owasp top 10
|
OWASP TOP 10 LES DIX VULNÉRABILITÉS DE SÉCURITÉ
OWASP Top 10 2007. RESUMÉ. A1 - Cross Site Scripting (XSS). Les failles XSS se produisent à chaque fois qu'une application prend des données. |
|
OWASP Top 10 2021
Qu'est-ce que le Top 10 d'OWASP ? Page 4. owasp.org. OWASP. “The Open Web Application |
|
OWASP Top 10 - 2017
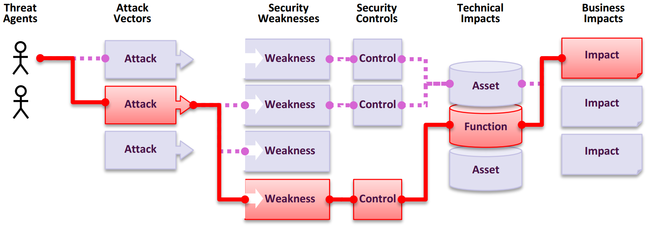
This provides us with confidence that the new OWASP Top 10 addresses the most impactful application security risks currently facing organizations. The OWASP Top |
|
OWASP Top 10 - 2010 FR.pptx
Ce |
|
Copie de OWASP TOP 10 VULNERABILITE
l'authenticité et la non-répudiation. Ils. 1 sont qualifiés d'algorithmes de primitives ou encore de mécanismes cryptographiques. |
|
OWASP Top 10 RC1_PR
19 avr. 2010 L'OWASP vient de mettre à jour le document présentant les 10 risques associés à ... télécharger le Top10 OWASP 2010 à l'URL suivante :. |
|
OWASP Top 10 - 2010
Welcome to the OWASP Top 10 2010! This significant update presents a more concise risk focused list of the Top 10 Most. Critical Web Application Security Risks |
|
OWASP Top 10 - 2013
This release of the OWASP Top 10 marks this project's tenth anniversary of raising awareness of the importance of application security risks. The OWASP Top 10 |
|
Owasp top 10 for java ee the ten most critical web application
The Top 10 provides basic methods to protect against these vulnerabilities – a great start to your secure coding security program. Security is not a one-time |
|
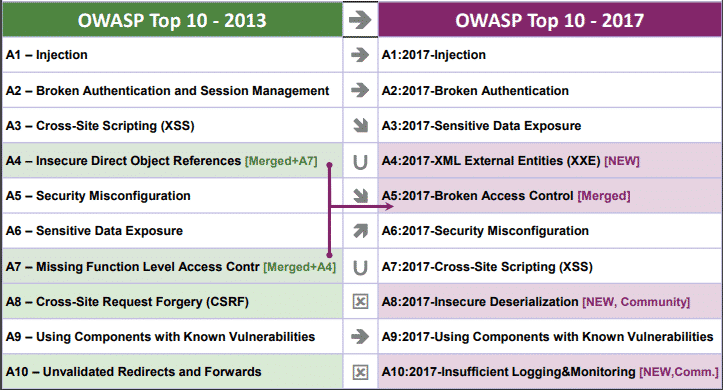
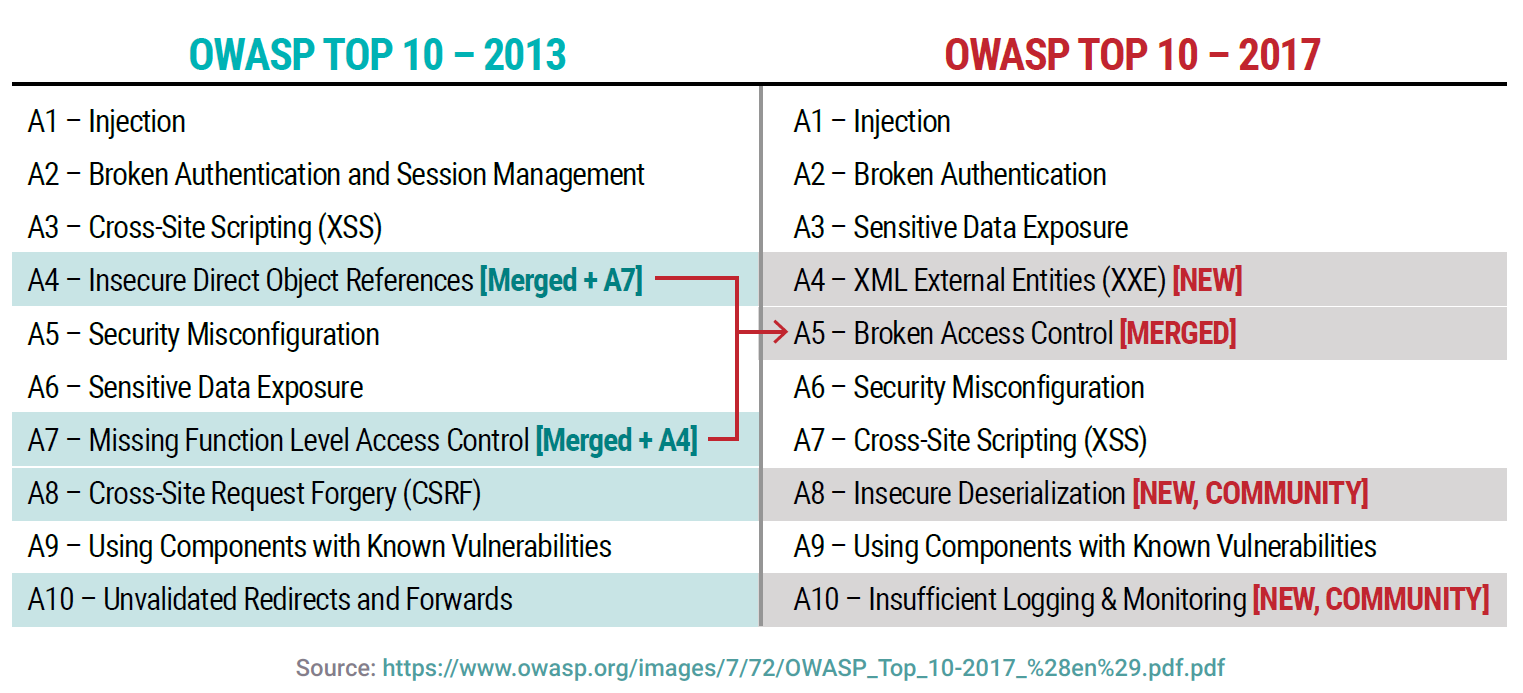
OWASP Top 10 2017
que ceux ajoutés dans le Top 10 2017. Page 8. Ce qui a été ajouté. ? A4 : XML External Entities (XXE) |
|
OWASP Top Ten
The goal of the OWASP Top 10 Proactive Controls project (OPC) is to raise awareness about application security by describing the most important areas of concern that software developers must be aware of We encourage you to use the OWASP Proactive Controls to get your developers started with application security |
|
Searches related to owasp top 10 filetype:pdf
OWASP Top Ten (2010 Edition) http://www owasp org/index php/Top_10 A7 – Insecure Cryptographic Storage Storing sensitive data insecurely Failure to identify all sensitive data Failure to identify all the places that this sensitive data gets stored Databases files directories log files backups etc |
What are the OWASP Top Ten?
- The OWASP Top Ten is a standard awareness document for developers and web application security. It represents a broad consensus about the most critical security risks to web applications. It was started in 2003 to help organizations and developer with a starting point for secure development.
How can the OWASP Top 10 be used to improve the security of web applications?
