What is a BYOD security policy?
BYOD stands for bring your own device, and the most commonly accepted BYOD meaning is when employees use their own personal devices to connect to the organization's network and access what they need to do their jobs.
This includes data and information that could be potentially sensitive or confidential.How do I secure my BYOD device?
Reviewing the fundamentals
1Communicate written BYOD security policies.
2) Continuously provide security awareness training.
3) Reinforce account and device safety.
4) Incorporate Zero Trust.
5) Stamp out shadow IT.
6) Implement strong data security controls.
7) Prevent malware threats.
8) Get visibility into and context of devices.Employees of [Company Name] may have the opportunity to use their personal electronic devices for work purposes when authorized in writing, in advance, by the employee and management.
Personal electronic devices include personally owned cellphones, smartphones, tablets, laptops and computers.
How do I write a BYOD policy?
Write your policy down before implementing it.
1Establish the Scope.2) Protect Privacy: Separate Personal and Company Data.
3) Compliance and Security Initiatives.
4) Simplify the Sign-Up Process.
5) Establish Reimbursement Guidelines.
6) Plan for Ongoing Maintenance.
7) Write Your Policy Down Before Implementing.
8) Sharing Your BYOD Policy.
|
Guidelines on the protection of personal data in mobile devices
17 déc. 2015 Information security policy . ... Organisational measures for BYOD . ... security policies and technical |
|
SAMPLE BYOD MOBILE DEVICE SECURITY POLICY
This outline of a BYOD policy gives a framework for securing mobile devices and should be linked to other policies which support your organization's posture on |
|
ITP-SEC035 Mobile Device Security Policy
13 mars 2014 Agencies must leverage. OA/OIT service offering. Personal devices / bring your own device (BYOD). Not Applicable. Users with personal devices ... |
|
Modifying Security Policies Towards BYOD
The data ownership problem arises when the data is been stored in the mobile device. What devices can BYOD policies support? The employees may prefer bringing |
|
Burdekin
23 nov. 2021 personally owned mobile devices (BYOD) used for work purposes. • eligible council employees contractors |
|
Mobile Device Security: Bring Your Own Device (BYOD)
18 mars 2021 mobile devices enforces security policies |
|
Capturing Policies for BYOD
27 nov. 2017 agreements companies may also use Mobile Device Management (MDM) software which can help enforce policies. MDM software can configure a ... |
|
Mobile Device Policy
2 déc. 2020 BYOD: Bring Your Own Device permits State personnel (both employees & contractors) to use personally owned mobile devices in the workplace ... |
