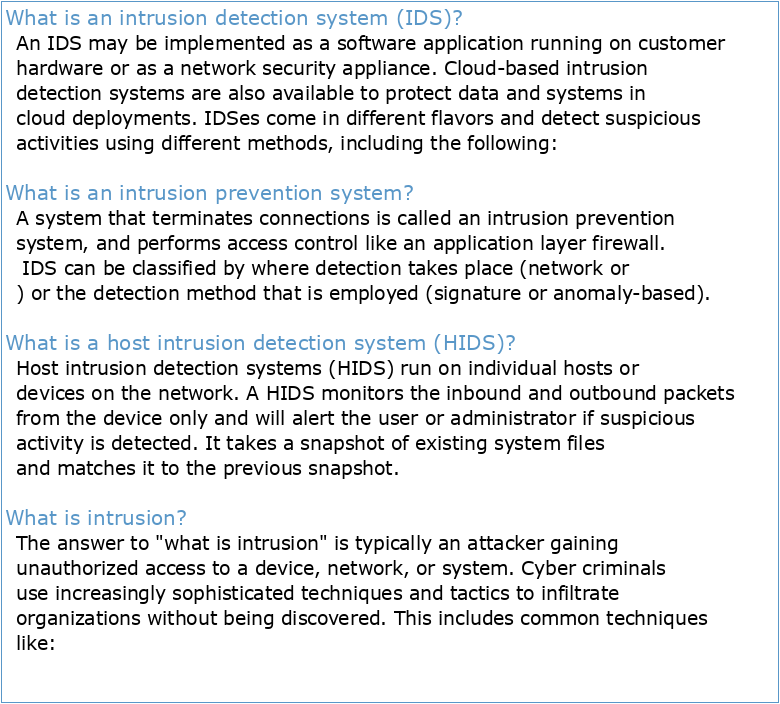
What is an intrusion detection system (IDS)?
An IDS may be implemented as a software application running on customer hardware or as a network security appliance. Cloud-based intrusion detection systems are also available to protect data and systems in cloud deployments. IDSes come in different flavors and detect suspicious activities using different methods, including the following:
What is an intrusion prevention system?
A system that terminates connections is called an intrusion prevention system, and performs access control like an application layer firewall. IDS can be classified by where detection takes place (network or ) or the detection method that is employed (signature or anomaly-based).
What is a host intrusion detection system (HIDS)?
Host intrusion detection systems (HIDS) run on individual hosts or devices on the network. A HIDS monitors the inbound and outbound packets from the device only and will alert the user or administrator if suspicious activity is detected. It takes a snapshot of existing system files and matches it to the previous snapshot.
What is intrusion?
The answer to "what is intrusion" is typically an attacker gaining unauthorized access to a device, network, or system. Cyber criminals use increasingly sophisticated techniques and tactics to infiltrate organizations without being discovered. This includes common techniques like:
Chapitre4 : Arithmétique dans Z
INITIATION À LA BUREAUTIQUE
CATABOLISME DES AA-AROMATIQUES 2016
LE SYSTÈME DE DÉTECTION DES INTRUSIONS ET LE SYSTÈME D
IDS IPS last
Chap2 notion d'algorithme et de programme
Chapitre 2-Notions d'Algorithme et programme Pascal
DIU Sexologie médecine sexuelle et sexothérapie
Formation en Psycho – Sexologie Appliquée (FPSA)

IDS / IPS expliqués en dessins

Détection dintrusions avec SNORT / IDS / IPS / prévention dintrusions
