 The Mobile Application Hackers Handbook
The Mobile Application Hackers Handbook
Although we provide some background theory for you to understand the fundamentals of mobile application pdf. Some browsers such as Chrome
 The mobile application hackers handbook
The mobile application hackers handbook
Mobile Application (In)security. 1. The Evolution of Mobile Applications. 2. Common Mobile Application Functions. 3. Benefits of Mobile Applications. 4. Mobile
 The Mobile Application Hackers Handbook
The Mobile Application Hackers Handbook
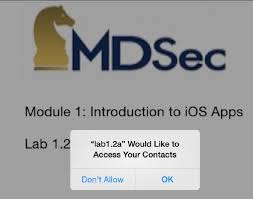
For each of the mobile platforms; we provide a pragmatic approach to performing a mobile application security assessment. pdf"];. NSError *error = nil;. [ ...
 The Mobile Application Hackers Handbook
The Mobile Application Hackers Handbook
The Mobile Application Hacker's Handbook. Published by. John Wiley & Sons Inc. 10475 download this material at http:// booksupport.wiley.com. For more ...
 The Web Application Hackers Handbook: Finding and Exploiting
The Web Application Hackers Handbook: Finding and Exploiting
%20Marcus%20Pinto%20-%20The%20web%20application%20hacker's%20handbook_%20finding%20and%20exploiting%20security%20flaws-Wiley%20(2011).pdf
 The Web Application Hackers Handbook: Discovering and
The Web Application Hackers Handbook: Discovering and
of /apps then the browser will submit its cookies to the paths /apps-test ... pdf. Because this is a completely static resource
 Программа учебной дисциплины «Безопасность компьютерных
Программа учебной дисциплины «Безопасность компьютерных
14 февр. 2019 г. The mobile application Hacker's handbook. John Wiley & Sons. 2015. – URL: http://proxylibrary.hse.ru:2048/login?url=http://search.ebscohost ...
 iOS Hackers Handbook
iOS Hackers Handbook
Of course once you could download new apps to iOS devices
 The Web Application Hackers Handbook: Discovering and
The Web Application Hackers Handbook: Discovering and
of /apps then the browser will submit its cookies to the paths /apps-test ... pdf. Because this is a completely static resource
 COMP4332 Mobile Security: Principles and Practice
COMP4332 Mobile Security: Principles and Practice
1 июн. 2021 г. static analysis of mobile malware dynamic analysis of mobile malware. 4. 7 ... Mobile Application Hacker's Handbook
 The Mobile Application Hackers Handbook
The Mobile Application Hackers Handbook
mobile applications are not covered in the context of this book; however we highly recommend The Web Application Hacker's. Handbook
 The Mobile Application Hackers Handbook
The Mobile Application Hackers Handbook
Using iTunes you can download applications from the App Store and synchronize Figure 2.4 summarizes this process courtesy of the iOS Hackers Handbook.
 Android Hackers Handbook PDF
Android Hackers Handbook PDF
ranging from app security to platform security (especially Android)
 The Web Application Hackers Handbook: Discovering and
The Web Application Hackers Handbook: Discovering and
21 févr. 2007 The web application hacker's handbook : discovering and exploiting security flaws / Dafydd Stut- tard Marcus Pinto. p. cm. Includes index.
 The mobile application hackers handbook
The mobile application hackers handbook
Common Mobile Application Functions. 3. Benefits of Mobile Applications. 4. Mobile Application Security. 4. Key Problem Factors.
 The Web Application Hackers Handbook: Finding and Exploiting
The Web Application Hackers Handbook: Finding and Exploiting
%20Marcus%20Pinto%20-%20The%20web%20application%20hacker's%20handbook_%20finding%20and%20exploiting%20security%20flaws-Wiley%20(2011).pdf
 The Web Application Hackers Handbook
The Web Application Hackers Handbook
21 févr. 2007 Dafydd Stuttard. Marcus Pinto. The Web Application. Hacker's Handbook. Discovering and Exploiting Security Flaws. Wiley Publishing Inc.
 The Antivirus Hackers Handbook
The Antivirus Hackers Handbook
If this book refers to media such as a CD or DVD that is not included in the version you purchased you may download this material at http://booksupport.wiley.
 The Web Application Hackers Handbook
The Web Application Hackers Handbook
6 juil. 2011 The Web Application Hacker's Handbook: Finding and Exploiting ... with mobile applications that are accessed using a smartphone or tablet.
