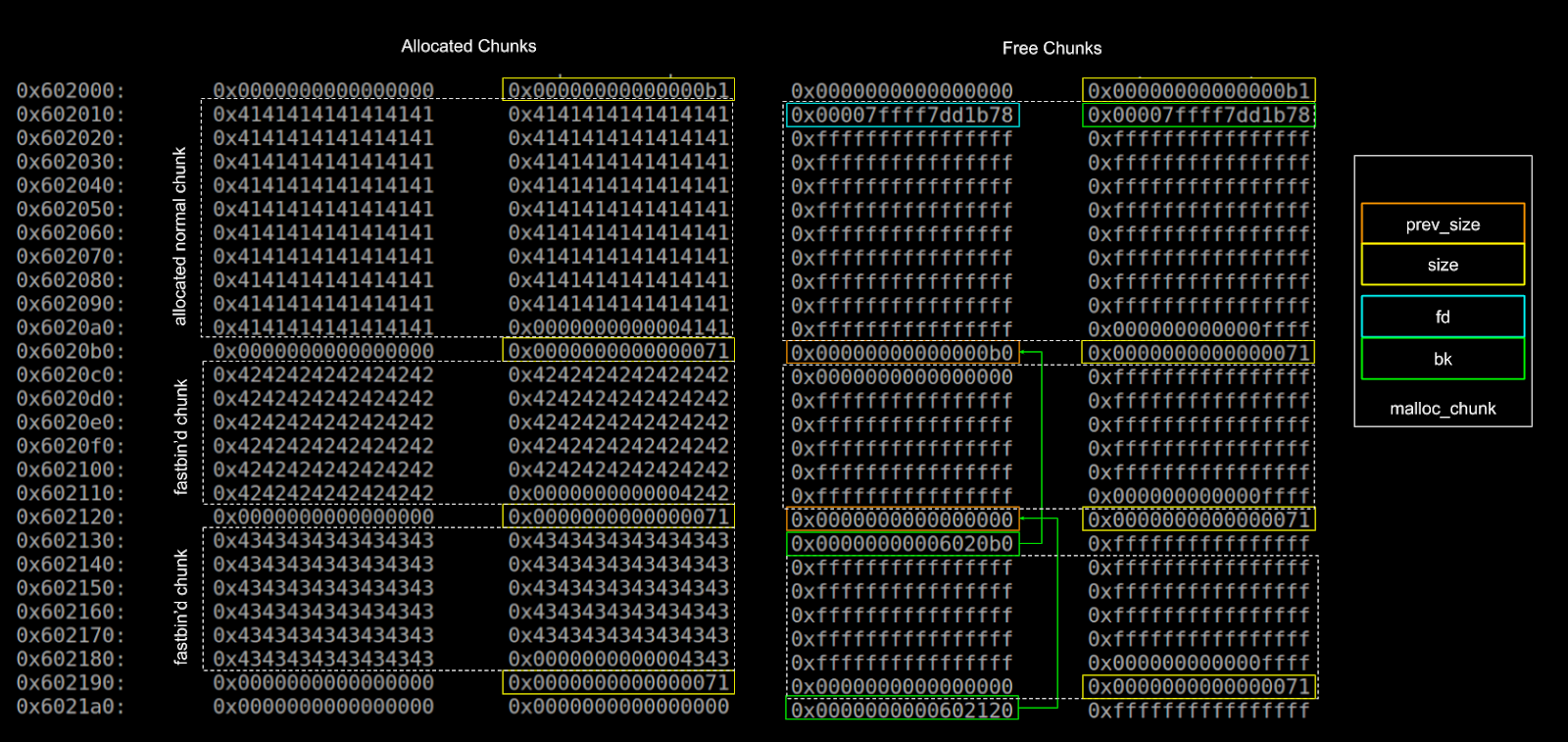
Heap-exploitation.pdf
Heap Memory. Diving into glibc heap malloc_chunk malloc_state. Bins and Chunks. Internal Functions. Core Functions. Security Checks. Heap Exploitation. |
|
Modular Synthesis of Heap Exploits
of program memory such as stack and heap buffer overflows |
|
Heap-exploitationpdf - The Swiss Bay
27 mar 2017 · This book is for understanding the structure of heap memory as well as the different kinds of exploitation techniques related to it The |
|
Heap exploitation
23 nov 2020 · Heap exploitation G Lettieri 23 November 2020 1 Introduction The heap is the area of a process' memory where the C library's malloc() |
|
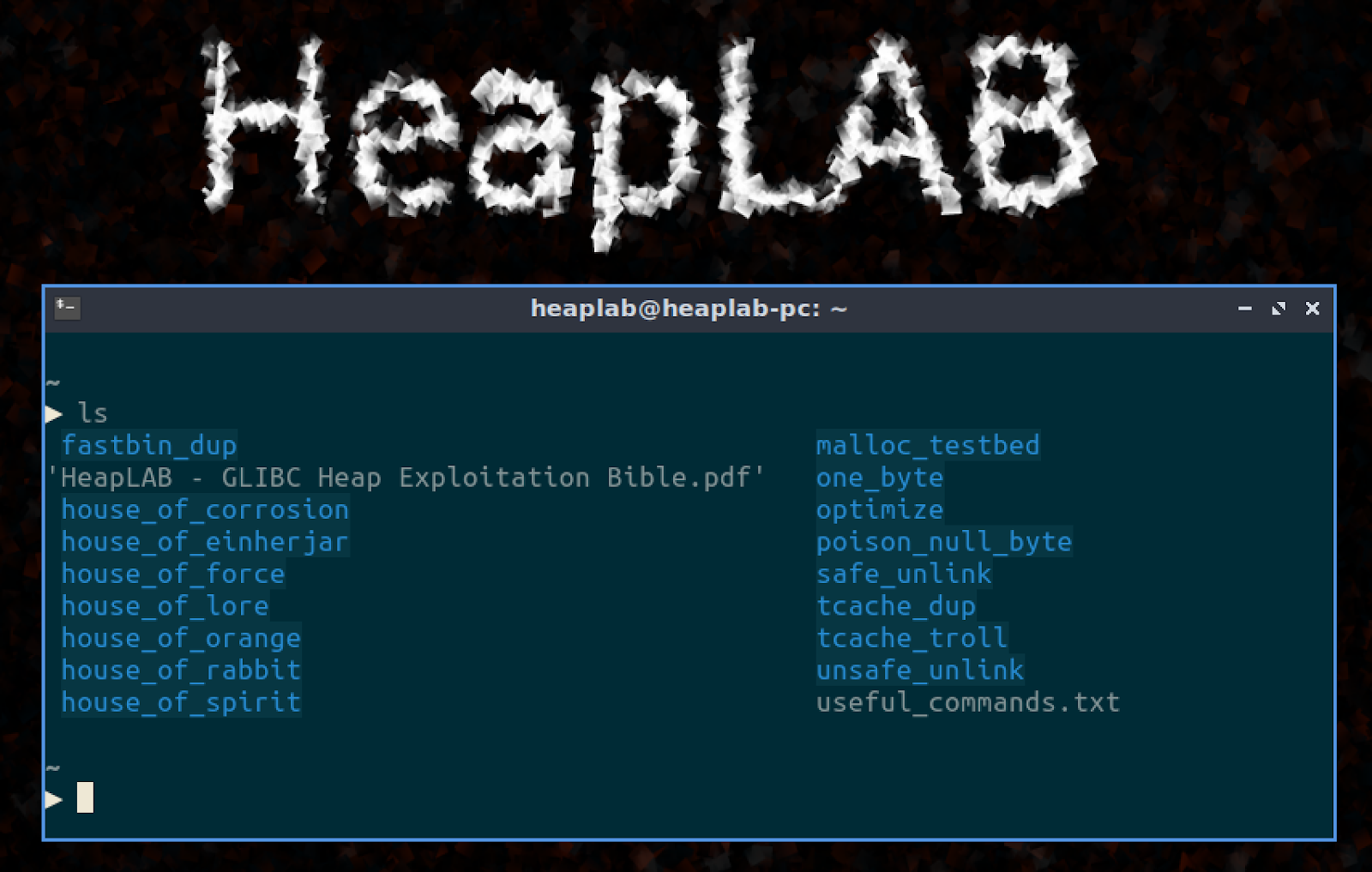
GLIBC Heap Exploitationpdf at main · limitedeternity/HeapLAB
Udemy – Linux Heap Exploitation Contribute to limitedeternity/HeapLAB development by creating an account on GitHub |
|
Investigation of x64 glibc heap exploitation techniques on Linux
This thesis sheds a light of different heap exploitation techniques relevant for the GNU C standard library on 64-bit Intel architecture on Linux We |
|
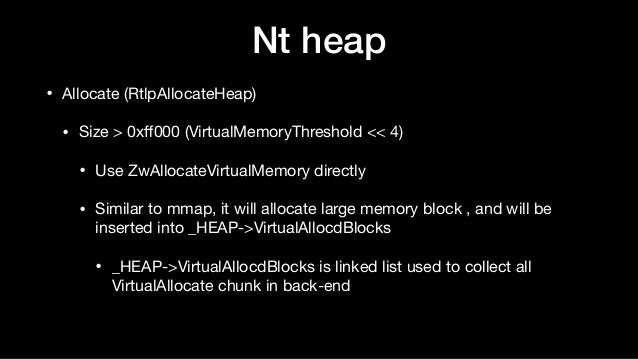
