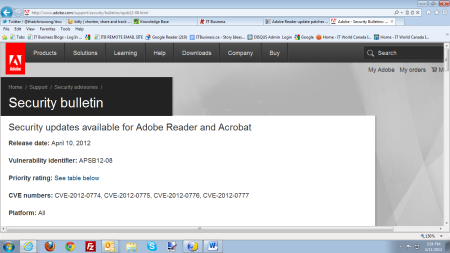
adobe security bulletin priority rating
What is the meaning of priority rating?
Priority Rating means the level of priority assigned to an Incident upon its receipt.
Acrobat Reader versions 20.005. 30539, 23.008. 20470 and earlier are affected by an out-of-bounds read vulnerability that could lead to disclosure of sensitive memory.
An attacker could leverage this vulnerability to bypass mitigations such as ASLR.
|
Vulnerability Disclosure in the Age of Social Media: Exploiting
12 août 2015 http://www.symantec.com/security/OIS_Guidelines%. 20for%20responsible%20disclosure.pdf. [19] Adding priority ratings to adobe security bulletins ... |
|
202010010900_September Vulnerability Bulletin_TLPWHITE
8 sept. 2020 Monthly Cybersecurity Vulnerability Bulletin ... Vulnerabilities this month are from Microsoft Adobe |
|
HC3: Monthly Cybersecurity Vulnerability Bulletin August 15 2022
3 juil. 2022 Department Of Homeland Security/Cybersecurity & Infrastructure Security Agency ... Adobe classifies this as a Priority 2 deployment rating. |
|
HC3: Monthly Cybersecurity Vulnerability Bulletin
HHS Office of Information Security: Health Sector Cybersecurity Vulnerabilities this month are from Microsoft Adobe |
|
Adobe® Incident Response Overview
Response (IR) program includes both proactive security monitoring and and to appropriately rank intelligence based upon necessary course of action. |
|
Vulnerability Disclosure in the Age of Social Media: Exploiting
index [21] and Adobe's priority ratings [19] err on the side of caution by mark- ... of release for a security bulletin |
|
HC3: Monthly Cybersecurity Vulnerability Bulletin September 6
3 août 2022 Department Of Homeland Security/Cybersecurity & Infrastructure Security ... most of these updates as a deployment priority rating of 3 ... |
|
Adobe Social Security Overview
Adobe Social is a social management platform that ties data to your bottom line. A part of the Adobe. Marketing Cloud suite of services Adobe Social goes |
|
Adobe
support for the applicable software products beyond the times mentioned in Adobe Support agreement. Response time objectives are: Priority Severity* |
|
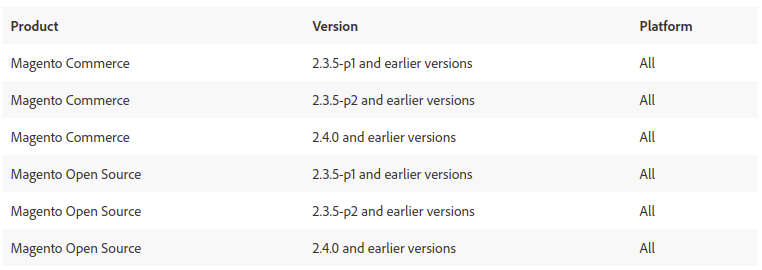
Cybersecurity Vulnerabilities Of Interest to the Health Sector - HHSgov
