adobe reader security block smb
|
Recommendations for Configuring Adobe Acrobat Reader DC in a
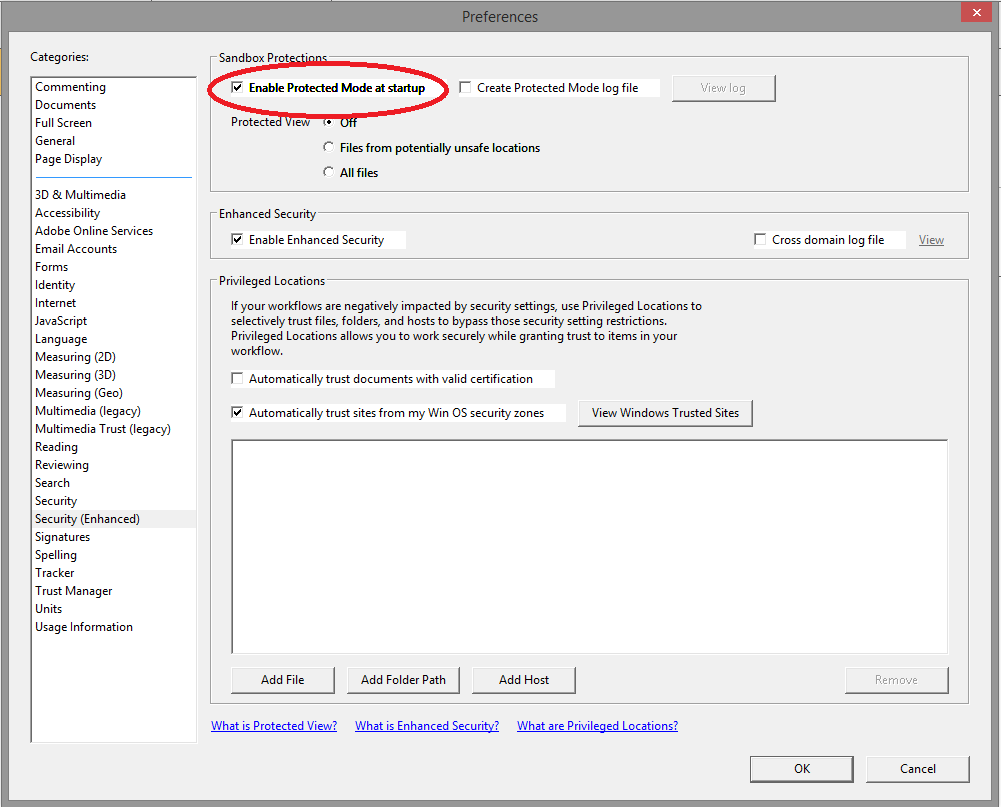
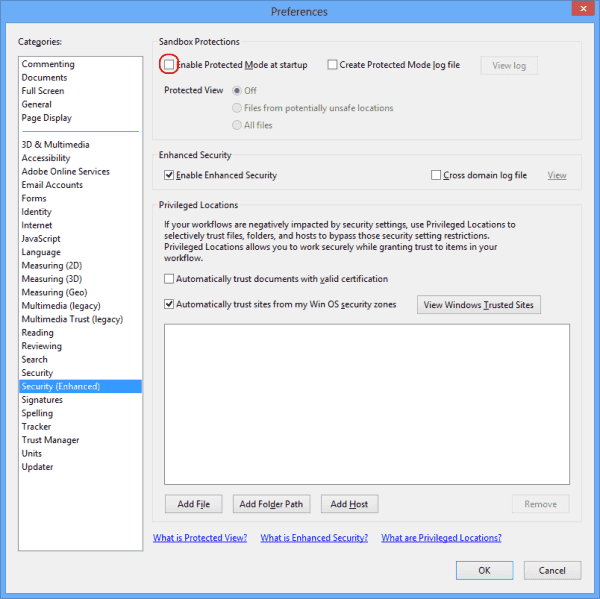
Jan 20 2022 · National Security Agency Cybersecurity Technical Report Recommendations for Configuring Adobe Acrobat Reader DC 1 Introduction The greatest threat to users of Adobe’s Acrobat Reader is opening a PDF file that contains malicious executable content (hereafter referred to as “malicious documents”) The risk of a user receiving such a |
How do I protect my PDF files from cyber attacks?
