password policy example
|
Password Policy Sample
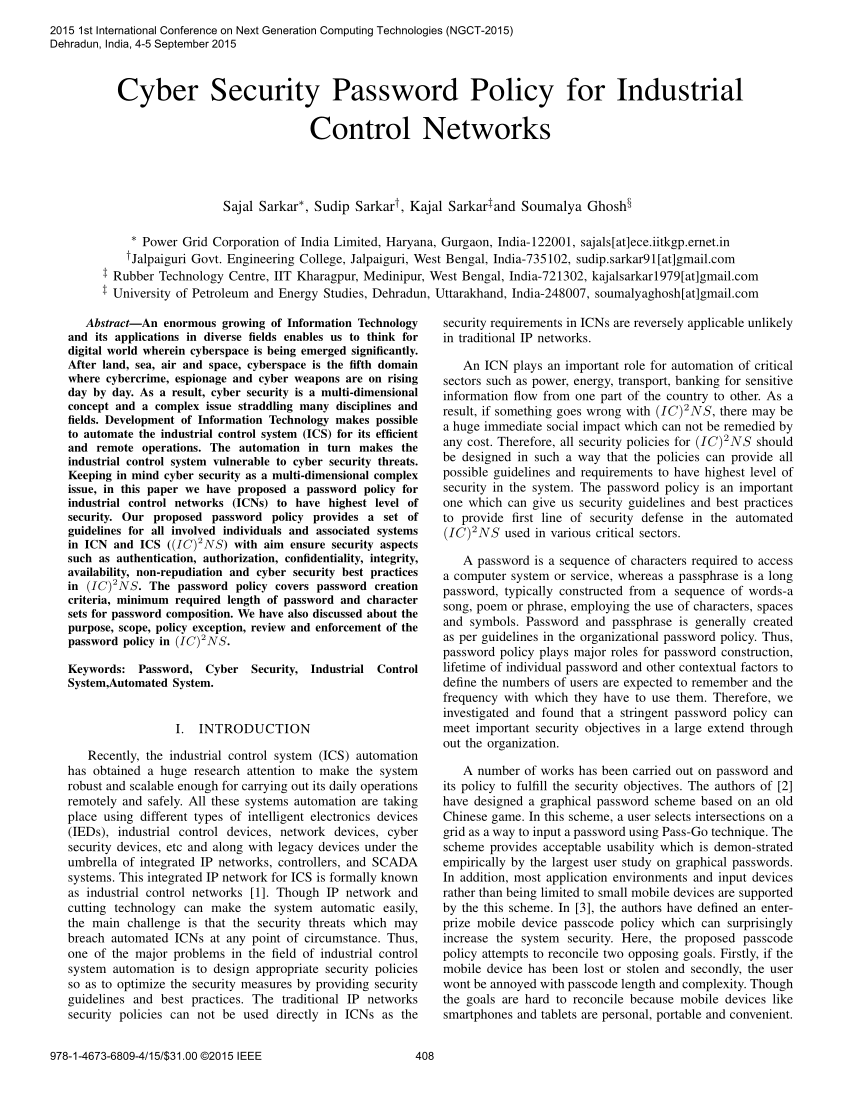
Password Policy Sample. (Sample written policy to assist with compliance). 1.0 Overview. Passwords are an important aspect of computer security. |
|
Password-policy.pdf
Derbyshire County Council Password Policy. 1. Information Security Document IMPORTANT: The above passphrase/password is an example and must NOT be. |
|
Password Policy Template
Password Policy Template. Overview. Employees at “CARA Technology” are given access a variety of IT resources including computers and. |
|
IT PASSWORD POLICY
Jan 25 2022 Examples of user accounts with privileges include: administrative and super user accounts. 5.10 “Security Tokens” are logical codes or physical ... |
|
AUC Password Policy
PASSWORD POLICY. Policy Statement The purpose of this policy is to establish a standard for creation of strong passwords the pro. |
