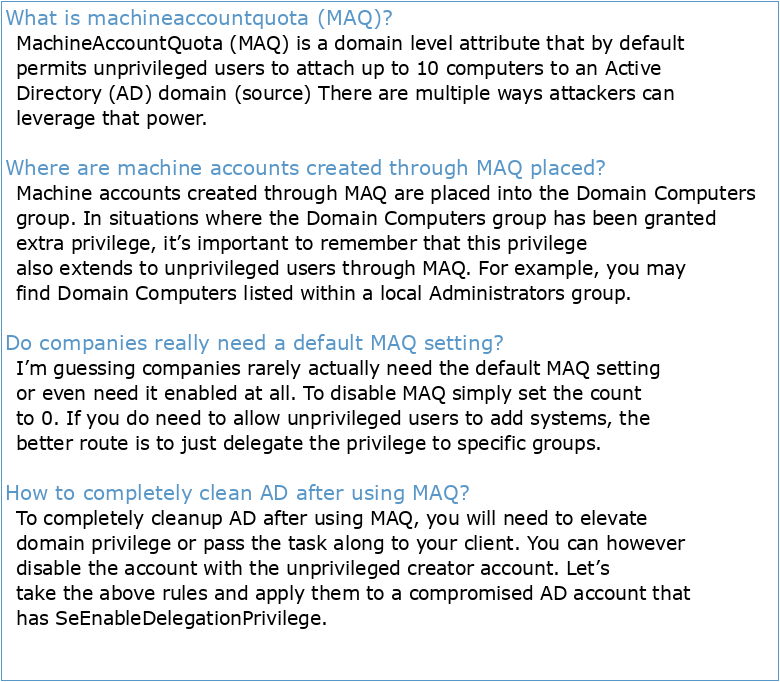
What is machineaccountquota (MAQ)?
MachineAccountQuota (MAQ) is a domain level attribute that by default permits unprivileged users to attach up to 10 computers to an Active Directory (AD) domain (source) There are multiple ways attackers can leverage that power.
Where are machine accounts created through MAQ placed?
Machine accounts created through MAQ are placed into the Domain Computers group. In situations where the Domain Computers group has been granted extra privilege, it’s important to remember that this privilege also extends to unprivileged users through MAQ. For example, you may find Domain Computers listed within a local Administrators group.
Do companies really need a default MAQ setting?
I’m guessing companies rarely actually need the default MAQ setting or even need it enabled at all. To disable MAQ simply set the count to 0. If you do need to allow unprivileged users to add systems, the better route is to just delegate the privilege to specific groups.
How to completely clean AD after using MAQ?
To completely cleanup AD after using MAQ, you will need to elevate domain privilege or pass the task along to your client. You can however disable the account with the unprivileged creator account. Let’s take the above rules and apply them to a compromised AD account that has SeEnableDelegationPrivilege.
Powermad
In late 2017, I released Powermad, which is a collection of PowerShell functions derived from an LDAP domain joinpacket capture. After digging through the packets, I identified the single encrypted LDAP add that created the machine account object. Here is an example of the LDAP add in an unencrypted state: My main motivation while developing Powerm
So Is Machineaccountquota Useful?
Since I first started working on Powermad, I’ve learned a lot about MAQ beyond just the default 10 system limit. Recently, I’ve learned even more from some amazing blog posts by Elad Shamir, Harmj0y, and Dirk-jan, in which MAQ makes an appearance. Overall, the conclusion I’ve reached is that MachineAccountQuota is useful… …sometimes. In this blog p
What Are The Rules?
I’ve broken up what I know about MAQ into 10 rules. Hopefully, you can use these rules to determine if MAQ can be useful in any particular situation. 1. MAQ allows unprivileged users to add machine account objects to a domain. By default, an unprivileged user can create 10 machine accounts. You do not need to do anything special to invoke MAQ. You
Machineaccountquota in Action
Let’s take the above rules and apply them to a compromised AD account that has SeEnableDelegationPrivilege. As mentioned in rule 4, even though an account has write access to an attribute, the write attempt is still subject to validation. However, if you happen to compromise an account with the correct privilege, such as SeEnableDelegationPrivilege
Defending Against Machineaccountquota
I believe that MAQ is just one of those default settings without enough awareness. I’m guessing companies rarely actually need the default MAQ setting or even need it enabled at all. To disable MAQ simply set the count to 0. If you do need to allow unprivileged users to add systems, the better route is to just delegate the privilege to specific gro
Conclusion
As with most things, MachineAccountQuota usage is situational. For testers, it is however something that is worthy of consideration for your bag of tricks. This has become even more apparent with recently released techniques from researchers such as Elad Shamir. For defenders, I recommend just disabling MachineAccountQuota. Special thanks to Karl F
1 Introduction sur la négociation en entreprise
L'internationalisation des PMe québécoises
Promotion et développement des entreprises québécoises sur les
NÉGOCIER DANS UNE ENTREPRISE
Négocier dans une entreprise de 11 à 49 salariés dépourvue de
LA NÉGOCIATION COLLECTIVE
Chapitre 1 : Normalisation et repérage d'une installation électrique
Prescription de renvoi pour des séances de psychologie de
Impulser la construction de plans de syndicalisation dans les syndicats