modular arithmetic in cryptography
|
Modular Arithmetic and Cryptography!
Modular Arithmetic and Cryptography! Math Circle Thursday January 22 2015. What is Modular Arithmetic? In modular arithmetic |
|
Faster Modular Arithmetic For Isogeny Based Crypto on Embedded
Faster Modular Arithmetic For Isogeny Based Crypto on. Embedded Devices. Joppe W. Bos1 and Simon J. Friedberger12. 1 NXP Semiconductors |
|
10 Modular Arithmetic and Cryptography
10 Modular Arithmetic and Cryptography. 10.1 Encryption and Decryption. Encryption is used to send messages secretly. The sender has a message or plaintext. |
|
Constant-Time Arithmetic for Safer Cryptography
We benchmarked the performance of our library against Go's big.Int library and found an acceptable slowdown of only 2.56× for modular exponentiation |
|
Powers in Modular Arithmetic and RSA Public Key Cryptography
then using modular arithmetic to construct a cipher number by number (or letter by letter) What we will do for RSA cryptography (and what has been done. |
|
E-PGPathshala Subject : Computer Science Paper: Cryptography
Module: Modular Arithmetic. Module No: CS/CNS/6. Quadrant 1 – e-text. Cryptography and Network Security. Module 6-Modular Arithmetic. Learning Objectives. |
|
ArXiv:2001.03741v3 [cs.DS] 4 Feb 2022
4 févr. 2022 Modular arithmetic is at the core of modern cryptography [56]. Modular oper- ... Modular multiplication and addition of two integers a. |
|
Long Modular Multiplication for Cryptographic Applications1
Keywords: Computer Arithmetic Cryptography |
|
Modular Arithmetic and Cryptography!
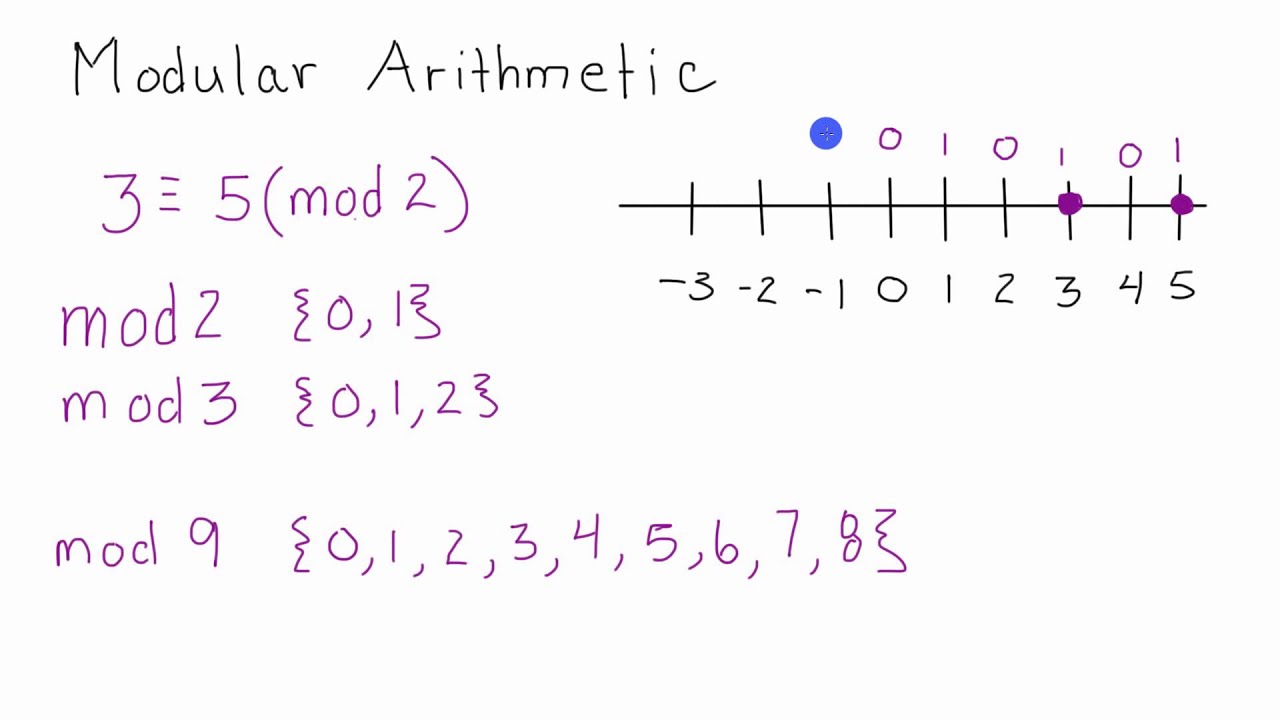
22 jan 2015 · In modular arithmetic we select an integer n to be our “modulus” Then our system of numbers only includes the numbers 0 1 2 3 n-1 |