|
USNH PASSWORD POLICY PURPOSE POLICY STATEMENT 2.1
Apr 30 2020 POLICY STATEMENT. 2.1 Password Change Frequency. 2.1.1 All passwords associated with USNH accounts must be changed annually with the ... |
|
Password Policy - UWE Bristol
This policy helps all members of UWE infosec@uwe.ac.uk. Password. Policy. September 2021 ... symbols can still be used if needed for example '3red! |
|
Password Policy for IT Systems - Information Services
Passwords are an important aspect of computer security and the failure to use Policy. When creating strong passwords users need to ensure that they:. |
|
Student Password Policy
Nov 20 2020 b) The password complexity standard for University student network ... A typical example of second factor authentication could be a passcode. |
|
CAPITAL UNIVERSITY PASSWORD POLICY
Try to create passwords that can be easily remembered. One way to do this is create a password based on a song title affirmation |
|
Password Policies and Guidelines - Cornell University
Apr 28 2021 · password manager such as LastPass as long as the master password is kept private and meets the requirements in the 3 Password Requirements section of this policy e) Individuals must never leave themselves logged into an application or system where someone else can unknowingly use their account i |
|
Example: Password Policy Example - IBM
Identification and Authentication Policy Information Security Policy Security Assessment and Authorization Policy Security Awareness and Training Policy ID AM-2 Software platforms and applications within the organization are inventoried Acceptable Use of Information Technology Resource Policy Access Control Policy |
|
Password Protection Policy
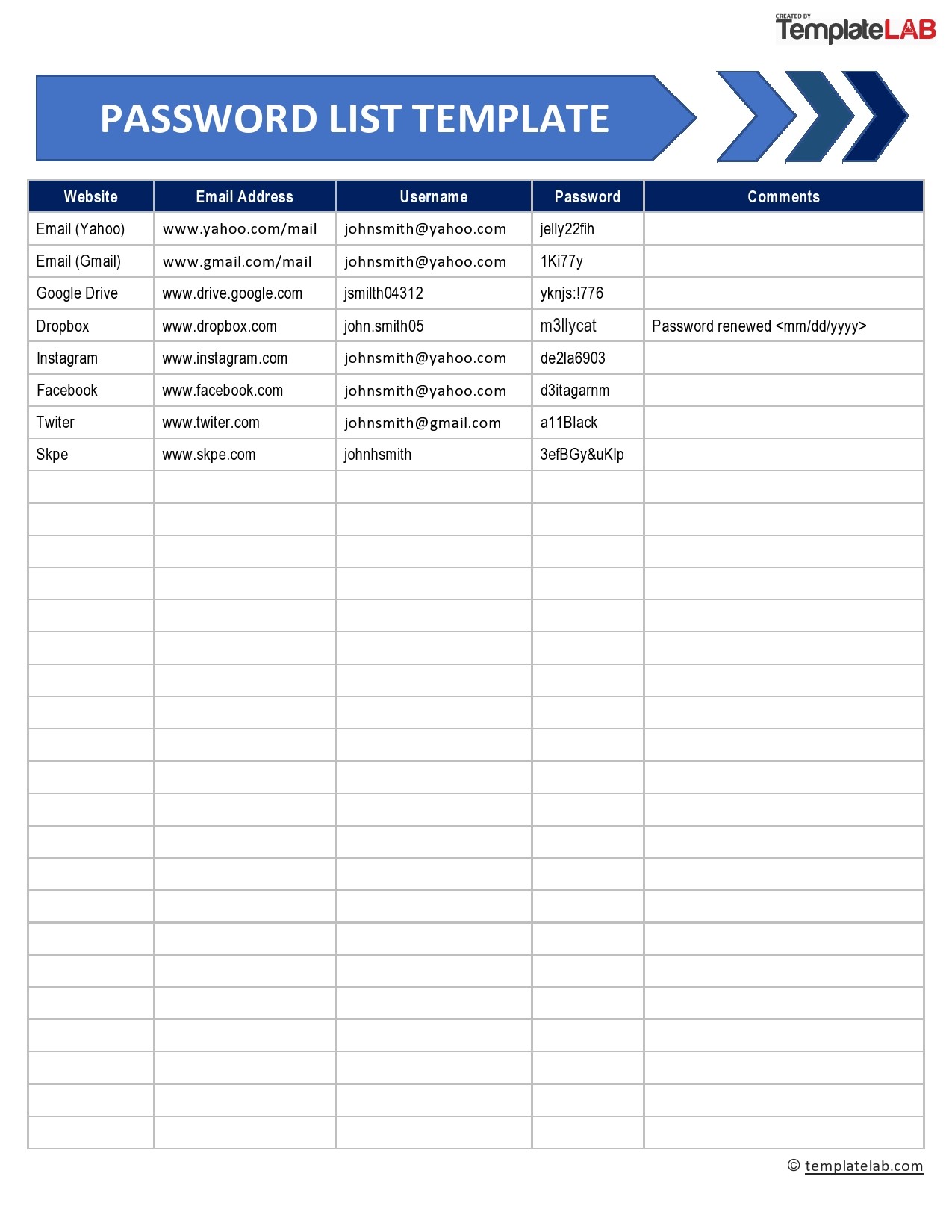