 The Mac Hackers Handbook
The Mac Hackers Handbook
Charlie Miller. Dino A. Dai Zovi. The Mac® Hacker's. Handbook nm /Applications/Safari.app/Contents/MacOS/Safari
 Searches related to the mobile application hacker+s handbook pdf PDF
Searches related to the mobile application hacker+s handbook pdf PDF
anApplication 204UnderstandingtheSecurityModel 206CodeSigning 206DiscoveredVulnerabilities 210UnderstandingPermissions 212InspectingtheAndroidPermissionModel 212ProtectionLevels 216ApplicationSandbox 219FilesystemEncryption 221GenericExploitMitigationProtections 222RootingExplained 226RootingObjectives 226RootingMethods
What is the mobile application hacker's Handbook?
The Mobile Application Hacker's Handbook is a comprehensive guide to securing all mobile applications by approaching the issue from a hacker's point of view. Heavily practical, this book provides expert guidance toward discovering and exploiting flaws in mobile applications on the iOS, Android, Blackberry, and Windows Phone platforms.
Who is the author of hacker handbooks?
Sommers is the lead author on Hacker handbooks, all published by Bedford/St. Martin’s, and is coauthor of Fields of Reading, Tenth Edition (2013). If playback doesn't begin shortly, try restarting your device.
Where can I find information about mobile application hackers?
The companion website for this book at www.mobileapphacker.com, which you can also link to from www.wiley.com/go/mobileapplicationhackers, contains several resources that you will find useful in the course of mastering the tech-niques we describe and using them to attack actual applications.
When should I read the mobile application ECU-Rity book?
If you are new to mobile application secu-rity, it is recommended that you read the book from start to finish, acquiring the knowledge and understanding to tackle later chapters. This can be applied to the relevant chapters for each mobile platform, or the entirety of the book.
Android
Hacker"s Handbook
f? rs.indd 01:50:14:PM 02/28/2014 Page ii f? rs.indd 01:50:14:PM 02/28/2014 Page iiiJoshua J. Drake
Pau Oliva Fora
Zach Lanier
Collin Mulliner
Stephen A. Ridley
Georg Wicherski
Android
Hacker"s
Handbook
f? rs.indd 01:50:14:PM 02/28/2014 Page ivAndroid
Hacker"s Handbook
Published by
John Wiley & Sons, Inc.
10475 Crosspoint Boulevard
Indianapolis, IN 46256
www.wiley.com Copyright © 2014 by John Wiley & Sons, Inc., Indianapolis, IndianaISBN: 978-1-118-60864-7
ISBN: 978-1-118-60861-6 (ebk)
ISBN: 978-1-118-92225-5 (ebk)
Manufactured in the United States of America
10 9 8 7 6 5 4 3 2 1
No part of this publication may be reproduced, stored in a retrieval system or transmitted in any form or by any means,
electronic, mechanical, photocopying, recording, scanning or otherwise, except as permitted under Sections 107 or
108 of the 1976 United States Copyright Act, without either the prior written permission of the Publisher, or autho-
rization through payment of the appropriate per-copy fee to the Copyright Clearance Center, 222 Rosewood Drive,
Danvers, MA 01923, (978) 750-8400, fax (978) 646-8600. Requests to the Publisher for permission should be addressed
to the Permissions Department, John Wiley & Sons, Inc., 111 River Street, Hoboken, NJ 07030, (201) 748-6011, fax (201)
748-6008, or online at http://www.wiley.com/go/permissions.
Limit of Liability/Disclaimer of Warranty: The publisher and the author make no representations or warranties with
respect to the accuracy or completeness of the contents of this work and speci? cally disclaim all warranties, including
without limitation warranties of ? tness for a particular purpose. No warranty may be created or extended by sales or
promotional materials. The advice and strategies contained herein may not be suitable for every situation. This work
is sold with the understanding that the publisher is not engaged in rendering legal, accounting, or other professional
services. If professional assistance is required, the services of a competent professional person should be sought.