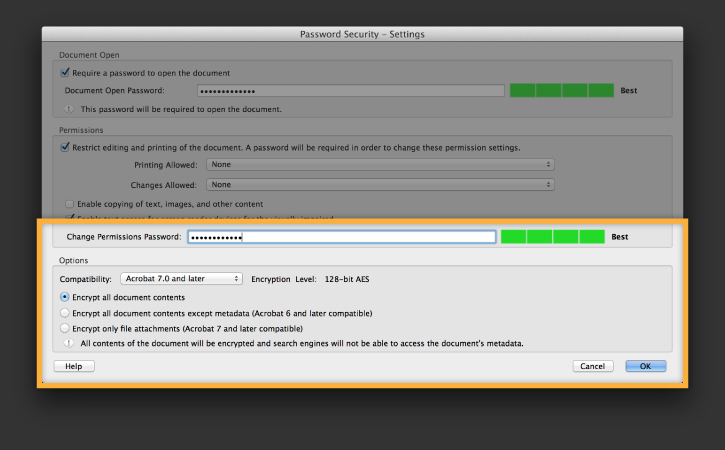
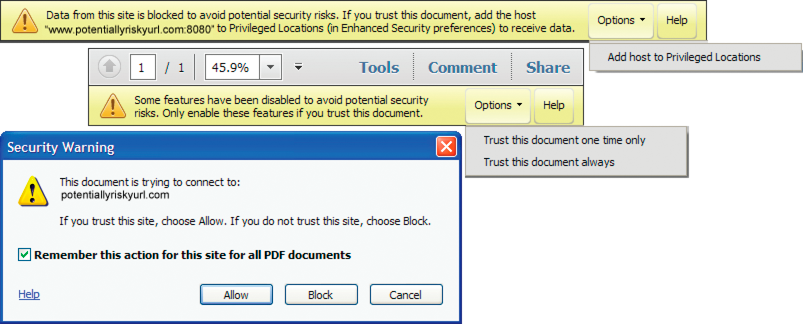
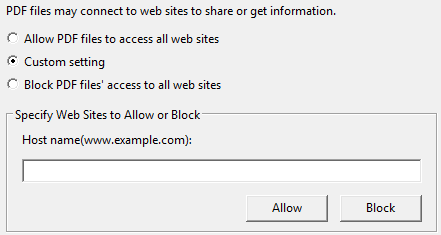
PDFs are commonly exploited by malicious cyber actors. Many security features discussed in this configuration guide can be used to help prevent common attack vectors. Most typical environments can use the Appendix: Configuring Settings for Adobe Acrobat Reader DC as a quick guide to configure Adobe Customization Wizard securely.
What is the greatest threat to Adobe Acrobat Reader?
1. Introduction The greatest threat to users of Adobe’s Acrobat Reader is opening a PDF file that contains malicious executable content (hereafter referred to as “malicious documents”). The risk of a user receiving such a document through email or web surfing is high.
What is a sandbox in Adobe Acrobat Reader DC?
Adobe’s Acrobat Reader DC (herein “Reader”) can run in a sandboxed process to help protect the user from malicious documents. Acrobat Reader DC is the latest version and replaces Acrobat Reader XI. The “DC” in the title stands for “Document Cloud,” which refers to the cloud-based features introduced in Acrobat Reader DC.
