information security program plan template
|
Creating a Written Information Security Plan for your Tax
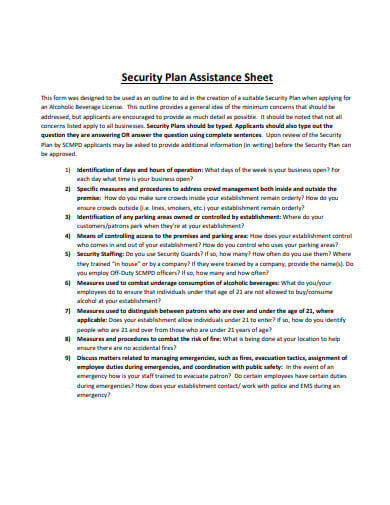
As a part of the plan the FTC requires each firm to: • Designate one or more employees to coordinate its information security program. • Identify and assess |
|
FY 2023 Tribal Cybersecurity Grant Program (TCGP) Cybersecurity
Please reach out to your assigned FEMA Preparedness Officer if you require additional technical assistance with completing this Cybersecurity Plan Template. Or |
|
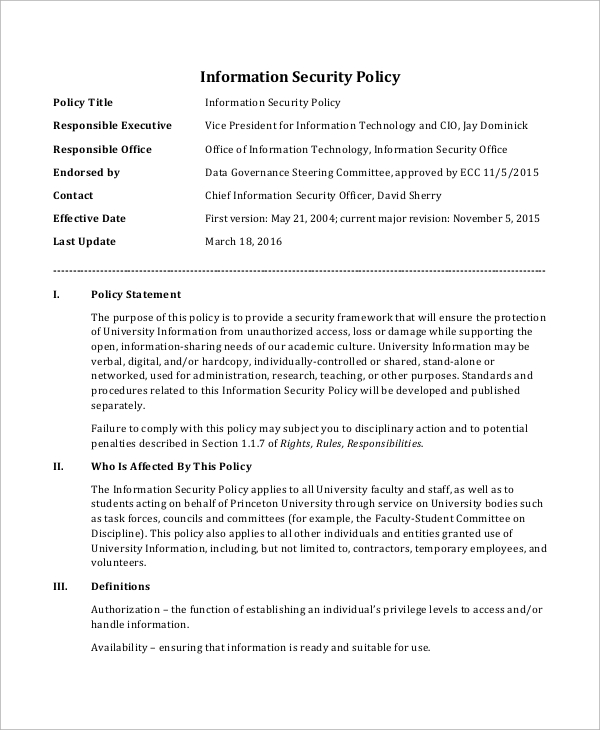
Security-plan-example.pdf
information and procedures associated with this Security Plan. The CIP Cyber Security Awareness Program serves as the first layer of cyber security education. |
|
Sample Information Security Program
Insure the security and confidentiality of the Dealership's customer information. •. Protect against any anticipated threats or hazards to the security and/or |
|
Cybersecurity Plan Guidance
Jun 22 2023 The templates provide guidance on how to structure a comprehensive plan that meets a project's risk profile. DOE uses cybersecurity plans to ... |
|
Sample Written Information Security Plan
Sample Written Information Security Plan. I. OBJECTIVE: Our objective in the 3) Use software program that requires each employee to enter a unique log-in ... |
|
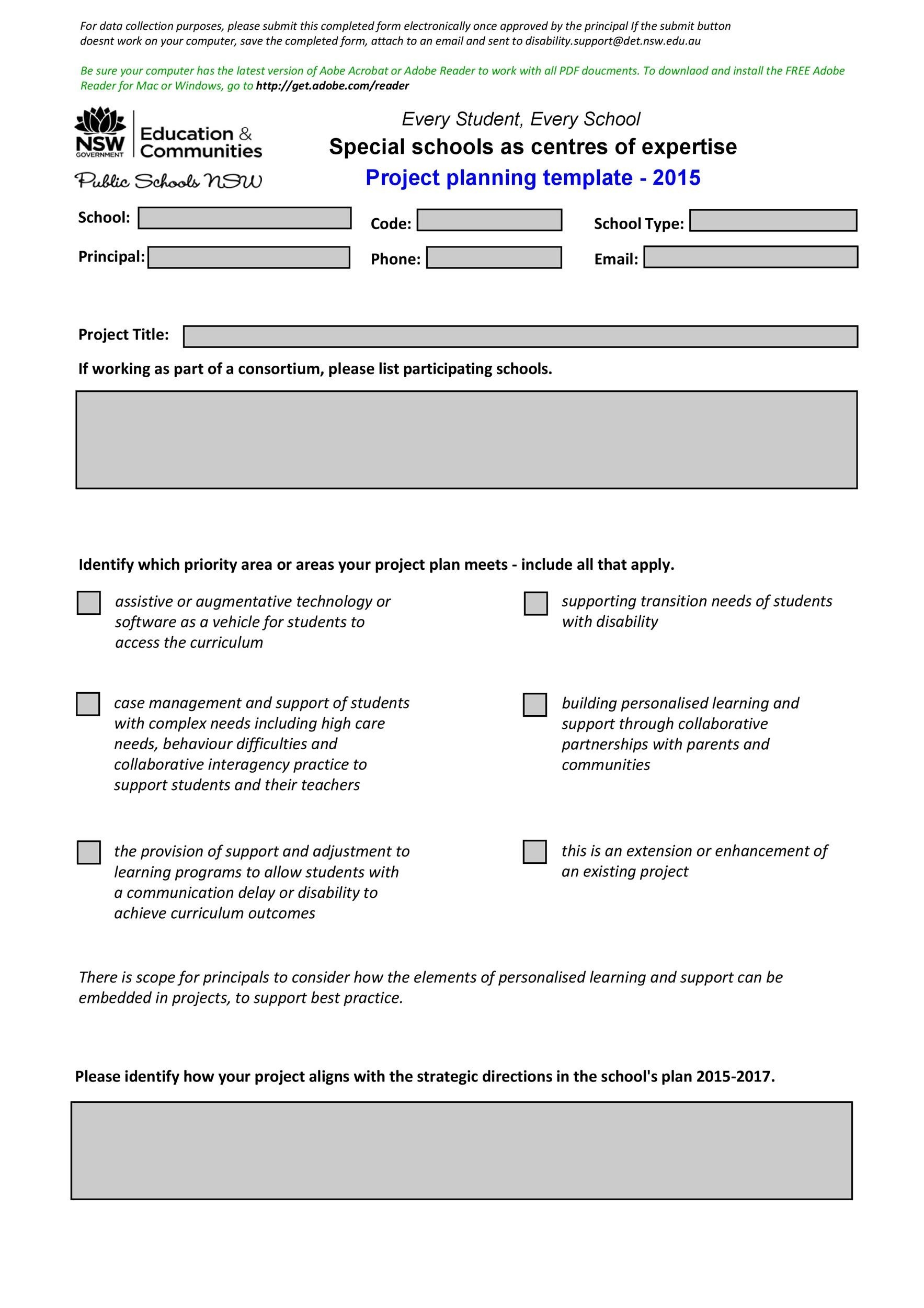
DEPARTMENT OF DEFENSE TECHNOLOGY AND PROGRAM
Programs will employ systems security engineering methods and practices including cybersecurity |
|
SECNAVINST 5510.36B DUSN 12 Jul 2019 SECNAV
Jul 12 2019 Security Plan Template ... Care must be taken to ensure identification of the security plan does not disclose the classified program information ... |
|
Sample insider threat program (itp)plan for industry
Information System Security Manager (ISSM). Verify the implementation of the information system security program and ensure continuous moni- toring |
|
Keeping your Elections Secure