19 mai 2020 · patches have a priority of critical and as such, should be patched immediately An explanation of Adobe's severity rating system can be found here https:// portal msrc microsoft com/en-US/security-guidance/advisory/CVE- |
|
Advisory
11 nov 2020 · Advisory Adobe Security Updates – November 2020 TLP: White as CVE-2020 -24442 and CVE-2020-24443 – with a priority rating of 3 and |
|
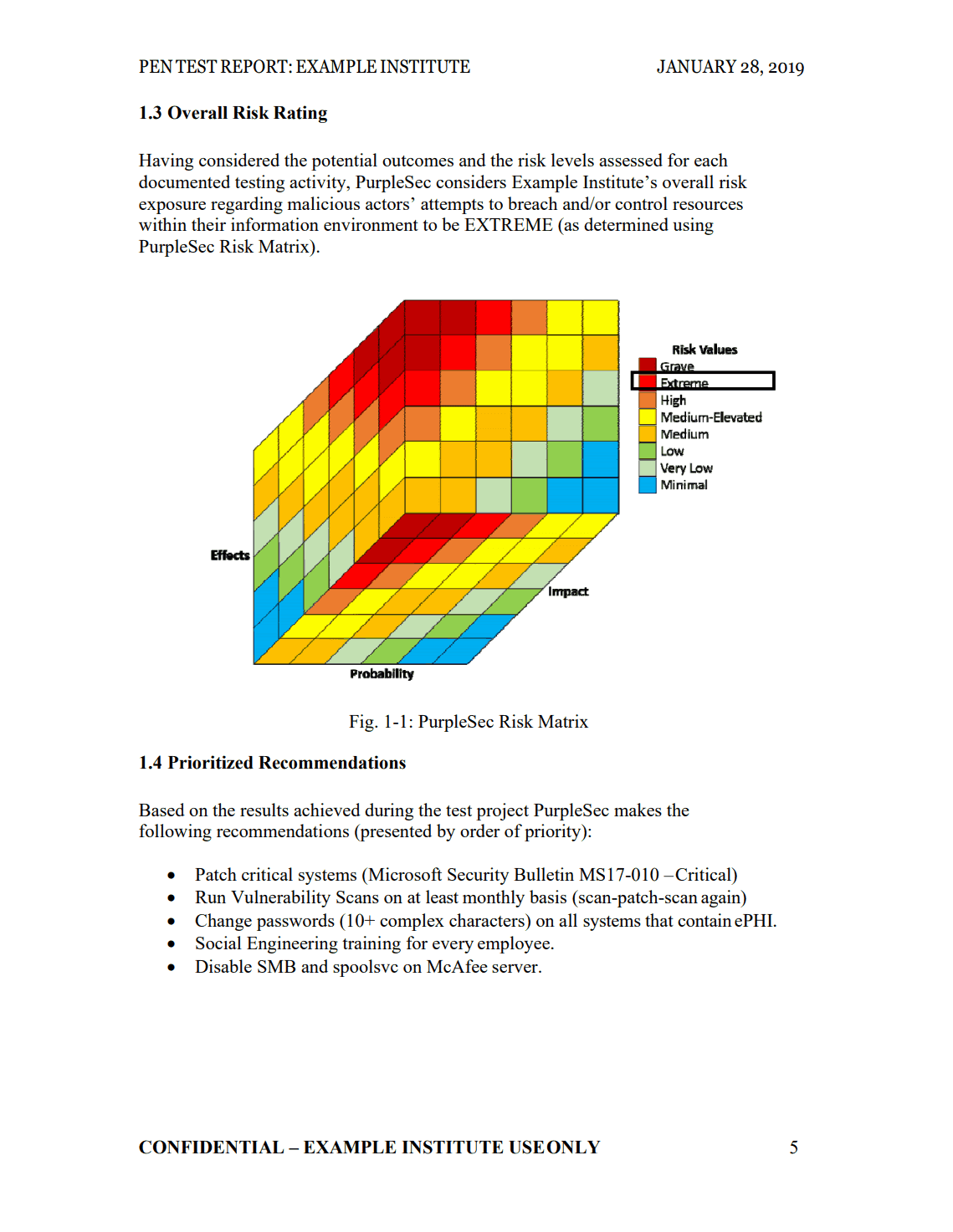
Adobe Security Bulletin - AM-Win
Adobe has released security updates for Adobe Flash Player for Windows, Macintosh Adobe categorizes these updates with the following priority ratings and |
|
T_Bap-E_tech-exploitation_216pdf - DGDR CNRS
http://www adobe com/support/security/bulletins/apsb12-09 html = Adobe categorizes these updates with the following priority ratings and recommends users |
|
Gathering Vulnerability Information Published by Software - IS MUNI
Vulnerability ble 1 1 describes differences between both versions of CVSS score score 2 3 Adobe Adobe provides Security Bulletins and Advisories on its security Priority - published in order to help customers prioritize impor- tant updates |
|
Monthly Security Bulletin Briefing
1 mai 2014 · May 2014 Bulletin Impact Component Severity Priority Exploit Index DoS Rating: T - Temporary (DoS ends when attack ceases) P - Permanent vulnerabilities described in Adobe Security bulletin APSB14-14 |
|
Vulnerability Disclosure in the Age of Social Media - USENIX
12 août 2015 · [54], Microsoft's exploitability index [21] and Adobe's priority ratings [19], err on the side of caution by mark- ing many vulnerabilities as likely to be of release for a security bulletin,2 and 1 for vulnerabil- ities that allowed the |
|
October2020 Vulnerability Bulletin
20 oct 2020 · Monthly Cybersecurity Vulnerability Bulletin Adobe released security update APSB20-58 which addresses a should still be addressed as a priority CVSS rating of 9 8 of 10 and 272 of them can be remotely exploited |






















![Adobe Acrobat Pro DC 2100120140 Crack + Keygen [Latest] Adobe Acrobat Pro DC 2100120140 Crack + Keygen [Latest]](https://media.springernature.com/lw785/springer-static/image/chp%3A10.1007%2F978-3-319-98842-9_4/MediaObjects/462756_1_En_4_Fig8_HTML.gif)