Heap de Windows : structure fonctionnement et exploitation
%2520fonctionnement%2520et%2520exploitation.pdf |
|
Lec13: Heap Exploitation
22 nov 2019 · Allocators B I C Description (applications) ptmalloc ? ? ? A default allocator in Linux dlmalloc ? ? ? An allocator that ptmalloc |
|
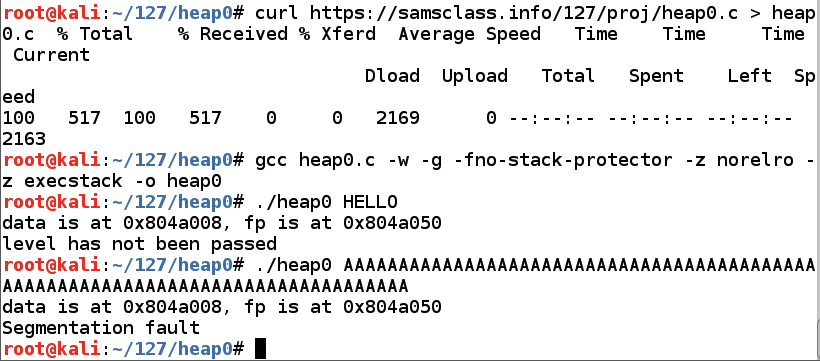
Week 11 - Heap Exploitation
How to use the heap? • malloc(size_t n) • Returns a pointer to newly allocated chunk of at least n bytes • |
|
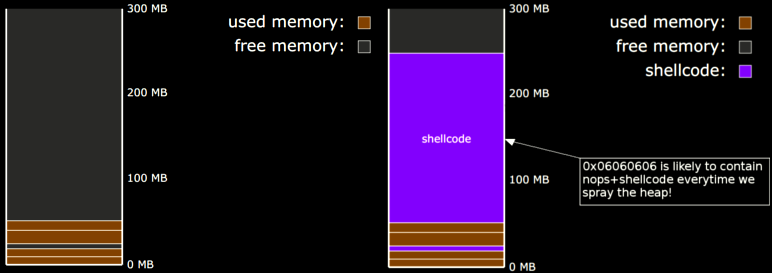
Heap Layout Optimisation for Exploitation (Technical Report)
Thus the attacker must reason about heap layout in order to automatically construct an exploit; it is this problem which we address To leverage OOB memory |
|
PHRACK HEAP HACKING - Seebug
If you are familiar with Linux heap exploitation (and more precisely with http://securityevaluators com/files/papers/isewoot08 pdf |
|
CSC 472/583 Topics of Software Security Heap Exploitation (2)
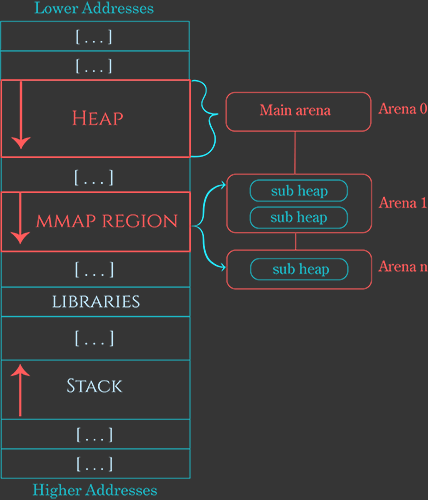
Heap Stack 0xb7ff0000 – Top of heap 0xbfff0000 – Top of stack 0xFFFFFFFF – End of memory MBE - 04/07/201 5 Heap Exploitation |
|
Heap Exploitation - Lao-Yuans Blog