WRITTEN INFORMATION SECURITY PROGRAM (WISP) TEMPLATES. KEEPING YOUR ELECTIONS Election Systems Security Plan. Vendor Risk Management Policy. Page 8 ... |
|
Information Security Plan
Note to agencies – This security plan template was created to align with the ISO and program source code will be controlled and information technology ... |
|
Information Security Program Plan
11 nov. 2015 This is the University of Tennessee Knoxville (UTK) Information Security Program Plan created as result of University of Tennessee (UT) ... |
|
IT Security Procedural Guide: Information Security Program Plan
16 juin 2020 This Information Security Program Plan (ISPP) was developed in order to provide ... template for a generalized contingency plan for all ... |
|
Creating a Written Information Security Plan for your Tax
2 août 2022 As a part of the plan the FTC requires each firm to: ? Designate one or more employees to coordinate its information security program. |
|
Michigan Technological University Information Security Plan
Security and Information Compliance Officers are responsible for the University's security programs including risk management. They play a leading role in |
|
NIST SP800-18 Guide for Developing Security Plans for Federal
Appendix A provides a system security plan template. security programs including the coordination of information security efforts throughout. |
|
Action Plan for the Implementation of the Cyber Security Concept of
National Strategy for Information Security in the Slovak Republic approved by Slovak Submit the multi-departmental budget program titled. “Protection ... |
|
NMSU-system-Written-Information-Security-Program.pdf
GLBA's Safeguards Rule which requires universities to develop a written information security plan that describes their program to protect customer |
|
SECNAVINST 5510.36B DUSN 12 Jul 2019 SECNAV
12 juil. 2019 (3) Department of the Navy Information Security Program. Overview ... related to the DON Security Programs; ... An “Emergency Plan Template”. |