|
6 Number Theory II: Modular Arithmetic Cryptography and
In this section we will consider modular arithmetic and applications to cryptography and to generating “random numbers” by deterministic computers |
|
10 Modular Arithmetic and Cryptography - Clemson University
10 Modular Arithmetic and Cryptography 10 1 Encryption and Decryption Encryption is used to send messages secretly The sender has a message or plaintext |
|
Contents 1 Classical Cryptosystems and Modular Arithmetic
1 Classical Cryptosystems and Modular Arithmetic In this chapter we discuss the basic ideas of cryptography and a number of historical cryptosystems |
|
Lecture 10: Public Key Cryptography 1 Modular Arithmetic
Today's lecture is about the Public Key Cryptography We first discuss general ideas in designing cryptography protocols Typically the encryption scheme |
|
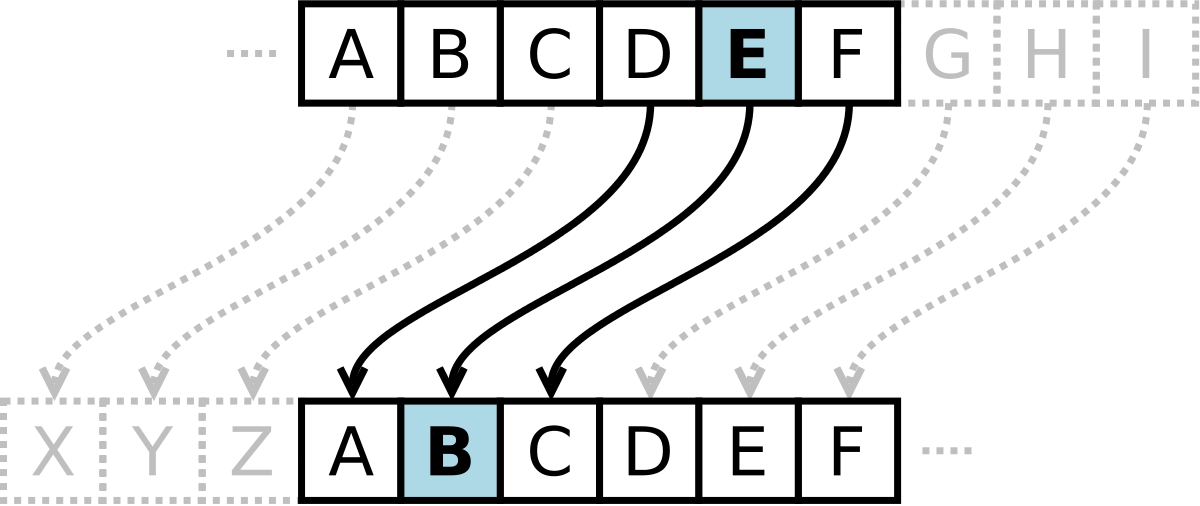
Cryptography and Modular Arithmetic 1 Simple Shift Ciphers
2 oct 2005 · We will introduce some simple methods of encoding that use algebra methods in particular modular arithmetic to encode messages We refer to the |
|
Section 21: Shift Ciphers and Modular Arithmetic
The purpose of this section is to learn about modular arithmetic in cryptography and illustrate a basic cryptographical involving shift ciphers |
|
Modular Arithmetic and Cryptography Author(s): J B Reade Source
Modular arithmetic and cryptography J B READE Even the purest of pure mathematics can have a crucial influence on practical problems |
|
Lecture 5: Finite Fields (PART 2) - PART 2: Modular Arithmetic
24 jan 2023 · PART 2: Modular Arithmetic Theoretical Underpinnings of Modern Cryptography Lecture Notes on “Computer and Network Security” |
What is modular arithmetic in cryptography?