Heap Memory Diving into glibc heap malloc_chunk malloc_state Bins and Chunks Internal Functions Core Functions Security Checks Heap Exploitation |
|
Investigation of x64 glibc heap exploitation techniques - UiO - DUO
This thesis sheds a light of different heap exploitation techniques relevant for the GNU C standard library on 64-bit Intel architecture on Linux We present an |
|
Introduction au heap exploitation - Sploitbox
struct malloc_chunk { size_t prev_size; size_t curr_size; /* fd et bk sont utilisés seulement lorsque le chunk est libre, sinon le reste du chunk est le buffer de |
|
Automatic Techniques to Systematically Discover New Heap
Heap exploitation techniques have steadily been used in real-world exploits To show that, we collected successful exploits for heap vulnerabilities leading to |
|
Heap exploitation
23 nov 2020 · The heap is the area of a process' memory where the C library's malloc() function and the C++ new operator allocate space from |
|
Heap Exploitation Abstraction by Example - Census Labs
Topics: kernel/heap exploitation, auditing Chariton Karamitas, huku Student at AUTh, intern at Census, Inc Topics: compilers, heap exploitation, maths |
|
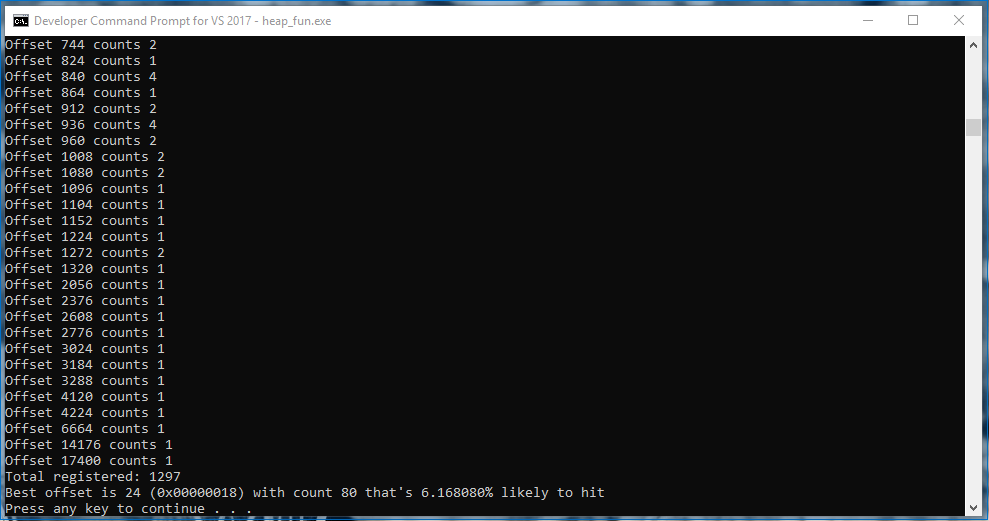