|
Mobile devices risk management and data protection
8 mai 2015 Data for the management of the mobile devices themselves (“Mobile Device Management” solutions) ... Have a policy governing BYOD:. |
|
Sample Mobile Device Security Policy - Sophos
Corporate IT departments face two challenges when contemplating a BYOD policy: a mix of corporate and employee owned devices accessing the organization's |
|
Bring Your Own Device (BYOD) Security Policy - Q-CERT
Devices work within the company IT environment, but the employees own their phone — either they paid for it themselves and can keep it forever, or the company |
|
Mobile Device Policy with BYOD - INgov
Policy and Procedures for Use of Personally- Owned Mobile managed BYOD Program Appendix C: Security Criteria for Personally Owned Mobile Devices |
|
Modifying Security Policies Towards BYOD - ScienceDirectcom
The prevailing security policies in BYOD are no more supportive for mobile devices like smartphones, tablets and laptops The security policies must be modified |
|
IDENTIFYING BEST PRACTICES FOR A BYOD POLICY - CORE
byod risks and disadvantages, byod risk mitigation strategies, security, mobile security, An organization with a BYOD policy allows the employees to take |
|
Legal Issues in Secure Implementation of Bring Your Own Device
the economical and usage benefits, Bring Your Own Device policy can pose some security models are used for BYOD – Mobile Device Management (MDM ), |
|
[PDF] Sample Mobile Device Security Policy - Sophos
Corporate IT departments face two challenges when contemplating a BYOD policy a mix of corporate and employee owned devices accessing the organization's |
|
[PDF] Bring Your Own Device (BYOD) Security Policy - Q-CERT
The head of agency shall by accountable for BYOD security policy and shall ensure completion Proposed Windows Mobile Security Policy The above is a list |
|
[PDF] Bring your own device - EY
The risk landscape of a BYOD mobile device deployment is largely dependent on these security policy controls, often through a unified management interface |
|
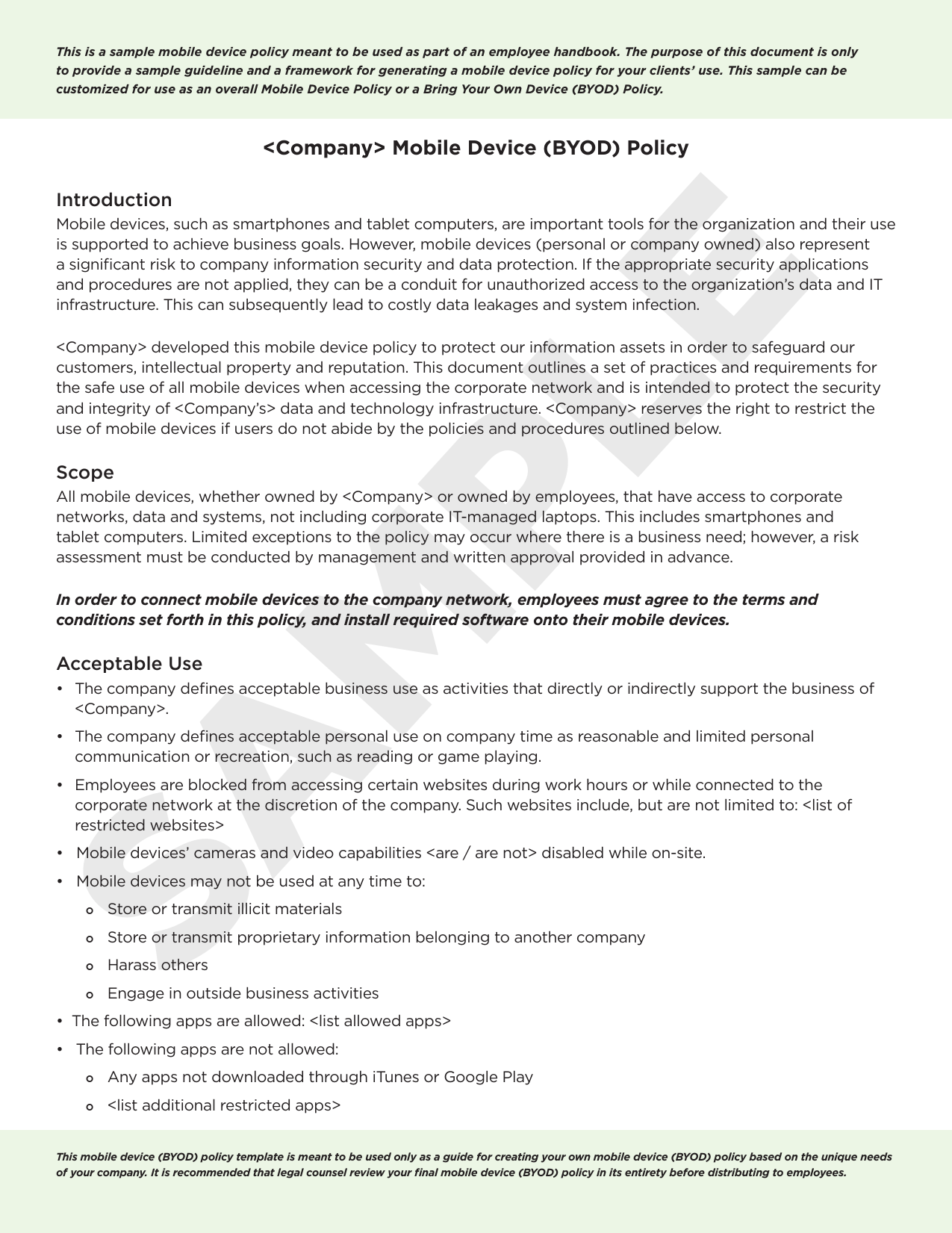
[PDF] Mobile Device (BYOD) Policy
This is a sample mobile device policy meant to be used as part of an employee handbook The purpose of this document is only to provide a sample guideline |
|
[PDF] I Purpose POLICY 08:13:06 BRING YOUR OWN DEVICE (BYOD
BRING YOUR OWN DEVICE (BYOD) The purpose of this policy is to define the appropriate use and procedures for using personally owned mobile and other |
|
[PDF] Bring Your Own Device Policy - University of Strathclyde
