 The Mobile Application Hackers Handbook
The Mobile Application Hackers Handbook
Although we provide some background theory for you to understand the fundamentals of mobile application pdf. Some browsers such as Chrome
 The mobile application hackers handbook
The mobile application hackers handbook
Mobile Application (In)security. 1. The Evolution of Mobile Applications. 2. Common Mobile Application Functions. 3. Benefits of Mobile Applications. 4. Mobile
 The Mobile Application Hackers Handbook
The Mobile Application Hackers Handbook
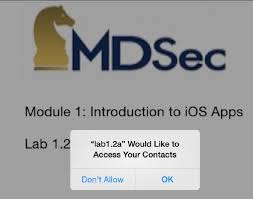
For each of the mobile platforms; we provide a pragmatic approach to performing a mobile application security assessment. pdf"];. NSError *error = nil;. [ ...
 The Mobile Application Hackers Handbook
The Mobile Application Hackers Handbook
The Mobile Application Hacker's Handbook. Published by. John Wiley & Sons Inc. 10475 download this material at http:// booksupport.wiley.com. For more ...
 The Web Application Hackers Handbook: Finding and Exploiting
The Web Application Hackers Handbook: Finding and Exploiting
%20Marcus%20Pinto%20-%20The%20web%20application%20hacker's%20handbook_%20finding%20and%20exploiting%20security%20flaws-Wiley%20(2011).pdf
 The Web Application Hackers Handbook: Discovering and
The Web Application Hackers Handbook: Discovering and
of /apps then the browser will submit its cookies to the paths /apps-test ... pdf. Because this is a completely static resource
 Программа учебной дисциплины «Безопасность компьютерных
Программа учебной дисциплины «Безопасность компьютерных
14 февр. 2019 г. The mobile application Hacker's handbook. John Wiley & Sons. 2015. – URL: http://proxylibrary.hse.ru:2048/login?url=http://search.ebscohost ...
 iOS Hackers Handbook
iOS Hackers Handbook
Of course once you could download new apps to iOS devices
 The Web Application Hackers Handbook: Discovering and
The Web Application Hackers Handbook: Discovering and
of /apps then the browser will submit its cookies to the paths /apps-test ... pdf. Because this is a completely static resource
 COMP4332 Mobile Security: Principles and Practice
COMP4332 Mobile Security: Principles and Practice
1 июн. 2021 г. static analysis of mobile malware dynamic analysis of mobile malware. 4. 7 ... Mobile Application Hacker's Handbook
 The Mobile Application Hackers Handbook
The Mobile Application Hackers Handbook
mobile applications are not covered in the context of this book; however we highly recommend The Web Application Hacker's. Handbook
 The Mobile Application Hackers Handbook
The Mobile Application Hackers Handbook
Using iTunes you can download applications from the App Store and synchronize Figure 2.4 summarizes this process courtesy of the iOS Hackers Handbook.
 Android Hackers Handbook PDF
Android Hackers Handbook PDF
ranging from app security to platform security (especially Android)
 The Web Application Hackers Handbook: Discovering and
The Web Application Hackers Handbook: Discovering and
21 févr. 2007 The web application hacker's handbook : discovering and exploiting security flaws / Dafydd Stut- tard Marcus Pinto. p. cm. Includes index.
 The mobile application hackers handbook
The mobile application hackers handbook
Common Mobile Application Functions. 3. Benefits of Mobile Applications. 4. Mobile Application Security. 4. Key Problem Factors.
 The Web Application Hackers Handbook: Finding and Exploiting
The Web Application Hackers Handbook: Finding and Exploiting
%20Marcus%20Pinto%20-%20The%20web%20application%20hacker's%20handbook_%20finding%20and%20exploiting%20security%20flaws-Wiley%20(2011).pdf
 The Web Application Hackers Handbook
The Web Application Hackers Handbook
21 févr. 2007 Dafydd Stuttard. Marcus Pinto. The Web Application. Hacker's Handbook. Discovering and Exploiting Security Flaws. Wiley Publishing Inc.
 The Antivirus Hackers Handbook
The Antivirus Hackers Handbook
If this book refers to media such as a CD or DVD that is not included in the version you purchased you may download this material at http://booksupport.wiley.
 The Web Application Hackers Handbook
The Web Application Hackers Handbook
6 juil. 2011 The Web Application Hacker's Handbook: Finding and Exploiting ... with mobile applications that are accessed using a smartphone or tablet.