|
Security-plan-example.pdf
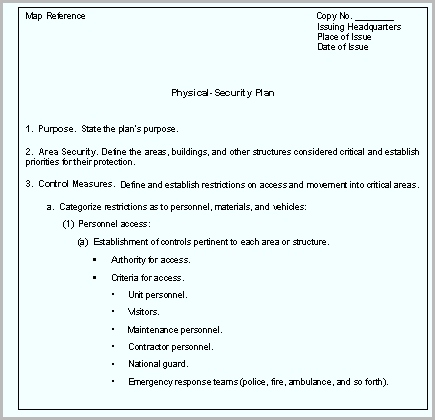
with NERC Standard CIP-006-2 Physical Security Program for the Protection of Critical. Cyber Assets. Maintenance and testing (R8) is described in this plan |
|
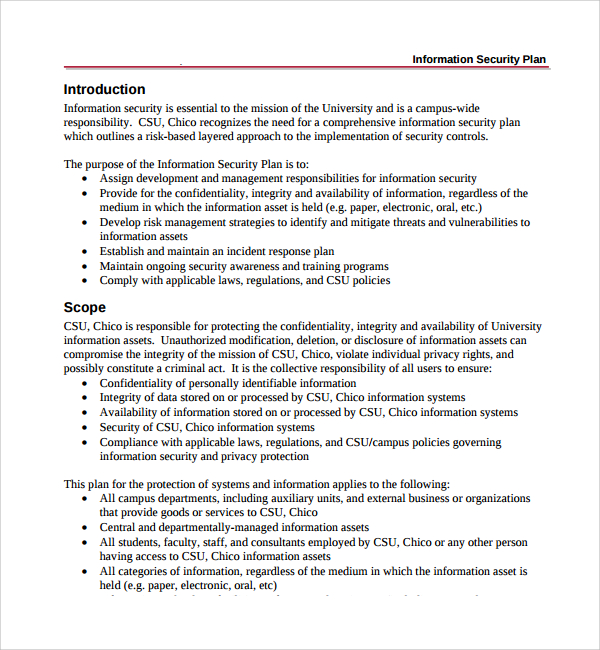
Information Security Plan - Oregongov
Information security is the protection of information from a wide range of threats in order to ensure business continuity minimize business risk and maximize return on investments and business opportunities Information security is achieved by implementing a suitable set of controls including |
|
Information Security Plan - Michigan Technological University
Information Security Policy ID AM-6 Cybersecurity roles and responsibilities for the entire workforces and third-party stakeholders (e g suppliers customers partners) are established Acceptable Use of Information Technology Resource Policy Information Security Policy Security Awareness and Training Policy Identify: Risk Management Strategy |
|
Information Security Plan - Michigan Technological University
An Information Security Plan (ISP) is designed to protect information and critical resources from a wide range of threats in order to ensure business continuity minimize business risk and maximize return on investments and business opportunities |
|
Creating a Written Information Security Plan for your Tax
Sample Template Written Information Security Plan (WISP) For [Your Firm Name Here] This Document is for general distribution and is available to all employees This Document is available to Clients by request and with consent of the Firm’s Data Security Coordinator |
|
Guide for developing security plans for federal information
Guide for Developing Security Plans for Federal Information Systems Authority This document has been developed by the National Institute of Standards and Technology (NIST) in furtherance of its statutory responsibilities under the Federal Information Security Management Act of 2002 Public Law 107-347 |
