insider threat use cases
|
Practical Applications in Splunk for Insider Threat Detection and
• Practical uses of ML and AD in various security and insider threat uses cases. • Advanced use-cases. • Wrap up and Questions. 4. Page 5. Why I Want To Talk To |
|
EXABEAM TOP 12 UEBA USE CASES
ALL RIGHTS RESERVED. DETECT INSIDER THREATS AND ACCELERATE INCIDENT RESPONSE. 1. Compromised User Credentials: This is table stakes for UBA. The solution |
|
Insider Threat Mitigation Guide
Case Study. When an Insider Becomes an Insider Threat. The case that follows demonstrates how the trusted employee and the use of their authorized access or |
|
Technical Detection Methods for Insider Risk Management
A Use-Case Based Approach to Insider Threat Control. Implementation and Operation. Identify insider threats to critical. Assets. Establish an insider threat. |
|
UEBA USE CASE: INSIDER ATTACK IDENTIFICATION WITH
Sep 4 2017 Aruba IntroSpect's User and Entity Behavioral Analytics (UEBA) automates the detection of insider threats from malicious. |
|
WHITE PAPER
This use case can also be classified as data spillage. Malicious Activity is the purposeful compromise of internal resources by disgruntled employees or |
|
Design and Implementation of a Comprehensive Insider Threat
use case applications of a comprehensive insider threat ontology—“Sociotechnical and Organizational Factors for Insider Threat” (SOFIT)—that comprises more ... |
|
How to Mitigate Insider Threat With Splunk UBA
Splunk UBA detects insider threats using out-of-the-box use cases that use unsupervised machine learning algorithms. Page 5. © 2020 SPLUNK INC. Splunk UBA |
|
Insider-threat-best-practices-guide.pdf
insider threat firms should use both technical tools and human intelligence. ... FBI and DHS |
|
Common Sense Guide to Mitigating Insider Threats Fifth Edition
The CERT insider threat corpus currently includes more than 1000 cases of insider threat This case illustrates several methods an insider may use to ... |
|
SEC1305: Detecting and Mitigating Insider Threats Using MLTK and
In many Insider Threat cases the activity begins with a user logging in at an abnormal time. ?Network Logs. • Traffic Flow through your web proxy |
|
Practical Applications in Splunk for Insider Threat Detection and
Insider Threat Cyber |
|
Insider threat detection: Where and how data science applies
Derek's prior machine learning works from Pivotal Software include the consultation and building of data science-based solutions for custom security use cases |
|
CERT Insider Threat Center
threat cases contains information we've used to learn about and analyze insider threats. We use system dynamics modeling to characterize the nature of the |