 The Mac Hackers Handbook
The Mac Hackers Handbook
Charlie Miller. Dino A. Dai Zovi. The Mac® Hacker's. Handbook nm /Applications/Safari.app/Contents/MacOS/Safari
 Searches related to the mobile application hacker+s handbook pdf PDF
Searches related to the mobile application hacker+s handbook pdf PDF
anApplication 204UnderstandingtheSecurityModel 206CodeSigning 206DiscoveredVulnerabilities 210UnderstandingPermissions 212InspectingtheAndroidPermissionModel 212ProtectionLevels 216ApplicationSandbox 219FilesystemEncryption 221GenericExploitMitigationProtections 222RootingExplained 226RootingObjectives 226RootingMethods
What is the mobile application hacker's Handbook?
The Mobile Application Hacker's Handbook is a comprehensive guide to securing all mobile applications by approaching the issue from a hacker's point of view. Heavily practical, this book provides expert guidance toward discovering and exploiting flaws in mobile applications on the iOS, Android, Blackberry, and Windows Phone platforms.
Who is the author of hacker handbooks?
Sommers is the lead author on Hacker handbooks, all published by Bedford/St. Martin’s, and is coauthor of Fields of Reading, Tenth Edition (2013). If playback doesn't begin shortly, try restarting your device.
Where can I find information about mobile application hackers?
The companion website for this book at www.mobileapphacker.com, which you can also link to from www.wiley.com/go/mobileapplicationhackers, contains several resources that you will find useful in the course of mastering the tech-niques we describe and using them to attack actual applications.
When should I read the mobile application ECU-Rity book?
If you are new to mobile application secu-rity, it is recommended that you read the book from start to finish, acquiring the knowledge and understanding to tackle later chapters. This can be applied to the relevant chapters for each mobile platform, or the entirety of the book.
DominicChell
Tyrone
Erasmus
ShaunColley
jOllieWhitehouse
WitfyTV.mk::.Mm - i*JLm4ml
Coilt»»fits
Introductionxxxi
Chapter
1Mobile
Application(In)security
1TheEvolutionofMobile
Applications
2CommonMobile
Application
Functions3
BenefitsofMobile
Applications
4Mobile
ApplicationSecurity
4 KeyProblemFactors7
UnderdevelopedSecurity
Awareness7
Ever-Changing
AttackSurfaces7
EconomicandTimeConstraints7
Custom
Development
8TheOWASPMobile
SecurityProject
8OWASPMobile
Top Ten9OWASPMobile
Security
Tools12
TheFutureofMobile
ApplicationSecurity
13Summary
15Chapter
2Analyzing
iOSApplications
17Understanding
theSecurity
Model17
Initializing
iOSwithSecureBootChain18Introducing
theSecureEnclave19RestrictingApplication
Processes
with CodeSigning
19IsolatingApplications
withProcess-LevelSandboxing
20Protecting
InformationwithData-at-Rest
Encryption
20ProtectingAgainst
Attackswith
ExploitMitigation
Features21
Understanding
iOSApplications
22DistributionofiOS
Applications
23AppleApp
Store23
Enterprise
Distribution24
xvi xviiiContentsApplication
Structure
24InstallingApplications
25UnderstandingApplication
Permissions
26JailbreakingExplained
29Reasonsfor
Jailbreaking
29Types ofJailbreaks 30
Building
aTestEnvironment 33Accessing
theDevice 33Building
aBasicToolkit 34Cydia 34
BigBoss
RecommendedTools34
Apple's
CCTools
35Debuggers
38Toolsfor
Signing
Binaries
39Installipa
40Exploring
theFilesystem
40Property
Lists 42Binary
Cookies
42SQLiteDatabases
42Understanding
theDataProtectionAPI43Understanding
theiOSKeychain
46Accessing
theiOSKeychain
49Understanding
TouchID51
Reverse
Engineering
iOSBinaries53Analyzing
iOSBinaries 53IdentifyingSecurity-Related
Features56
Position-Independent
Executable56
Stack-Smashing
Protection
57AutomaticReference
Counting
58DecryptingApp
StoreBinaries59
Decrypting
iOSBinaries Using aDebugger
59Automating
theDecryption
Process61
InspectingDecrypted
Binaries62
InspectingObjective-CApplications
62Inspecting
SwiftApplications
63Disassembling
andDecompiling
iOSApplications
67Summary
67quotesdbs_dbs14.pdfusesText_20
[PDF] the national k 12 foreign language enrollment survey report 2018
[PDF] the national k 16 foreign language enrollment survey report
[PDF] the nature of code pdf download
[PDF] the netflix recommender system
[PDF] the neuroscience of joyful education
[PDF] the new c standard
[PDF] the new oxford picture dictionary (english spanish edition)
[PDF] the new oxford picture dictionary download
[PDF] the new oxford picture dictionary english chinese pdf
[PDF] the new oxford picture dictionary english spanish pdf free
[PDF] the new oxford picture dictionary monolingual english edition
[PDF] the new oxford picture dictionary spanish pdf
[PDF] the new school waitlist
[PDF] the new york times guide to the best 1