Neither the publisher nor the author shall be liable for damages arising herefrom. The fact that an organization or
Web site is referred to in this work as a citation and/or a potential source of further information does not mean that
the author or the publisher endorses the information the organization or Web site may provide or recommendations
it may make. Further, readers should be aware that Internet Web sites listed in this work may have changed or disap-
peared between when this work was written and when it is read.For general information on our other products and services please contact our Customer Care Department within the
United States at (877) 762-2974, outside the United States at (317) 572-3993 or fax (317) 572-4002.Wiley publishes in a variety of print and electronic formats and by print-on-demand. Some material included with
standard print versions of this book may not be included in e-books or in print-on-demand. If this book refers to media
such as a CD or DVD that is not included in the version you purchased, you may download this material at
http:// booksupport.wiley.com . For more information about Wiley products, visit www.wiley.com.Library of Congress Control Number:
2013958298
Trademarks: Wiley and the Wiley logo are trademarks or registered trademarks of John Wiley & Sons, Inc. and/or
its af? liates, in the United States and other countries, and may not be used without written permission. Android is a
trademark of Google, Inc. All other trademarks are the property of their respective owners. John Wiley & Sons, Inc.,
is not associated with any product or vendor mentioned in this book. v f? rs.indd 01:50:14:PM 02/28/2014 Page v Joshua J. Drake is a Director of Research Science at Accuvant LABS. Joshua focuses on original research in areas such as reverse engineering and the analy- sis, discovery, and exploitation of security vulnerabilities. He has over 10 years of experience in the information security ? eld including researching Linux security since 1994, researching Android security since 2009, and consulting with major Android OEMs since 2012. In prior roles, he served at Metasploit and VeriSign"s iDefense Labs. At BlackHat USA 2012, Georg and Joshua demon- strated successfully exploiting the Android 4.0.1 browser via NFC. Joshua spoke at REcon, CanSecWest, RSA, Ruxcon/Breakpoint, Toorcon, and DerbyCon. He won Pwn2Own in 2013 and won the DefCon 18 CTF with the ACME Pharm team in 2010.Pau Oliva Fora
is a Mobile Security Engineer with viaForensics. He has pre- viously worked as R+D Engineer in a wireless provider. He has been actively researching security aspects on the Android operating system since its debut with the T-Mobile G1 on October 2008. His passion for smartphone security has manifested itself not just in the numerous exploits and tools he has authored but in other ways, such as serving as a moderator for the very popular XDA- Developers forum even before Android existed. In his work, he has provided consultation to major Android OEMs. His close involvement with and observa- tion of the mobile security communities has him particularly excited to be a part of pulling together a book of this nature. Zach Lanier is a Senior Security Researcher at Duo Security. Zach has been involved in various areas of information security for over 10 years. He has been conducting mobile and embedded security research since 2009,About the Authors
f? rs.indd 01:50:14:PM 02/28/2014 Page vi ranging from app security, to platform security (especially Android), to device, network, and carrier security. His areas of research interest include both offensive and defensive techniques, as well as privacy-enhancing technologies. He has presented at various public and private industry conferences, such as BlackHat, DEFCON, ShmooCon, RSA, Intel Security Conference, AmazonZonCon, and more.
Collin Mulliner is a postdoctoral researcher at Northeastern University. His main interest lies in security and privacy of mobile and embedded systems with an emphasis on mobile and smartphones. His early work dates back to 1997, when he developed applications for Palm OS. Collin is known for his work on the (in) security of the Multimedia Messaging Service (MMS) and the Short Message Service (SMS). In the past he was mostly interested in vulnerability analysis and offensive security but recently switched his focus the defensive side to develop mitigations and countermeasures. Collin received a Ph.D. in computer science computer science at UC Santa Barbara and FH Darmstadt. Ridley (as his colleagues refer to him) is a security researcher and author with more than 10 years of experience in software development, software security, and reverse engineering. In that last few years Stephen has presented his research and spoken about reverse engineering and software security on every continent (except Antarctica). Previously Stephen served as the Chief Information Security Of? cer of Simple.com, a new kind of online bank. Before that, Stephen was senior researcher at Matasano Security and a founding member of the Security and Mission Assurance (SMA) group at a major U.S defense contractor, where