insider threat activities
|
Insider Threat Indicators in User Activity Monitoring Job Aid
policies require User Activity Monitoring (UAM) on classified networks in support of. Insider Threat Programs for: • DoD Components under DoDD 5205.16. |
|
Insider Threat Mitigation for U.S. Critical Infrastructure Entities
19 mar. 2021 Among other activities foreign threat actors are collecting large sets of public and non-public data about these organizations and their ... |
|
Insider threat and Extremist activity WITHIN THE DOD
INSIDER THREAT AND EXTREMIST. ACTIVITY. WITHIN THE DOD. CENTER FOR DEVELOPMENT OF SECURITY. EXCELLENCE (CDSE). UNCLASSIFIED. 5/9/2022. UNCLASSIFIED |
|
Insider Threat Study: Illicit Cyber Activity in the Banking and Finance
Previous efforts have been made to study insider incidents including workshops to develop a foundation of knowledge on insider threats;3 annual surveys of |
|
Combating the Insider Threat
2 mai 2014 An insider threat is generally defined as a current or former employee ... Some Behavioral Indicators of Malicious Threat Activity:4 |
|
Student Guide - Privacy and Civil Liberties Overview
However Insider Threat program personnel need to be careful not to overstep the 5th Amendment when conducting activities or inquiries. 9th Amendment. Page 8 |
|
Basic Hub Operations Student Guide
Course Introduction Functions of an Insider Threat Hub |
|
ADVISORY: Insider Threat Competency Resource Guide
30 août 2017 This CRG addresses key work activities and competencies required to deter detect |
|
INSIDER THREAT
II. INSIDER THREAT PROGRAM PERSONNEL. III. EMPLOYEE TRAINING AND AWARENESS. IV. ACCESS TO INFORMATION. V. MONITORING USER ACTIVITY ON NETWORKS. |
|
National Insider Threat Policy and the Minimum Standards
Critical program requirements include but are not limited to: (1) monitoring user activity on classified computer networks controlled by the Federal. Government |
|
Insider Threat Mitigation Guide - CISA
Costs-of-Insider-Threats-in-this-New-Infographic pdf Broadly insider threats originate from two primary kinds of activity: unintentional and |
|
Insider Threat Tip Card - CISA
Shows signs of drug or alcohol abuse financial difficulties gambling illegal activities poor mental health or hostile behavior IF YOU'VE BEEN COMPROMISED |
|
(PDF) Insider threats in Cyber Security: The enemy within the gates
PDF Insider threats have become reality for civilian firms such as Tesla which experienced sabotage and intellectual property theft and Capital One |
|
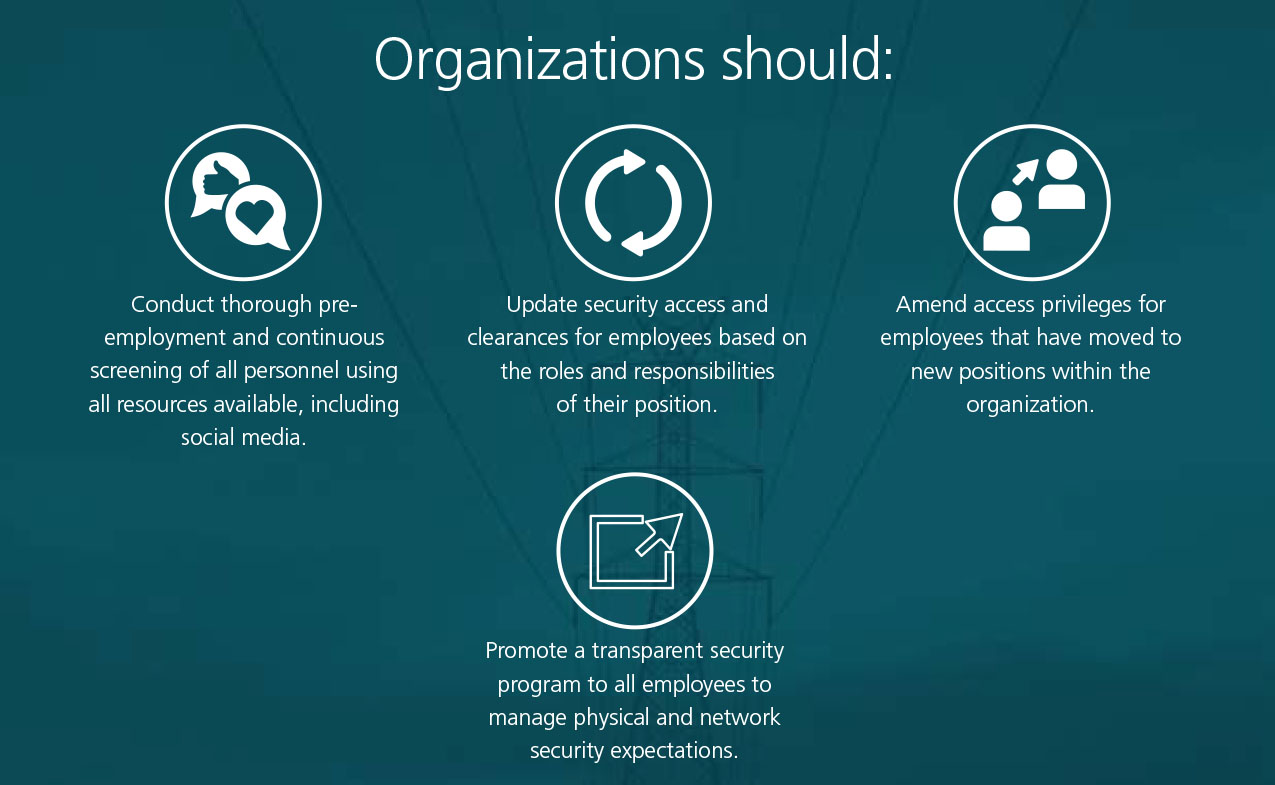
Managing insider threat EY
document considers insider threats stemming from intentional fraudulent or criminal activities To combat this insidious type of threat organizations need |
|
Insider Threat Awareness (INT101) Student Guide - CDSE
Recognize insider threat counterintelligence and security reporting recommendations Lesson 1 activities or contractual relationship with DoD |
|
Insider Threat Potential Risk Indicators (PRI) - JOB AID - CDSE
Some PRI may involve activities that are constitutionally protected Timely and appropriate reporting of PRI is crucial for assessing and mitigating insider |
|
Insider Threat Study: Illicit Cyber Activity in the Banking and Finance
Pittsburgh PA 15213-3890 Insider Threat Study: Illicit Cyber Activity in the Banking and Finance Sector CMU/SEI-2004-TR-021 ESC-TR-2004-021 |
|