- One of OWASP’s core principles is that all of their materials be freely available and easily accessible on their website, making it possible for anyone to improve their own web application security. The materials they offer include documentation, tools, videos, and forums. Perhaps their best-known project is the OWASP Top 10.
What are the changes in the OWASP Top 10 for 2021?
- If you’re familiar with the 2020 list, you’ll notice a large shuffle in the 2021 OWASP Top 10, as SQL injectionhas been replaced at the top spot by Broken Access Control. Broken Access Control Cryptographic Failures Injection
|
OWASP Top 10 - OWASP Foundation
OWASP Top 10 - 2017 The Ten Most Critical Web Application Security Risks This work is licensed under a Creative Commons Attribution-ShareAlike 4 0 |
|
Introduction to Application Security and OWASP Top 10 Risks - Part
OWASP Top 10 (c) Creative Commons 3 0 2 Ralph Durkee OWASP: About OWASP = Open Web Application Security Project Dedicated to making application |
|
OWASP Top 10 - 2010 - OWASP Foundation
Welcome to the OWASP Top 10 2010 This significant update presents a more concise, risk focused list of the Top 10 Most Critical Web Application Security Risks |
|
OWASP Top 10 - 2013 - OWASP Foundation
This release of the OWASP Top 10 marks this project's tenth anniversary of raising awareness of the importance of application security risks The OWASP Top 10 |
|
OWASP TOP 10 LES DIX VULNÉRABILITÉS DE SÉCURITÉ
OWASP Top 10 2007 RESUMÉ A1 - Cross Site Scripting (XSS) Les failles XSS se produisent à chaque fois qu'une application prend des données écrites par |
|
OWASP Top 10 - OWASP Foundation
These APIs are often unprotected and contain numerous vulnerabilities A10 – Underprotected APIs OWASP Top 10 Application Security Risks – 2017 |
|
HOW TO PROTECT AGAINST THE OWASP TOP 10 - F5 Networks
CAN EDUCATION REDUCE VULNERABILITIES? THE OWASP TOP 10: A TAXONOMY OF RISK The Open Web Application Security Project publishes the |
|
Protect Your Applications Against All OWASP Top 10 - Imperva, Inc
It provides excellent insight into the most critical security risks to web applications In spite of the fact that more than half of the threats on the OWASP 2017 Top 10 |
|
Simplifying Application Security and Compliance with the OWASP
The objective of the OWASP Top 10 project is not only to raise awareness about ten specific risks, but also to educate business managers and technical personnel |
|
OWASP Top 10 PPT - Cypress Data Defense
What are the OWASP Top 10 Vulnerabilities for 2017? A1: Injection A2: Broken Authentication A3: Sensitive Data Exposure A4: XML External Entities (XEE) |


![OWASP Mobile Security by Sven Schleier et al [PDF/iPad/Kindle] OWASP Mobile Security by Sven Schleier et al [PDF/iPad/Kindle]](http://hackersgrid.com/wp-content/uploads/2017/11/owasp.jpg)


![OWASP Testing Manual v40 - [PDF Document] OWASP Testing Manual v40 - [PDF Document]](https://i2.wp.com/habrastorage.org/webt/dv/ks/qi/dvksqiidkrekftgx_6zrdqudbno.png?w\u003d1160\u0026ssl\u003d1)