 8086 Instruction Encoding-1 Encoding of 8086 Instructions ! 8086
8086 Instruction Encoding-1 Encoding of 8086 Instructions ! 8086
8086 Instruction Encoding-12. Examples (Cont'd) ! MOV instruction has seven possible formats. We will not discuss them all. MOV reg/memreg/mem ! This
 80x86 Instruction Encoding 8086 Instructions Encoding of 8086
80x86 Instruction Encoding 8086 Instructions Encoding of 8086
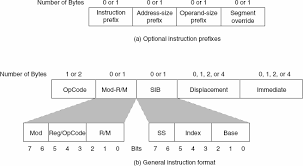
Encoding of 8086 Instructions. • 8086 instructions are encoded as binary numbers. • Instructions vary in length from 1 to 6 bytes. Note that many RISC
 Instruction Encoding
Instruction Encoding
• Additional notes in : Instruction Encoding Note. SYSC3006. 1. Page 2. Instruction Encoding. On the Intel 8086 an instruction is a sequence of 1..6 bytes. • A
 4- MACHINE LANGUAGE CODING 4-1THE INSTRUCTION SET
4- MACHINE LANGUAGE CODING 4-1THE INSTRUCTION SET
17 janv. 2018 The machine code instructions of the 8086 vary in the number of bytes used to encode them. Some instructions can be encoded with just 1 byte ...
 ASM86 LANGUAGE REFERENCE MANUAL
ASM86 LANGUAGE REFERENCE MANUAL
Encoding. 9809 FO. Operation op1. Emulator. Encoding. CO 19 FO op2. Execution ... 8086/8088 flags. (see Flags). 8087 Control word 6-110. 8087 Data types
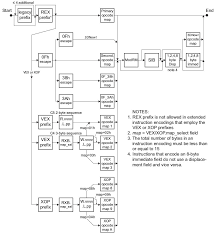 x86 Instruction Encoding
x86 Instruction Encoding
version of 8086 :-) – Page 4. 11 x86 ISA. ○ Insn set backwards-compatible to Intel 8086. • A hybrid CISC. • Little endian byte order. • Variable length ...
 adaptTo() 2020
adaptTo() 2020
30 sept. 2020 CVE-2019-8086 / XML eXternal Entity Injection. ▫ CVE-2019-8087 / XML ... encoding="utf-8"?><!DOCTYPE afData [<!ENTITY a SYSTEM "file:///etc ...
 Instructions Involve a Segment Register (SR-field) Encoding a
Instructions Involve a Segment Register (SR-field) Encoding a
The first byte of the program is stored at the lowest address. Page 2. 8086/8088MP. INSTRUCTOR: ABDULMUTTALIB A. H. ALDOURI. ٥٨.
 Multiple Choice Questions on 8086 Microprocessor
Multiple Choice Questions on 8086 Microprocessor
data encoding. ANSWER: C. 78. In 8086 Example for Non maskable interrupts are . A. TRAP. B. RST6.5. C. INTR. D. RST6.6. ANSWER: A. 79. In 8086 the overflow
 x86-64 encoding / viruses
x86-64 encoding / viruses
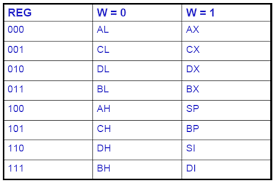
8 févr. 2021 (dedicated opcodes) pop ax … 6. Page 7. 8086 instruction encoding: two-arg. 1-byte opcode sometimes ModRM byte: 2-bit “mod” and. 3-bit register ...
 8086 Instruction Encoding-1 Encoding of 8086 Instructions ! 8086
8086 Instruction Encoding-1 Encoding of 8086 Instructions ! 8086
8086 Instruction Encoding-1. Encoding of 8086 Instructions ! 8086 Instructions are represented as binary numbers. Instructions require between 1 and 6 bytes.
 80x86 Instruction Encoding 8086 Instructions Encoding of 8086
80x86 Instruction Encoding 8086 Instructions Encoding of 8086
through x86-64 are backwardly compatible with the 8086. • We will look at 8086 encoding in detail 8086 instructions are encoded as binary numbers.
 Instructions Involve a Segment Register (SR-field) Encoding a
Instructions Involve a Segment Register (SR-field) Encoding a
8086/8088MP. INSTRUCTOR: ABDULMUTTALIB A. H. ALDOURI. ??. Ex: Encode the “block move” program and show how it would be stored in.
 Instruction Encoding
Instruction Encoding
Instruction Encoding. On the Intel 8086 an instruction is a sequence of 1..6 bytes. • A simple (and incomplete) model of an instruction is as follows.
 x86-64 encoding / viruses
x86-64 encoding / viruses
8 févr. 2021 8086 instruction encoding: two-arg. 1-byte opcode sometimes ModRM byte: 2-bit “mod” and. 3-bit register number (source or dest ...
 4- MACHINE LANGUAGE CODING 4-1THE INSTRUCTION SET
4- MACHINE LANGUAGE CODING 4-1THE INSTRUCTION SET
17 janv. 2018 The machine code instructions of the 8086 vary in the number of bytes used to encode them. Some instructions can be encoded with just 1 byte ...
 x86 Instruction Encoding
x86 Instruction Encoding
8086: 1978 16-bit CPU with 16-bit external data bus Insn set backwards-compatible to Intel 8086 ... Encoding escapes: different encoding syntax.
 8086 Programming
8086 Programming
23 oct. 2012 Instruction Encoding. How to encode instructions as binary values? Instructions consist of: • operation (opcode) e.g. MOV.