|
Insider Threat Mitigation Guide
insider who uses their access and knowledge to harm an organization. In every case effective insider threat mitigation programs need to be able to ... |
|
Design and Implementation of a Comprehensive Insider Threat
We describe the development and envisioned use case applications of a comprehensive insider threat ontology—“Sociotechnical and Organizational Factors for |
|
An Insider Threat Indicator Ontology
We make the case for using an ontology to fill the stated gap in the insider threat community. We also describe the semi-automated data-driven development of |
|
How to Mitigate Insider Threat With Splunk UBA
Splunk UBA detects insider threats using out-of-the-box use cases that use unsupervised machine learning algorithms. Page 5. © 2020 SPLUNK INC. Splunk UBA |
|
An integrated approach to insider threat protection
including IBM Guardium users can enrich their data security monitoring and threat detection use cases to focus specifically on insider threat activities. |
|
An extended misuse case notation: Including vulnerabilities and the
The original misuse case notation adds inverted use cases to model threats and vulnerabilities and the insider threat and discusses the use of this ex-. |
|
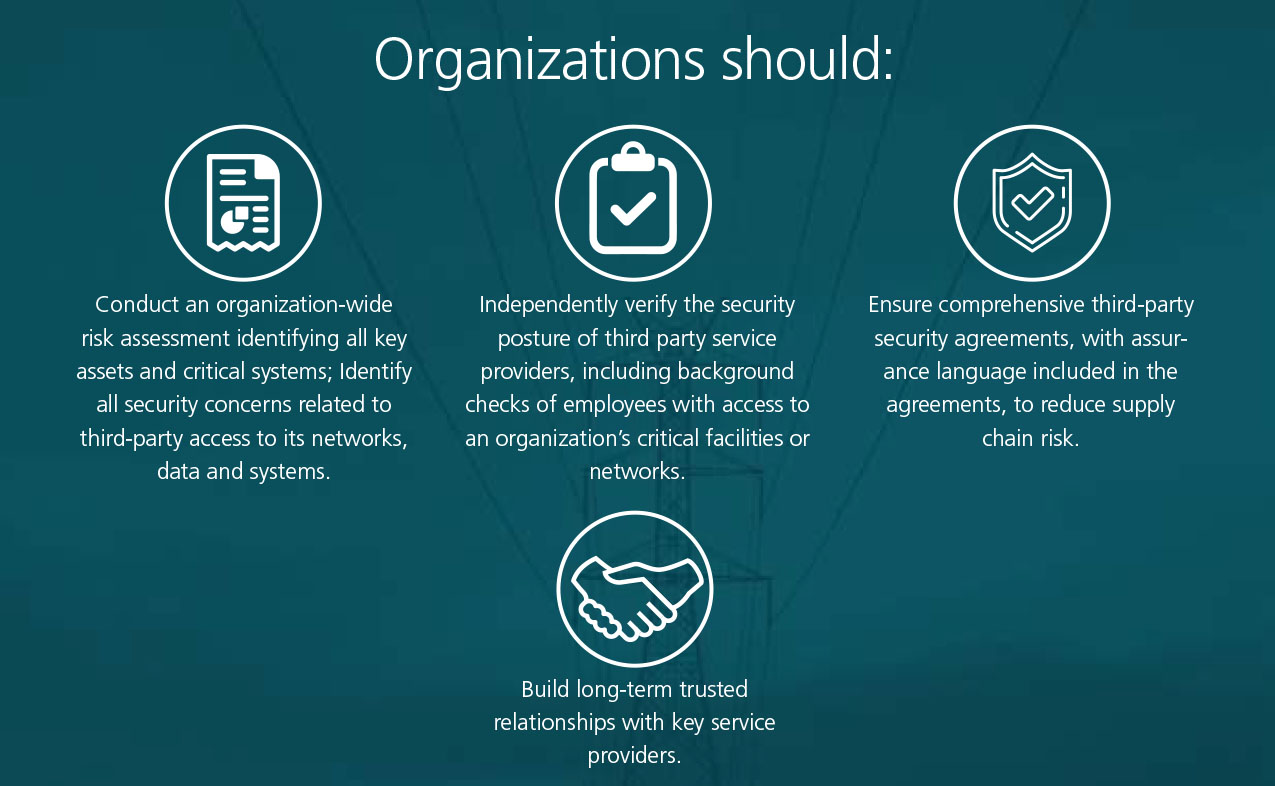
Insider Threat Mitigation Guide - CISA
Through a case study approach this Guide details an actionable framework for an effective insider threat mitigation program: Defining the Threat |
|
Insider Threat Detection Study CCDCOE
This study focuses on the threat to information security posed by insiders (i e insider threat) as the recent cases of Edward Snowden Chelsea Manning |
|
Insider-threat-best-practices-guidepdf - SIFMA
An effective insider threat program therefore uses both cybersecurity defenses and designated intelligence personnel to detect and contain insiders who pose a |
|
Cyber Security Division - Insider Threat
Cyber Security Division - Insider Threat The real threats posed by trusted insiders Cybersecurity measures are frequently focused on threats |
|
An Overview of Insider Threat Management
Use Cases Section 5: Industry-Specific Threats Concerns Introduction Conclusion and Next Steps Key Findings AN OVERVIEW OF INSIDER THREAT |
|
Insider threat detection: Where and how data science applies
Derek's prior machine learning works from Pivotal Software include the consultation and building of data science-based solutions for custom security use cases |
|
PREVENTING INSIDER THREATS WITH UEBA Exabeam
Insider Threats refer to malicious activity against an In other cases as they are duplicated for a variety of uses including |