|
Information Security Plan - Oregongov
Note to agencies – This security plan template was created to align with the ISO 27002:2005 standard and to meet the requirements of the statewide Information |
|
Information Security Program Plan
11 nov 2015 · This plan details the information security risks facing the UTK Campus as well as the disposition of mitigating or compensating controls |
|
Sample Written Information Security Plan - State Bar of Wisconsin
Appendix B Sample Written Information Security Plan I OBJECTIVE: Our objective in the development and implementation of this written information |
|
Michigan Technological University Information Security Plan
The Information Security Plan establishes and states the policies governing Michigan Technological University's IT standards and practices |
|
INFORMATION SECURITY PLAN - Kilgore College
SUMMARY An Information Security Plan provides direction for managing and protecting the confidentiality integrity and availability of information |
|
(DOC) Cyber Security Plan Template Zain Ahmed - Academiaedu
Cyber Security Plan Template Download Free PDF Software risk is a condition that can result failure of software project and loss in terms of cost |
|
Information Security Program Plan (ISPP) CIO-IT Security-18-90 - GSA
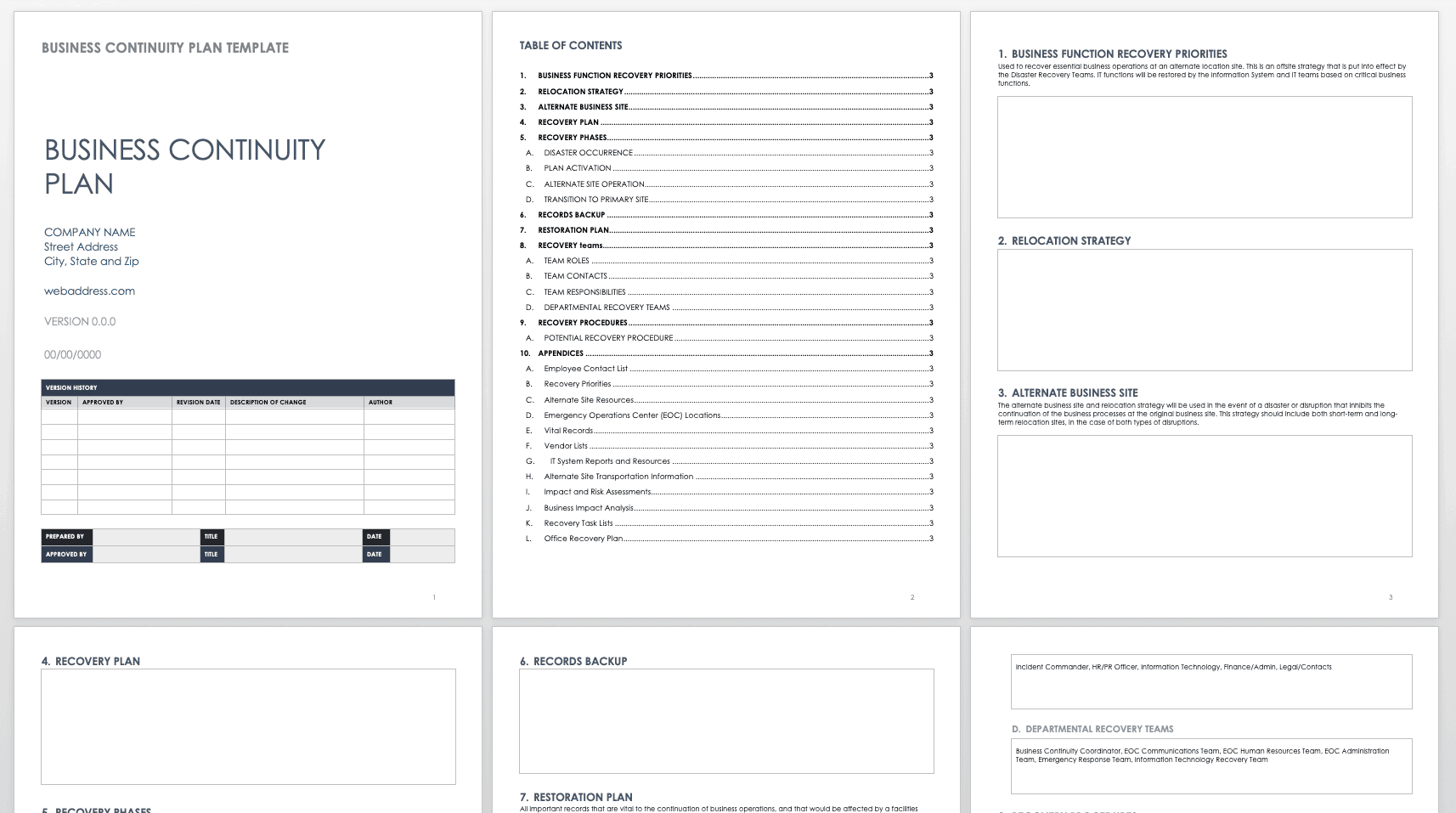
16 jui 2020 · Organizations may choose for example to implement the Contingency Planning security control (CP-2) as a predefined template for a generalized |
|
Information Security Program Plan CIO-IT Security-18-90 - GSA
Organizations may choose for example to implement the Contingency Planning security control (CP-2) as a predefined template for a generalized contingency plan |
|
Template for Cyber Security Plan Implementation Schedule
This action in combination with the other elements of insider mitigation program supports addressing the insider threat The critical group of the Insider |
What is an information security plan?
