http proxy cloudflare exploit
|
Finding The Real Origin IPs Hiding Behind CloudFlare or TOR
Aug 19 2018 Starting a quick pentest could reveal the IP as well. Headers like the HTTP server header can be used to find possible ex- ploits for the ... |
|
Hacking Tools Cheat Sheet
curl http://10.5.23.42:2305/?foo=bar --proxy http://127.0.0.1:8080: Set proxy ... Show exploit file path and copy it into clipboard:. |
|
KASPERSKY SECURITY BULLETIN 2013
For example MiniDuke included the first exploit capable look for insecure web sites and plant a malicious script into HTTP or PHP code on. |
|
Host of Troubles: Multiple Host Ambiguities in HTTP Implementations
cache proxy or firewall) interprets the request one way but the final destination (such as a leading to three exploiting techniques: (a) multiple Host. |
|
Forwarding-Loop Attacks in Content Delivery Networks
(such as appending custom HTTP headers like CloudFlare's. CF-Connecting-IP [19]) to detect adds a new header Incapsula-Proxy-ID |
|
Internet
(such as appending custom HTTP headers like CloudFlare's The vulnerability we examine in ... Table I presents the 16 CDNs and their vulnerability to. |
|
Cached and Confused: Web Cache Deception in the Wild
Aug 12 2020 the use of massive networks of caching proxies deployed ... disagreement can then be exploited to trick the web cache. |
|
Host of Troubles: Multiple Host Ambiguities in HTTP Implementations
Exploits multiple ambiguities of HTTP response headers. (Content-Encoding .etc). • Host header attacks [Kettle 2013]. • Exploiting insufficient input |
|
# references WP Security Whitepaper May 4 2016 <http://arstechnica.com/security/2016/05/easily-exploited-bug-exposes-huge- ... DNS-level (Cloudflare |
|
T-Reqs: HTTP Request Smuggling with Differential Fuzzing
Nov 15 2021 HTTP Request Smuggling (HRS) is an attack that exploits the HTTP processing discrepancies between two servers deployed in a proxy- origin ... |
|
Finding The Real Origin IPs Hiding Behind CloudFlare or TOR
19 août 2018 · Hidden services and the effectiveness of CloudFlare or any similar service live from hiding the origin servers IP |
|
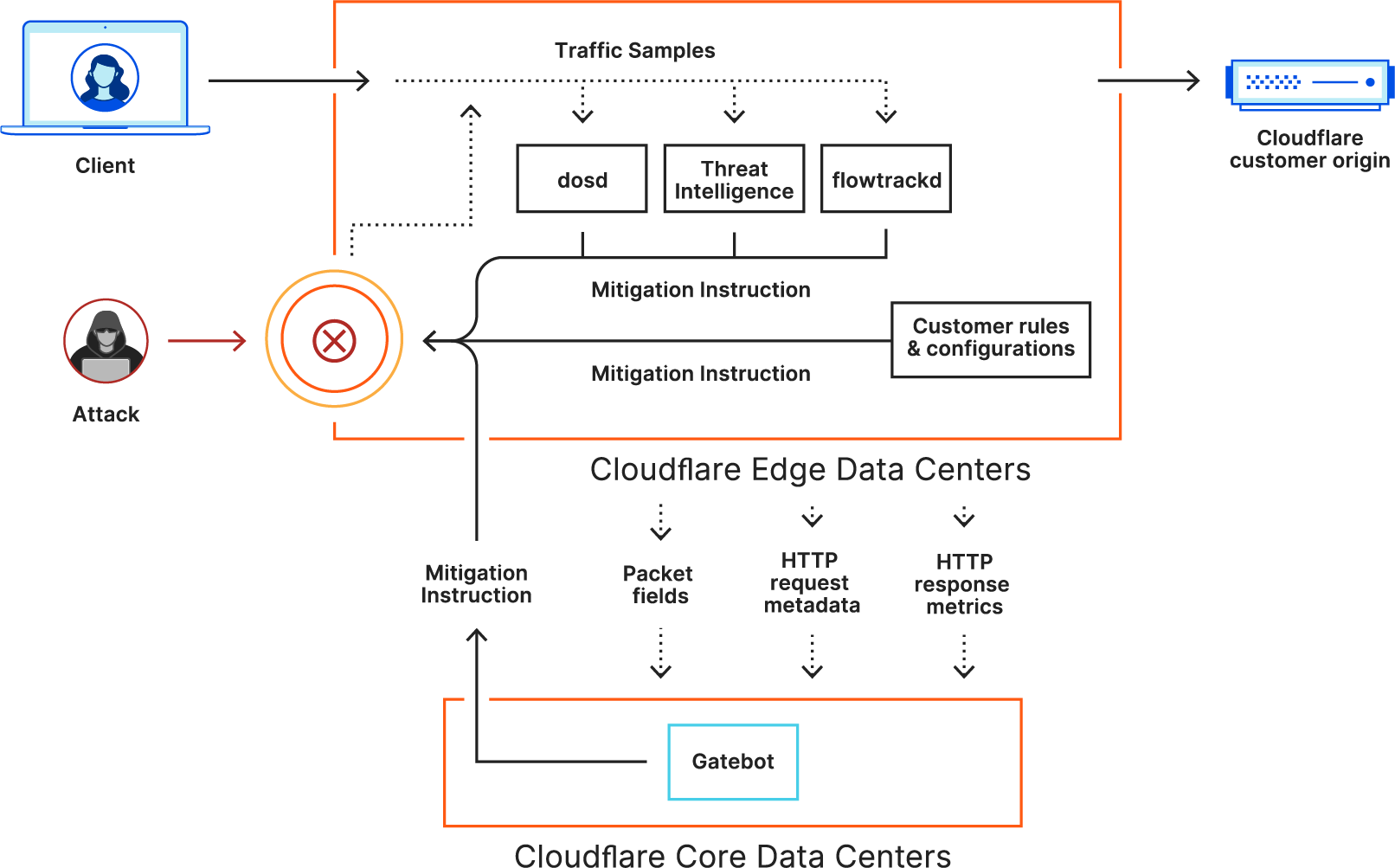
Cloudflare Zero Trust
Comprehensive logs for DNS HTTP SSH network and Shadow IT activity Monitor user activity across all apps Send logs to multiple of your preferred cloud |
|
WAF product brief Fall 2022 - Cloudflare
Our managed rules block exploits complemented by machine learning-derived WAF attack scores to detect evasions OWASP top ten threats Attacks require layered |
|
Common browser isolation challenges and how to overcome them
8 avr 2021 · Cloudflare's Network Vector Rendering (NVR) technology intercepts the remote Chromium browser's Skia draw commands tokenizes and compresses |
|
Cloud Application Security & Performance - Cloudflare
The majority of web traffic today is served through CDNs Malicious payloads exploit application vulnerabilities using methods such as SQL injections |
|
A tale of a DNS exploit: CVE-2015-7547 - The Cloudflare Blog
29 fév 2016 · The DNS proxy on localhost is going to ask the attacker both queries over UDP valgrind curl https://www cloudflare com/ ==6025== Process |
|
A hands-on gaze on HTTP/3 security through the lens of - arXiv