|
Insider Threat Study: Illicit Cyber Activity in the Banking and Finance
and commercial use should be addressed to the SEI Licensing Agent and implications specific to research conducted on insider threat cases in the |
|
Insider Threat Study: Illicit Cyber Activity - Carnegie Mellon University
obtained using system logs 27 In 30 of cases forensic examination of the targeted network system or data or of the insider's home or work equipment |
|
Insider threat: a potential challenges for the information security
PDF The growth of insider threat is ever expanding it proliferation in Case study: A disgruntled employee of the organization is the software |
|
Insider threat detection - Exabeam
Derek's prior machine learning works from Pivotal Software include the consultation and building of data science-based solutions for custom security use cases for |
|
Development of a Methodology for Customizing Insider Threat
An intent-based insider threat risk assessment methodology is presented to create use case scenarios tailored to address an organization‟s specific security |
|
Insider Threat Detection Study - NATO Cooperative Cyber Defence
Therefore, malicious use of PII has inherently lower risk associated with it Additionally, organised crime involvement was noted in cases with the greatest |
|
Insider threats Case Study_1 - StreamAnalytix
customer-facing and operational applications The bank was struggling to deploy timely threat detection use cases with its existing solution It took almost 2 years |
|
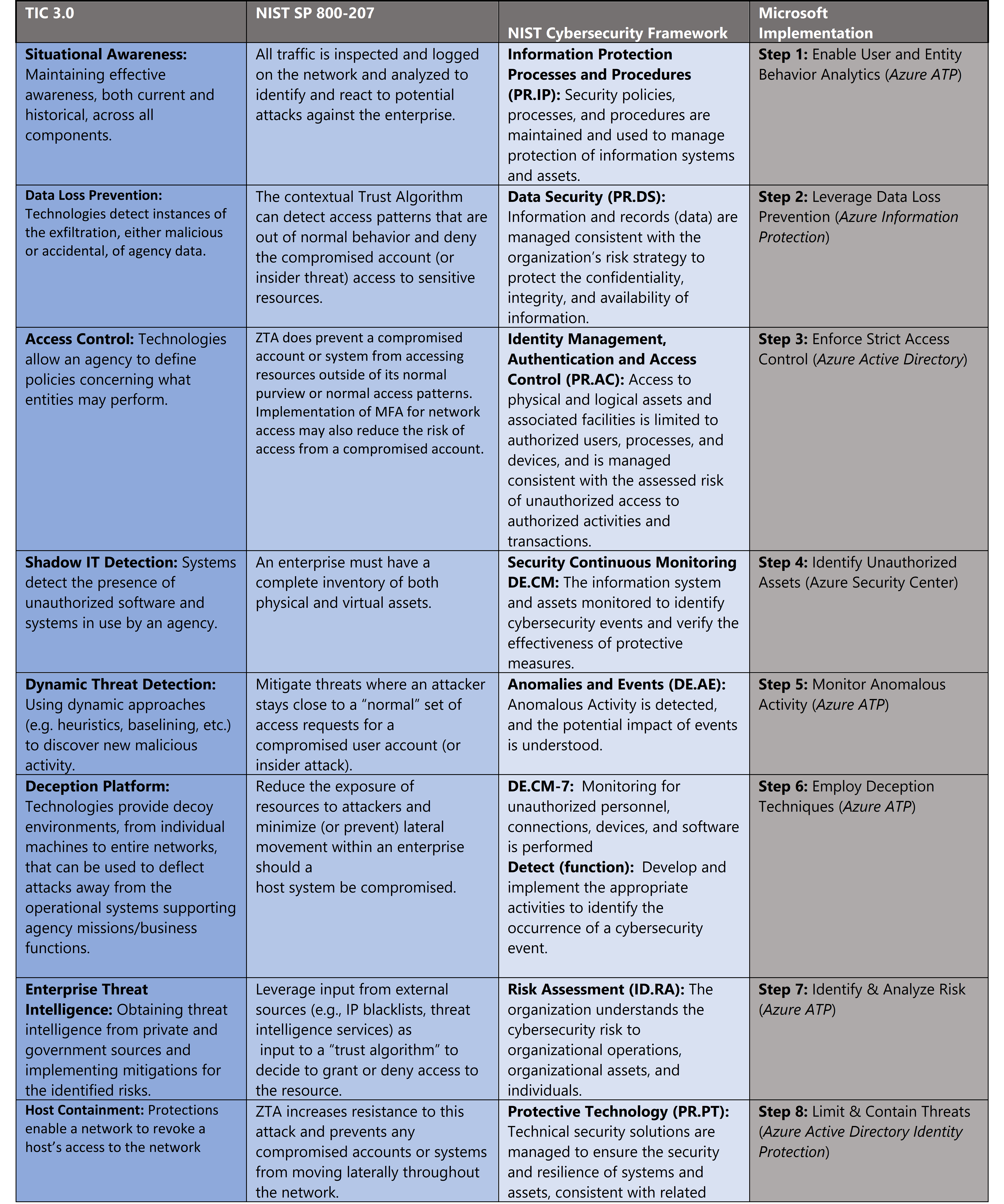
Review of different security technologies to tackle insider threats
The paper analysis the technologies in light of the common insider threat use- cases and is meant to serve as a guide for IT decision makers during their selection |
|
The Increasing Threat from Inside - Oliver Wyman
This means refocusing the organization's efforts on practical use cases that support the development of a data-driven, risk-focused, and proactive insider risk |
|
Insider Threat Mitigation Guide - CISA
Through a case study approach, this Guide details an actionable framework for an effective insider threat mitigation program: Defining the Threat, Detecting and |
|
Managing insider threat - EY
An insider threat is when a current or former employee, ease of discussion, we will be using “insider threat program” for the organization to drive use case |
|
Predicting Malicious Insider Threat Scenarios Using Organizational
The unsupervised approach for detecting insider threats was effective in that all insider threat cases had an anomaly measure of above the median score |