 Instruction format
Instruction format
The machine code instructions of the 8086 vary in the number of bytes used to encode them. Some instructions can be encoded with just 1 byte others can be done
 adaptTo() 2020
adaptTo() 2020
30 sept. 2020 CVE-2019-8086. 16. ? Exploitation hints. ? We can JSON-encode XXE payload to bypass a WAF*. ? In Java we can list directory content.
EUROPE'S LEADING AEM DEVELOPER CONFERENCE
28thÿ30thSEPTEMBER 2020
A Hacker's perspective on AEM applications securityMikhail Egorov, Security researcher & bug hunter
2 Intro whoami 3Security researcher & full-time bug hunter
https://bugcrowd.com/0ang3el https://hackerone.com/0ang3elConference speaker
https://www.slideshare.net/0ang3el https://speakerdeck.com/0ang3el whoami 4Toolset for AEM hacking
https://github.com/0ang3el/aem-hacker 5APSB19-48
APSB19-48
6 ence-manager/apsb19-48.htmlCVE-2019-8086 / XML eXternalEntity Injection
CVE-2019-8087 / XML eXternalEntity Injection
CVE-2019-8088 / JavaScript Code Injection
XML eXternalEntity (XXE) attacks
7Do we see the parsed XML?
General external entities
Parameter external entities
External DTD loading
XML eXternalEntity (XXE) attacks
8XML eXternalEntity (XXE) attacks
9 %xxe;XML eXternalEntity (XXE) attacks
10CVE-2019-8086
11GuideInternalSubmitServlet
@Service({Servlet.class}) @Properties({@Property( name = "sling.servlet.resourceTypes", value = {"fd/af/components/guideContainer"} ), @Property( name = "sling.servlet.methods", value = {"POST"} ), @Property( name = "sling.servlet.selectors", value = {"af.internalsubmit"} public class GuideInternalSubmitServletCVE-2019-8086
12CVE-2019-8086
13CVE-2019-8086
14XXE payload
CVE-2019-8086
15CVE-2019-8086
16Exploitation hints
We can JSON-encode XXE payload to bypass a WAF*
In Java we can list directory content
/proc/self/cwd * WAF ÿweb application firewallCVE-2019-8086
17JSON-encoding
data = ']>CVE-2019-8086
18CVE-2019-8086
19XXE payload
CVE-2019-8086
20CVE-2019-8086
21Exploitation requirements
There should be a node with
fd/af/components/guideContainerresource type onents/guideContainerAttacker should have a jcr:writeaccess
somewhereCVE-2019-8086
22Exploitation requirements
Only blind SSRF* for some versions
CVE-2019-8087
23WSDLInvokerServlet
@Service({Servlet.class}) @Properties({@Property( name = "sling.servlet.resourceTypes", value = {"fd/af/components/guideContainer"} ), @Property( name = "sling.servlet.selectors", value = {"af.wsdl"} ), @Property( name = "sling.servlet.methods", value = {"POST"} public class WSDLInvokerServletCVE-2019-8087
24CVE-2019-8087
25CVE-2019-8087
26WSDL example
CVE-2019-8087
27CVE-2019-8087
28Malicious xxe.wsdl
%dtd; %param1;CVE-2019-8087
29Malicious loot.dtd
">CVE-2019-8087
30CVE-2019-8087
31Exploitation requirements
There should be a node with
fd/af/components/guideContainerresource type onents/guideContainerAttacker should have a jcr:writeaccess
somewhereCVE-2019-8087
32Exploitation requirements
On some AEM versions WSDLInvokerServletis not
presentCVE-2019-8088
33GuideSubmitServlet
@Service({Servlet.class}) @Properties({@Property( name = "sling.servlet.resourceTypes", value = {"fd/af/components/guideContainer"} ), @Property( name = "sling.servlet.methods", value = {"POST"} ), @Property( name = "sling.servlet.selectors", value = {"af.submit", "af.agreement", "af.signSubmit"} public class GuideSubmitServlet extends SlingAllMethodsServlet {CVE-2019-8088
34CVE-2019-8088
35CVE-2019-8088
36CVE-2019-8088
37CVE-2019-8088
38CVE-2019-8088
39Sandboxed Rhino engine on some AEM versions
No RCE *
Sandbox allows network interactions
SSRF w/ ability to see the response
* RCE ÿRemote Code ExecutionCVE-2019-8088
40JS payload
rator.net');//CVE-2019-8088
41CVE-2019-8088
42CVE-2019-8088
43JS payload
CVE-2019-8088
44CVE-2019-8088
45CVE-2019-8088
46Exploitation requirements
There should be a node with
fd/af/components/guideContainerresource type onents/guideContainerAttacker should have a jcr:writeaccess
somewhereCVE-2019-8088
47Exploitation requirements
RCE or SSRF
APSB19-48
48Keep AEM up to date
nce-manager/apsb19-48.htmlBlock jcr:writeaccessfor anonymous user
Remove demo content (Geometrixx, WeRetail, )
49Thank you
@0ang3elquotesdbs_dbs12.pdfusesText_18[PDF] 8086 instruction format example
[PDF] 8086 instruction format pdf
[PDF] 8086 instruction set and assembler directives pdf
[PDF] 8086 instruction set opcodes pdf
[PDF] 8086 instruction set pdf
[PDF] 8086 instruction set pdf download
[PDF] 8086 instruction set pdf nptel
[PDF] 8086 instruction set slideshare
[PDF] 8086 kit lab manual
[PDF] 8086 microprocessor architecture and instruction set
[PDF] 8086 microprocessor architecture and pin diagram pdf
[PDF] 8086 microprocessor architecture and pin diagram ppt
[PDF] 8086 microprocessor architecture diagram
[PDF] 8086 microprocessor architecture explanation