sumed that by exploiting HPACK HTTP/2-enabled proxies could be over after the attack was active for 30 sec Cloudflare presented an |
|
A Large-scale Analysis of Content Modification by Open HTTP Proxies
open HTTP proxies are an attractive option for bypassing IP- based filters and geo-location the services launched by cloud providers such as CloudFlare2 |
|
Hacking Tools Cheat Sheet - Compass Security
Hacking Tools Cheat Sheet Compass Security Version 1 1 compass-security com on https://crt sh --proxy http://127 0 0 1:8080: Set proxy |
|
The Security Impact of HTTPS Interception - J Alex Halderman
company that serves approximately 5 of all web traffic [25] Cloudflare provides these services by acting as a reverse proxy Clients connect to one of |
|
Finding The Real Origin IPs Hiding Behind CloudFlare or TOR
19 août 2018 · directly connecting to your IP on port 443 (https://136 23 63 44:443) proxy services like CloudFlare mostly requires a certain amount of un- |
|
Web Cache Deception Attack - Black Hat
A proxy server that retrieves resources from the web server on behalf of An unauthenticated attacker can easily exploit this vulnerability, as shown in the following steps: Cloudflare server checks for the existence of HTTP caching headers |
|
Practical Web Cache Poisoning: Redefining - PortSwigger
Web cache poisoning has long been an elusive vulnerability, a 'theoretical' threat used Vary header is only used in a rudimentary way, CDNs like Cloudflare ignore it poisoning caches - you can also use HTTP Response Splitting and Request Sifting through proxy history logs revealed that the culprit was Firefox itself |
|
Your Cache Has Fallen: Cache-Poisoned Denial-of - CPDoS
cal relevance by identifying one proxy cache product and five CDN services that are HTTP; Web Caching; Cache Poisoning; Denial of Service ACM Reference is successful, the response splitting attack exploits a parsing issue in the origin Akamai, Fastly, CDN77, Cloudflare, CloudFront and Varnish cache this status |
|
Cloud Application Security & Performance: Critical - Cloudflare
Hackers use login software and proxies, often IoT botnets, to bombard websites and SaaS Malicious payloads exploit application vulnerabilities using methods such as SQL A website that uses SSL (TLS) will have an HTTPS web address |
|
Forwarding-Loop Attacks in Content Delivery Networks - ICSI
(such as appending custom HTTP headers like CloudFlare's The vulnerability we examine in adds a new header, Incapsula-Proxy-ID, with the ID set to |
|
Virtual Host Confusion: Weaknesses and Exploits
requests to a virtual host reverse proxies D Exploiting shared HTTP proxies on CDNs Because CloudFlare is willing to include any domain in their |
|
CDN Backfired: Amplification Attacks Based on HTTP Range Requests
exploiting the implementation flaws on multi-range requests and by connecting the Cloudflare and Akamai to launch an OBR attack and selecting a 1KB file as the the FCDN's origin server as our proxy server and set the proxy server to |
|
HTTP/2 Tsunami: Investigating HTTP/2 Proxy Amplification DDoS
common approach is to use a HTTP/2 to HTTP/1 proxy, this allows for the older CDNs such as Cloudflare have also enabled HTTP/2 by default for all their consist of an attacker exploiting the dynamic header compres- sion by referencing |