All relevant University policies still apply to staff using BYOD Staff should Protection of Information Held on Mobile Devices and Encryption Policy • Anti Virus |
|
[PDF] BYOD Policy - Squarespace
a variety of mobile devices and to protect your organization's sensitive data You need to ly, a BYOD security policy and its enforcement mechanisms |
|
[PDF] securing byod - CDW
29 CHAPTER 5 Strategies for BYOD Success • Mobile Use Policies • Device App Choice Guidelines • Incident Response Strategy • BYOD Security Solution |
- mobile device policy
- byod security policy
- byod policy
- byod policy template
- mobile device management policy best practices
- mobile device policy iso 27001
- sans byod policy template
- mobile device management policy pdf
PDF) MOBILE DEVICE MANAGEMENT IN THE CONTEXT OF BYOD
Source:https://s3.manualzz.com/store/data/027007936_1-35b77c33658794b98c9eaf0e4684fe6b.png
Mobile Device (BYOD) Policy
Source: Manualzz
Mobile Device Acceptable Use Policy TEMPLATE
Source: Computer Security

Development of Bring-Your-Own-Device Risk Management Model: A Case
Source:https://i1.rgstatic.net/publication/343248669_BYOD_SECURITY_STRATEGY_ASPECTS_OF_A_MANAGERIAL_DECISION/links/5f522c4792851c250b8f446c/largepreview.png

PDF) BYOD SECURITY STRATEGY (ASPECTS OF A MANAGERIAL DECISION)
Source:https://www.wordlayouts.com/wp-content/uploads/2016/06/BYOD-Policy-Example-pdf-1.png

BYOD Policy Templates - 4 Best Samples and Examples
Source:https://i1.rgstatic.net/publication/327784045_Bring_your_own_device_a_survey_of_threats_and_security_management_models/links/5cfa2a154585157d15991678/largepreview.png
byod policy best practices
[PDF] BYOD Best Practices, Requirements and Challenges - Advanced
- byod security policy considerations and best practices
byod policy examples
[PDF] Bring your own device - EY
- google byod policy
- byod policy for small business
- gdpr byod policy template
- byod policy template sans
- byod policy best practices
- byod examples
- byod policy framework
- simple byod policy
- byod company policy examples
- byod corporate policy examples
byod policy nist
[PDF] A Call to Action Bring Your Own Device (BYOD) Personally - ATARC
- nist byod policy template
- nist telework policy
- nist 800-114
- byod standards
- nist mobile device security
- nist remote access
- nist guide to remote working
- nist 800-171 byod
- byod policy template nist
byod policy pdf
[PDF] Bring Your Own Device (BYOD) and Acceptable - The Horton Group
- byod policy template
- simple byod policy
- gdpr byod policy template
- byod security policy
- byod acceptable use policy
- byod pdf
- byod standards pdf
- bring your own device policy gdpr
- byod policy sample pdf
- byod policy example pdf
- byod security policy pdf