|
Recommendations for Configuring Adobe Acrobat Reader DC in a
Prior to the existence of the Protected Mode sandbox the typical security practice was to disable all JavaScript to prevent execution of malicious scripts. |
|
Adobe
improved and extended to Reader. PV is a highly secure read-only mode that blocks most actions and application behavior until the user decides whether or |
|
Registry-level preferences provide Admins with granular control
When configuring paths use your product (Adobe Acrobat or Acrobat Reader) and version (e.g. 11.0). For 8.x |
|
HP Wolf Pro Security Edition Datasheet
HP support is included with HP Wolf Pro Security Edition to help get the most from your when Microsoft Office or Adobe Acrobat are installed. |
|
IPS Signature Release Note V7.16.15
1.8.2019 Acrobat Flash Player request for atl.dll over. SMB attempt ... apphelp.dll over SMB attempt ... Acrobat EMF file GIF sub-block memory. |
|
Hardening Microsoft Windows 10 version 21H1 Workstations
example Microsoft provides security baselines for their products on their Microsoft Security Baseline Block Adobe Reader from creating child processes ... |
|
Docs@Work: Securing Mobile Content
their mobile devices for secure enterprise content and collaboration. other PDF viewers such as Adobe Acrobat Reader and Preview in OS X |
|
Xerox® PrimeLink® B9100/B9110/B9125/B9136 Copier/Printer
Adobe the Adobe logo |
|
HP DesignJet and PageWide XL Printers Security Features
Check that the Firewall does not block de CIFS/SMB ports. • Try a basic network configuration connect the printer directly to the computer. Notes: • Direct |
|
WorkCentre 7120 Multifunction Printer System Administrator Guide
Adobe Reader® Adobe Type Manager® |
|
Acrobat Application Security Guide - Adobe
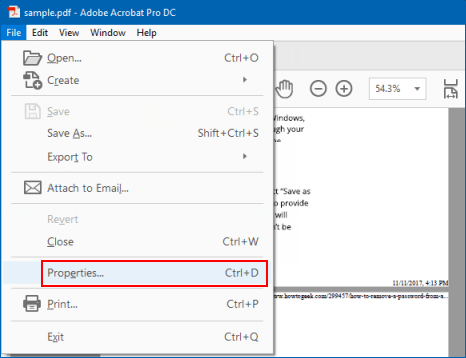
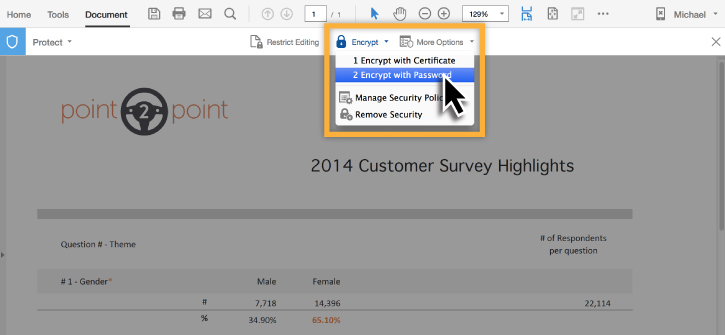
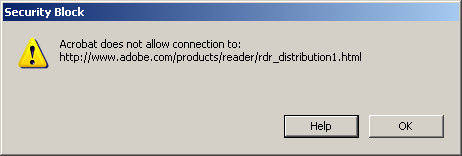
Adobe Application Security Guide for the Adobe® Acrobat Family of Products If this guide is relatively simple: Acrobat products allow you to apply application- wide protections and disable risky features c:test pdf smb://smb_server/xyz data |
|
Acrobat Online Collaboration: Setup and Administration - Adobe
27 juil 2005 · What kind of security is needed for the documents? SMB: Server Zone: mainserver:Users:jsmith:example pdf Since the syntax used in each case is different, Even though a firewall will normally block external access to |
|
IPS Signature Release Note V71615 - Documentation - Sophos
1 août 2019 · Acrobat Flash Player ClbCatQ dll over SMB sub-block memory reference of CVE Identifiers for publicly known information security |
|
MITIGATION OF RANSOMWARE AND MALWARE - EBU tech
Typical broadcast systems use CIFS/SMB file shares in production workflows 4 websites and proactively block advertising networks that are often misused for Turn on enhanced security in Adobe® Reader; protect your machines from |
|
A Curious Exploration of Malicious PDF Documents - SciTePress
PDF Documents, Malware, Malicious PDFs, Security Abstract: The SMB protocol is not the sole possibility here perimeters normally do not block port 80 |
|
Processing Dangerous Paths - Ruhr-Universität Bochum
6 jan 2021 · PDF features relevant for the security and privacy of users can, for example, define a headline, a text block, or an image 1 SMB server |
|
Redaction of PDF Files Using Adobe Acrobat Professional X
National Security Agency 9800 Savage Rd Ft Meade, MD Redaction of PDF files is an ongoing challenge for these entities This document describes how to |
|
Hardening Microsoft Windows 10 version 1709 Workstations
When applications are installed they are often not pre-configured in a secure state sources such as office productivity suites (e g Microsoft Office), PDF readers (e g Adobe terminate or steal a Server Message Block (SMB) session |










/001-prevent-adobe-from-opening-pdfs-in-ie-153338-dd3b1c823717455f93a16eec182c536a.jpg)