4 1 Password Creation 4 1 1 All user-level and system-level passwords must conform to the Password Construction Guidelines 4 1 2 Users must use a separate unique password for each of their work related accounts Users may not use any work related passwords for their own personal accounts |
|
Password Policy - Derbyshire
V13 0 Derbyshire County Council Password Policy 6 • Passwords should never be written down or stored online Try to create passwords that can be easily remembered Poor weak passwords have the |
|
Searches related to password policy example filetype:pdf
Password Policy 1 0 Overview Passwords are an important aspect of computer security They are the front line of protection for user accounts A poorly chosen password may result in the compromise of the University of Evansville's entire corporate network As su ch all University of Evansville employees |
What is the purpose of a password policy?
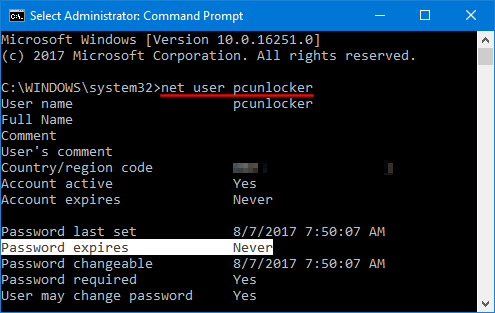
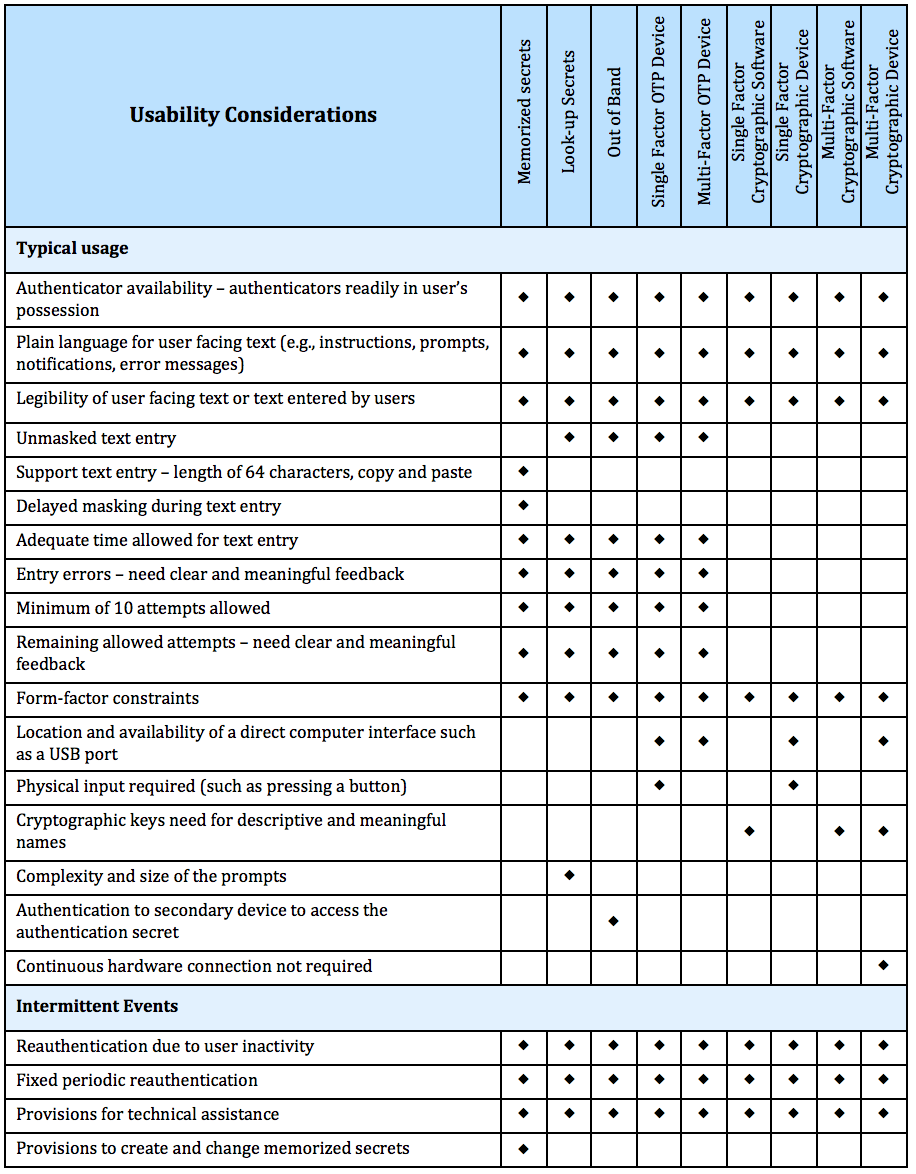
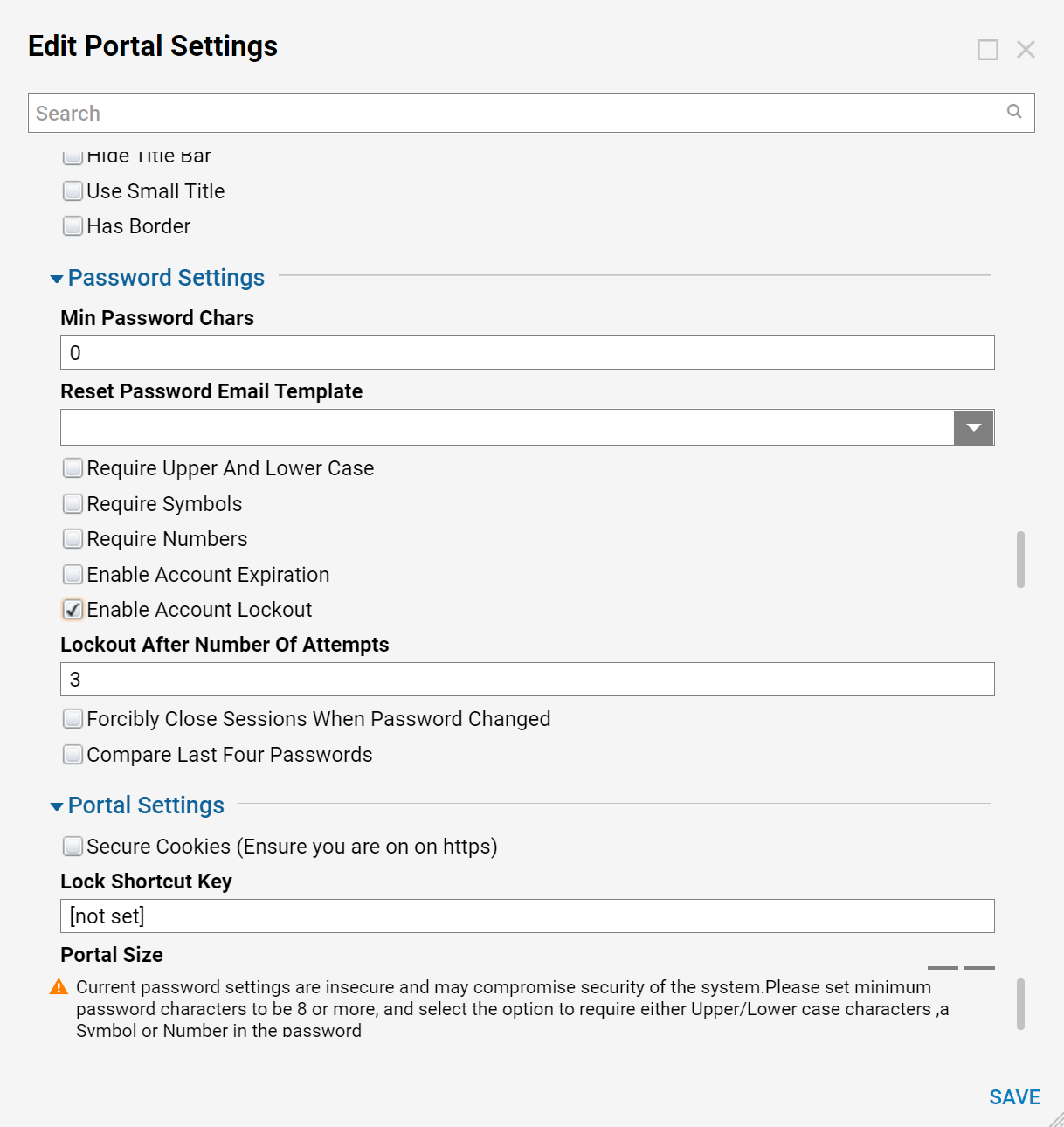
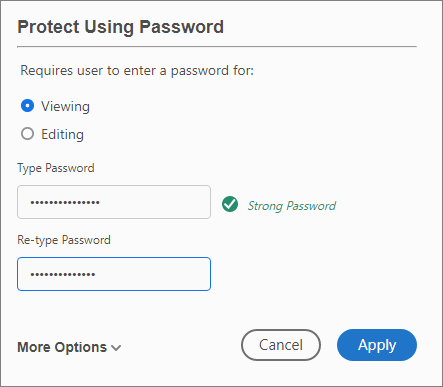
- Once all conditions set in the password policy are met by the user changing the password, the system saves the new password and allows the user access. Each user account can have only one password policy associated with it, but you can apply one password policy to multiple user accounts.
What are the requirements for a strong password?
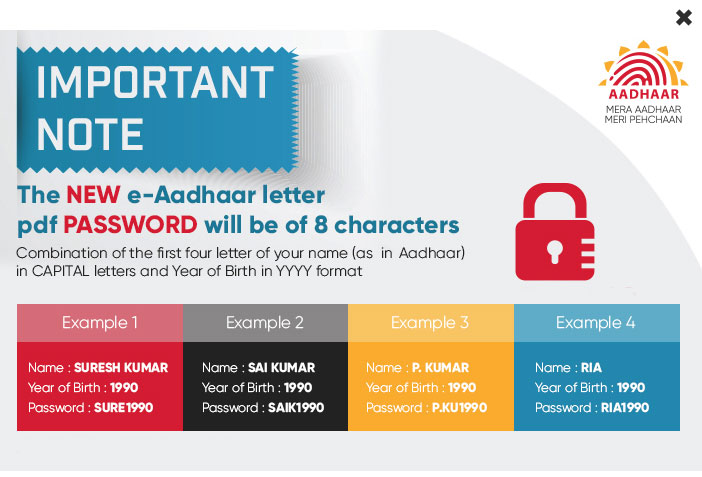
- A secure network environment requires all users to use strong passwords, which have at least eight characters and include a combination of letters, numbers, and symbols. These passwords help prevent the compromise of user accounts and administrative accounts by unauthorized users who use manual methods or automated tools to guess weak passwords.