How to Build an Insider Threat Program in 10 Steps by Ekran System
The 2020 Cost of Insider Threats: Global Report [PDF] by the control user activity spot security threats and stop them Our clients augment their |
|
ICAO INSIDER THREAT TOOLKIT
1 août 2022 · security concern; reduce the risk of insider activity; and protect an organization's assets INSIDER THREAT TOOLKIT A malicious insider |
|
INSIDER THREAT PROGRAM MATURITY FRAMEWORK
anomalous activity and potential insider threats ME15: Employs behavioral science methodologies to help identify indicators of potential insider threats |
What is insider threat activity?
Overview.
. An insider threat refers to a cyber security risk that originates from within an organization.
. It typically occurs when a current or former employee, contractor, vendor or partner with legitimate user credentials misuses their access to the detriment of the organization's networks, systems and data.What are the four types of insider threats?
Insider threats manifest in various ways: violence, espionage, sabotage, theft, and cyber acts.What are the 3 phases of insider threat?
The key steps to mitigate insider threat are Define, Detect and Identify, Assess, and Manage.
. Threat detection and identification is the process by which persons who might present an insider threat risk due to their observable, concerning behaviors come to the attention of an organization or insider threat team.- Types of insider threats
Departing employees: Employees leaving the company voluntarily or involuntarily are among the most common insider threats.
. They might take materials they're proud of to help land a new job or, more viciously, steal and expose sensitive data out of revenge.
|
Insider Threat Mitigation Guide - CISA
have an equivalent capability to monitor and respond to insider activities, especially the malicious disruptions that are a frequent expression of insider threats |
|
Insider Threat - CISA
Shows signs of drug or alcohol abuse, financial difficulties, gambling, illegal activities, poor mental health, or hostile behavior Report incidents, phishing attempts, malware, and vulnerabilities computer or network vulnerabilities to US-CERT via the hotline: 1-888-282-0870 or www us- cert |
|
Insider Threat - CDSE
Trusted insiders may commit malicious acts, such as fraud, theft, sabotage, espionage, unauthorized disclosure, workplace violence, and more Unwitting insiders may inadvertently disclose sensitive information, unknowingly download malware, or facilitate other cybersecurity events |
|
Insider Threat Detection Study - NATO Cooperative Cyber Defence
This data is entirely based on convicted insiders who had malicious intent It does not reflect unintentional insider activities and the risk they pose to an |
|
Insider Threat Report: Trends and Analysis - Fortinet
Because insiders often have elevated access privileges to sensitive data and applications, it becomes increasingly difficult to detect malicious activity (60 ) |
|
INSIDER THREAT - Office of the Director of National Intelligence
INSIDER THREAT PROGRAM PERSONNEL III EMPLOYEE TRAINING AND AWARENESS IV ACCESS TO INFORMATION V MONITORING USER ACTIVITY |
|
Insider Threat Program Best Practices - PAE Security Portal
The continued collection and retention of relevant events or contextual information is critical to performing monitoring and response for insider threat mitigation |