Understanding the heap by breaking it - Black Hat
Traditional exploitation techniques of overwriting heap metadata has been 4 4 Exploitation method 2: ptr = (pointer+offset) = pointer ??, double free of |
|
Heap Exploitation
Heap Background ○ What is the Heap ○ Heap Chunks □ What's in one ○ Heap Exploitation ○ Use After Free ○ Double Free ○ Heap Overflow |















![PDF] Automatic Techniques to Systematically Discover New Heap PDF] Automatic Techniques to Systematically Discover New Heap](https://samsclass.info/127/proj/p7-heap4.png)



![PDF] Automatic Techniques to Systematically Discover New Heap PDF] Automatic Techniques to Systematically Discover New Heap](https://pbs.twimg.com/media/D0-beQ_XgAE5Hya.png)


![PDF] Automatic Techniques to Systematically Discover New Heap PDF] Automatic Techniques to Systematically Discover New Heap](https://i.ytimg.com/vi/6-Et7M7qJJg/mqdefault.jpg)




![PDF] Automatic Techniques to Systematically Discover New Heap PDF] Automatic Techniques to Systematically Discover New Heap](https://image.slidesharecdn.com/advwinexploitation-180820043300/95/advanced-windows-exploitation-3-638.jpg?cb\u003d1534739686)