he specialized in vulnerability research, reverse engineering, and "offensive software" in support of the U.S. Defense and Intelligence community. At pres- ent, Stephen is principal researcher at Xipiter (an information security R&D ? rm that has also developed a new kind of low-power smart-sensor device). Recently, Stephen and his work have been featured on NPR and NBC and in Wired, the Washington Post, Fast Company, VentureBeat, Slashdot, The Register, and other publications. Georg Wicherski is Senior Security Researcher at CrowdStrike. Georg particularly enjoys tinkering with the low-level parts in computer security; hand-tuning custom-written shellcode and getting the last percent in exploit reliability stable. Before joining CrowdStrike, Georg worked at Kaspersky and McAfee. At BlackHat USA 2012, Joshua and Georg demonstrated successfully exploiting the Android 4.0.1 browser via NFC. He spoke at REcon, SyScan, BlackHat USA and Japan, 26C3, ph-Neutral, INBOT, and various other confer- ences. With his local CTF team 0ldEur0pe, he participated in countless and won numerous competitions. vi About the Authors vii f? rs.indd 01:50:14:PM 02/28/2014 Page vii Rob Shimonski (www.shimonski.com) is a best-selling author and editor with over 15 years" experience developing, producing and distributing print media in the form of books, magazines, and periodicals. To date, Rob has successfully created over 100 books that are currently in circulation. Rob has worked for countless companies that include CompTIA, Microsoft, Wiley, McGraw Hill Education, Cisco, the National Security Agency, and Digidesign. Rob has over 20 years" experience working in IT, networking, systems, and security. He is a veteran of the US military and has been entrenched in security topics for his entire professional career. In the military Rob was assigned to a communications (radio) battalion supporting training efforts and exercises. Having worked with mobile phones practically since their inception, Rob is an expert in mobile phone development and security.About the Technical Editor
f? rs.indd 01:50:14:PM 02/28/2014 Page viii ix f? rs.indd 01:50:14:PM 02/28/2014 Page ixExecutive Editor
Carol Long
Project Editors
Ed Connor
Sydney Jones Argenta
Technical Editor
Rob Shimonski
Production Editor
Daniel Scribner
Copy Editor
Charlotte Kughen
Editorial Manager
Mary Beth Wake? eld
Freelancer Editorial Manager
Rosemarie Graham
Associate Director of Marketing
David MayhewMarketing ManagerAshley Zurcher
Business Manager
Amy Knies
Vice President and Executive
Group Publisher
Richard Swadley
Associate Publisher
Jim Minatel
Project Coordinator, Cover
Todd Klemme
Proofreaders
Mark Steven Long
Josh Chase, Word One
Indexer
Ron Strauss
Cover Designer
WileyCredits
Cover Image
The Android robot is reproduced or modi? ed from work created and shared by Google and used according to terms described in the Creative Commons3.0 Attribution License.
f? rs.indd 01:50:14:PM 02/28/2014 Page x xi f? rs.indd 01:50:14:PM 02/28/2014 Page xi I thank my family, especially my wife and son, for their tireless support and affection during this project. I thank my peers from both industry and academia; their research efforts push the boundary of public knowledge. I extend my gratitude to: my esteemed coauthors for their contributions and candid discus- sions, Accuvant for having the grace to let me pursue this and other endeavors, and Wiley for spurring this project and guiding us along the way. Last, but not least, I thank the members of #droidsec, the Android Security Team, and the Qualcomm Security Team for pushing Android security forward.Joshua J. Drake
I"d like to thank Iolanda Vilar for pushing me into writing this book and sup- porting me during all the time I"ve been away from her at the computer. Ricard and Elena for letting me pursue my passion when I was a child. Wiley and all the coauthors of this book, for the uncountable hours we"ve been working on this together, and specially Joshua Drake for all the help with my broken English. The colleagues at viaForensics for the awesome technical research we do together. And ? nally all the folks at #droidsec irc channel, the Android Security com- munity in G+, Nopcode, 48bits, and everyone who I follow on Twitter; without you I wouldn"t be able to keep up with all the advances in mobile security.Pau Oliva
Acknowledgments
xii Acknowledgments f? rs.indd 01:50:14:PM 02/28/2014 Page xii I would like to thank Sally, the love of my life, for putting up with me; my family for encouraging me; Wiley/Carol/Ed for the opportunity; my coauthors for sharing this arduous but awesome journey; Ben Nell, Craig Ingram, Kelly Lum, Chris Valasek, Jon Oberheide, Loukas K., Chris Valasek, John Cran, and Patrick Schulz for their support and feedback; and other friends who"ve helped and supported me along the way, whether either of us knows it or not.Zach Lanier
I would like to thank my girlfriend Amity, my family, and my friends and colleagues for their continued support. Further, I would like to thank my advi- sors for providing the necessary time to work on the book. Special thanks toJoshua for making this book happen.