Modular arithmetic is a key ingredient of many public key crypto-systems. It provides finite structures (called “rings”) which have all the usual arithmetic operations of the integers and which can be implemented without difficulty using existing computer hardware.Why is modular arithmetic important for modern cryptography?
One major reason is that modular arithmetic allows us to easily create groups, rings and fields which are fundamental building blocks of most modern public-key cryptosystems. For example, Diffie-Hellman uses the multiplicative group of integers modulo a prime p.What is the difference between modular arithmetic and ordinary arithmetic in cryptography?
Definition. Modular arithmetic is almost the same as the usual arithmetic of whole numbers. The main difference is that operations involve remainders after division by a specified number (the modulus) rather than the integers themselves.- Shift Ciphers work by using the modulo operator to encrypt and decrypt messages. The Shift Cipher has a key K, which is an integer from 0 to 25.
|
Lecture 10: Public Key Cryptography 1 Modular Arithmetic
Today's lecture is about the Public Key Cryptography We first discuss general gorithms, encryption algorithm and decryption algorithm 1 Modular Arithmetic |
|
6 Number Theory II: Modular Arithmetic, Cryptography - Penn Math
In this section we will consider modular arithmetic and applications to cryptography and to generating “random numbers” by deterministic computers 6 1 |
|
10 Modular Arithmetic and Cryptography - Clemson University
10 Modular Arithmetic and Cryptography 10 1 Encryption and Decryption Encryption is used to send messages secretly The sender has a message or plaintext |
|
Contents 1 Classical Cryptosystems and Modular Arithmetic
Most modern cryptography makes heavy use of modular arithmetic and number theory, and most of these methods rely on the assumed difficulty of solving one or more problems in number theory, such as computing discrete logarithms, factoring large integers, and computing square roots modulo composite integers |
|
Studies on Modular Arithmetic Hardware - marcelo kaihara
25 jan 2006 · As noted above, both the encryption and the decryption operations in RSA are mod- ular exponentiations Computation of the modular |
|
Modular Arithmetic and Cryptography
Modular Arithmetic and Cryptography Math Circle Thursday January 22, 2015 What is Modular Arithmetic? In modular arithmetic, we select an integer, n, to be |
|
Topic 1: Cryptography 1 Introduction to Cryptography:
Modular arithmetic is concerned with finding the remainder of integer division with respect to some other given integer n, called the modulus When you divide any |



![PDF] Finite Fields (PART 2) Modular Arithmetic free tutorial for PDF] Finite Fields (PART 2) Modular Arithmetic free tutorial for](https://image2.slideserve.com/4352697/properties-of-modular-arithmetic-l.jpg)


![PDF] Chapter 2 Cryptography and Number Theory 2 1 Cryptography PDF] Chapter 2 Cryptography and Number Theory 2 1 Cryptography](https://i0.wp.com/cryptographystudies.files.wordpress.com/2018/01/modulo-definition.jpg?resize\u003d650)



![PDF] The Basics of Cryptography free tutorial for Beginners PDF] The Basics of Cryptography free tutorial for Beginners](https://0.academia-photos.com/attachment_thumbnails/50640489/mini_magick20190128-32723-10s13z1.png?1548696672)
![PDF] Maximization of Speed in Elliptic Curve Cryptography Using PDF] Maximization of Speed in Elliptic Curve Cryptography Using](https://media.springernature.com/w306/springer-static/cover-hires/book/978-1-4302-1157-0)