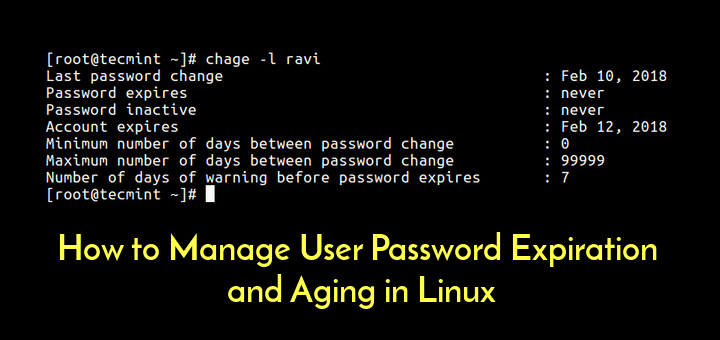
How often do passwords need to be changed?
- Change passwords often. IT recommends customers change their passwords at least once a month to discourage hackers. Remember, an expert hacker may eventually discover your password given enough time to work on it.
|
Sample Password Policy
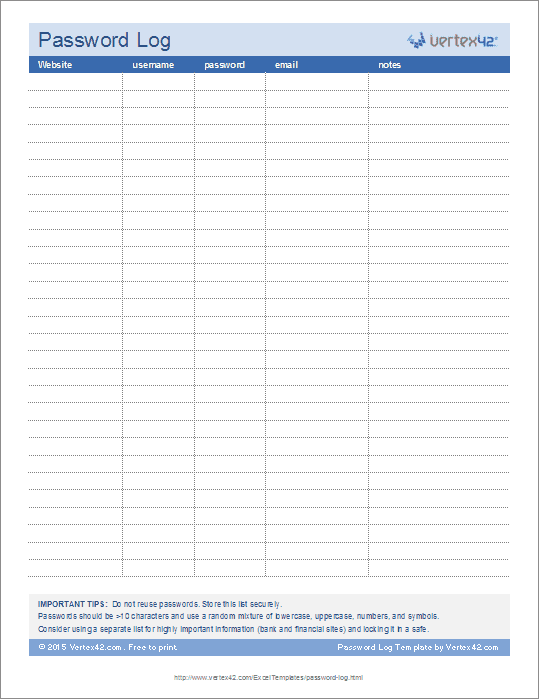
Do not use your User ID as your password Do not share [agency name] passwords with anyone, including administrative assistants or secretaries All passwords are to be treated as sensitive, Confidential [agency name] information |
|
Password Policy - SANS Technology Institute
(NOTE: Do not use either of these examples as passwords) B Password Protection Standards • Always use different passwords for accounts |
|
Password Policy - Technology and Security Consulting Services
NOTE: Do not use either of these examples as passwords B Password Protection Standards Do not use the same password for accounts as |
|
Password Policy - IAgrE
As far as possible, passwords should be easy to remember For this purpose, pass-phrase based passwords may be used For example, the phrase might be: " My |
|
Password policy - Derbyshire County Council
store any personal, sensitive or confidential Council information 4 Policy Statement The continual reliance on IT systems, requires that effective password controls |
|
CAPITAL UNIVERSITY PASSWORD POLICY
NOTE: Do not use either of these examples as passwords Poor, weak passwords have the following characteristics: • The password contains less than seven |
|
IT Password Protection Policy - Southern Health NHS Foundation
3 sept 2019 · A self-service password reset tool is currently available to staff who have a requirement – for example, their working hours are outside helpdesk |










![Screenshots of A-PDF Password Security [A-PDFcom] Screenshots of A-PDF Password Security [A-PDFcom]](https://templatelab.com/wp-content/uploads/2020/04/Password-List-Template-01-TemplateLab.com_.jpg)