Collin Mulliner
No one deserves more thanks than my parents: Hiram O. Russell, and Imani Russell, and my younger siblings: Gabriel Russell and Mecca Russell. A great deal of who (and what) I am, is owed to the support and love of my family. Both of my parents encouraged me immensely and my brother and sister never cease to impress me in their intellect, accomplishments, and quality as human beings. You all are what matter most to me. I would also like to thank my beautiful ? an- cée, Kimberly Ann Hartson, for putting up with me through this whole process and being such a loving and calming force in my life. Lastly, I would like to thank the information security community at large. The information security community is a strange one, but one I "grew up" in nonetheless. Colleagues and researchers (including my coauthors) are a source of constant inspiration and provide me with the regular sources of news, drama, and aspirational goals that keep me interested in this kind of work. I am quite honored to have been given the opportunity to collaborate on this text.Stephen A. Ridley
I sincerely thank my wife, Eva, and son, Jonathan, for putting up with me spending time writing instead of caring for them. I love you two. I thank Joshua for herding cats to make this book happen.Georg Wicherski
xiii f? rs.indd 01:50:14:PM 02/28/2014 Page xiiiIntroduction xxv
Chapter 1 Looking at the Ecosystem 1
Chapter 2 Android Security Design and Architecture 25Chapter 3 Rooting Your Device 57
Chapter 4 Reviewing Application Security 83
Chapter 5 Understanding Android"s Attack Surface 129 Chapter 6 Finding Vulnerabilities with Fuzz Testing 177 Chapter 7 Debugging and Analyzing Vulnerabilities 205Chapter 8 Exploiting User Space Software 263
Chapter 9 Return Oriented Programming 291
Chapter 10 Hacking and Attacking the Kernel 309
Chapter 11 Attacking the Radio Interface Layer 367Chapter 12 Exploit Mitigations 391
Chapter 13 Hardware Attacks 423
Appendix A Tool Catalog 485
Appendix B Open Source Repositories 501
Appendix C References 511
Index 523
Contents at a Glance
f? rs.indd 01:50:14:PM 02/28/2014 Page xiv xv ftoc.indd 09:50:43:PM 03/04/2014 Page xvIntroduction xxv
Chapter 1 Looking at the Ecosystem 1
Understanding Android"s Roots 1
Company History 2
Version History 2
Examining the Device Pool 4
Open Source, Mostly 7
Understanding Android Stakeholders 7
Google 8
Hardware Vendors 10
Carriers 12
Developers 13
Users 14
Grasping Ecosystem Complexities 15
Fragmentation 16
Compatibility 17
Update Issues 18
Security versus Openness 21
Public Disclosures 22
Summary 23
Chapter 2 Android Security Design and Architecture 25Understanding Android System Architecture 25
Understanding Security Boundaries and Enforcement 27Android"s Sandbox 27
Android Permissions 30
Looking Closer at the Layers 34
Android Applications 34
The Android Framework 39
Contents
xvi Contents ftoc.indd 09:50:43:PM 03/04/2014 Page xviThe Dalvik Virtual Machine 40
User-Space Native Code 41
The Kernel 49
Complex Security, Complex Exploits 55
Summary 56
Chapter 3 Rooting Your Device 57
Understanding the Partition Layout 58
Determining the Partition Layout 59
Understanding the Boot Process 60
Accessing Download Mode 61
Locked and Unlocked Boot Loaders 62
Stock and Custom Recovery Images 63
Rooting with an Unlocked Boot Loader 65
Rooting with a Locked Boot Loader 68
Gaining Root on a Booted System 69
NAND Locks, Temporary Root, and Permanent Root 70
Persisting a Soft Root 71
History of Known Attacks 73
Kernel: Wunderbar/asroot 73
Recovery: Volez 74
Udev: Exploid 74
Adbd: RageAgainstTheCage 75
quotesdbs_dbs21.pdfusesText_27[PDF] the national k 12 foreign language enrollment survey report 2018
[PDF] the national k 16 foreign language enrollment survey report
[PDF] the nature of code pdf download
[PDF] the netflix recommender system
[PDF] the neuroscience of joyful education
[PDF] the new c standard
[PDF] the new oxford picture dictionary (english spanish edition)
[PDF] the new oxford picture dictionary download
[PDF] the new oxford picture dictionary english chinese pdf
[PDF] the new oxford picture dictionary english spanish pdf free
[PDF] the new oxford picture dictionary monolingual english edition
[PDF] the new oxford picture dictionary spanish pdf
[PDF] the new school waitlist
[PDF] the new york times guide to the best 1