- Information Security Plan Page 4 Rev: 3 – 10/13/2011 1 EXECUTIVE SUMMARY An Information Security Plan (ISP) is designed to protect information and critical resources from a wide range of threats in order to ensure business continuity, minimize business risk, and maximize return on investments and business opportunities.
What documents should be included in a security plan?
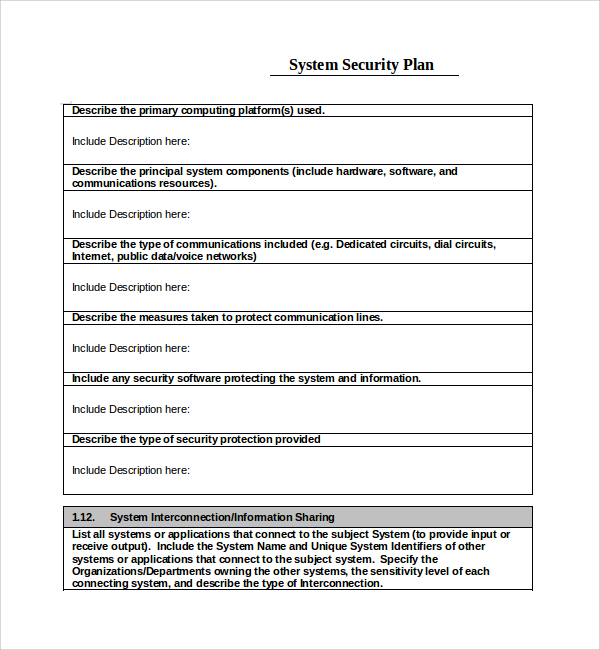
- The plan also may reference other key security-related documents for the information system such as a risk assessment, plan of action and milestones, accreditation decision letter, privacy impact assessment, contingency plan, configuration management plan, security configuration checklists, and system interconnection agreements as appropriate.
What should a system security plan include?
- System security plans should clearly identify which security controls employed scoping guidance and include a description of the type of considerations that were made. The application of scoping guidance must be reviewed and approved by the authorizing official for the information system.
Which NIST publications support the preparation of a security plan?
- Other key NIST publications directly supporting the preparation of the security plan are NIST SP 800-30, Risk Management Guide for Information Technology Systems, and NIST SP 800-37, Guide for the Security Certification and Accreditation of Federal Information Systems.
|
Information Security Plan - State of Oregon
Note to agencies – This security plan template was created to align with the ISO and program source code will be controlled and information technology |
|
Sample Information Security Program
The Program Coordinator shall conduct a risk assessment to identify reasonably foreseeable internal and external risks to the security, confidentiality and integrity |
|
Sample Written Information Security Plan - State Bar of Wisconsin
3) Use software program that requires each employee to enter a unique log-in ID to access computer records, and to re-log-in when the computer is inactive for |
|
Template for the Cyber Security Plan Implementation - NRCgov
The insider mitigation program critical group has been expanded to include addressing cyber security staff in accordance with RG 5 77, and was completed by |
|
IT Security Plan - University of South Florida
The USF IT Security Plan defines the information security standards and procedures for increases security or adds new features to a software program |
|
Information Security Program Plan - Office of Information Technology
11 nov 2015 · Areas that fall under the scope of industry, regulatory, or legal requirements, for example, often require additional controls The most common of |
|
Security Plan Example - Federal Energy Regulatory Commission
(Utility)'s security program, and in some sections, makes reference to other relevant plans and information and procedures associated with this Security Plan |
|
Information Security Program Plan CIO-IT Security-18-90 - GSAgov
the Contingency Planning security control (CP-2) as a predefined template for a GSA's enterprise-wide Information Security Program Plan, Revision 2, |
|
Security Plan Template for Major Applications and General Support
A General Support System is an "interconnected set of information resources under protecting shared data must be included with this security plan A 10 Applicable Describe the awareness program for the application/system C 9 Incident |
|
System Security Plan Template
MISP Ministry Information Security Program ISO Information Security Office AA Approving Authority CA Certification Authority SSP System Security Plan |

![48 Professional Project Plan Templates [Excel Word PDF] ᐅ 48 Professional Project Plan Templates [Excel Word PDF] ᐅ](https://0.academia-photos.com/attachment_thumbnails/56669537/mini_magick20190111-3530-1obb8rd.png?1547252037)

![48 Professional Project Plan Templates [Excel Word PDF] ᐅ 48 Professional Project Plan Templates [Excel Word PDF] ᐅ](https://www.tylercybersecurity.com/hs-fs/hubfs/images/Sample-Information-Security-Program.png?width\u003d1200\u0026name\u003dSample-Information-Security-Program.png)